Risky Bulletin Newsletter
May 13, 2026
Risky Bulletin: RubyGems disables sign-ups after attack on staff
Written by

News Editor
This newsletter is brought to you by Knocknoc. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
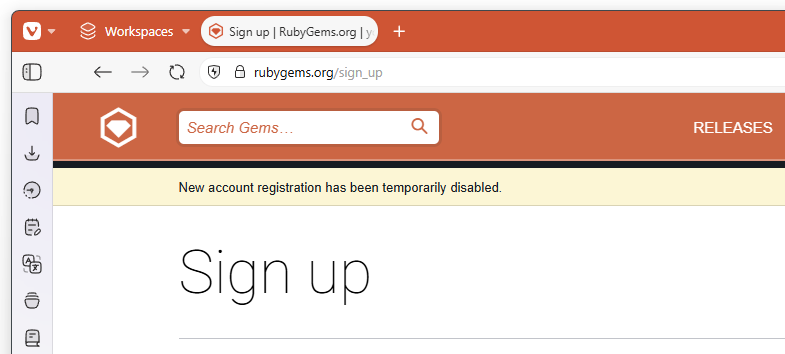
The RubyGems package repository has disabled new user sign-ups after a malicious attack on Monday targeted its engineers and staff.
Hundreds of malicious packages were published on Monday and then again on Tuesday.
The packages contained malicious code aimed at RubyGems developers. The code tried to execute cross-site scripting attacks and steal data from their systems.

The incident is unrelated to a major supply chain attack that was happening at the same time on the npm JavaScript package repository. That attack originated from the TanStack framework's packages and spread to more than 400 npm libraries in a matter of hours, but that one targeted developers and not npm staff.
Details are still unclear of what the attackers tried to steal from the RubyGems staff.
"The team has been on this for hours. More details to follow once we're through it," said Maciej Mensfeld, one of the members of the RubyGems security team.
RubyGems also reported getting hit by a DDoS attack, although, I'm inclined to believe this is just infosec gibberish terms semantics, and they're calling the flood of malicious packages a DDoS attack.
I don't think it was an actual DDoS. There's been a hacktivist group that has attacked FOSS projects like Ubuntu, Mastodon, and BlueSky, but they were busy attacking GoodReads for the past few days.
Risky Business Podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss why it makes even more sense for criminal organisations to adopt AI as compared to regular businesses.
Breaches, hacks, and security incidents
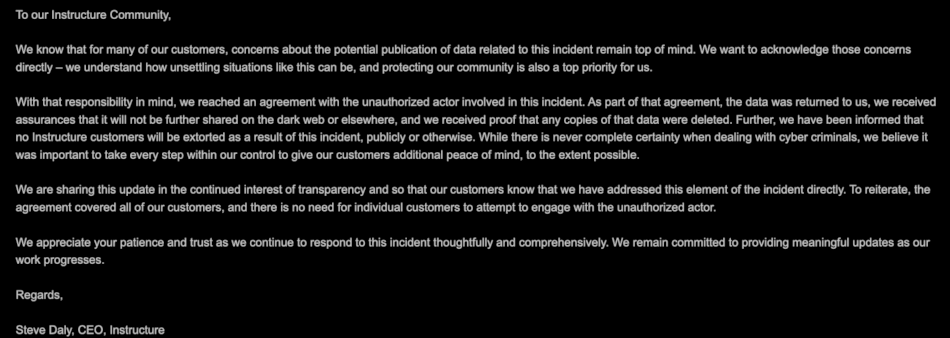
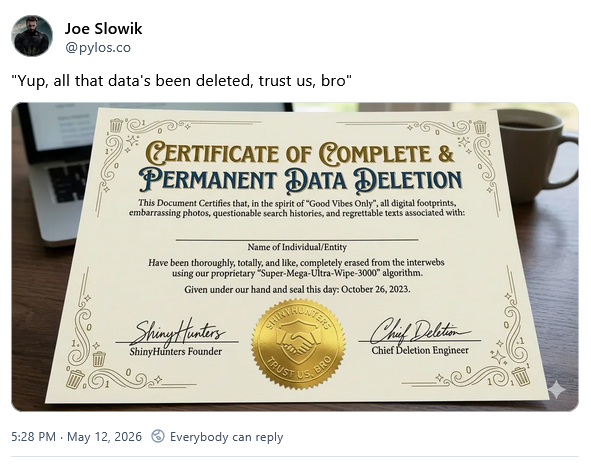
Instructure pays the ransom: edTech company Instructure has paid the hackers who took down its Canvas student management platform. The company emailed schools and colleges about the payment, before the platform was restored over the weekend. Almost 9,000 universities, schools, and school districts were impacted by the hack and couldn't access the platform during end-of-year exams. It's unknown how much Instructure paid. Its name was removed from the hackers' website, which usually happens when a ransom has been paid. Meanwhile, there's a very concerted effort to track the group via their blockchain payments, and the House Homeland Security Committee has also summoned the company's leadership to a meeting. [CalMatters // DataBreaches.net]
Skoda shop breach: Automaker Skoda says hackers exploited a vulnerability in its web store in Germany and likely accessed customer data. [h/t DD Forty]
Best Western discloses breach: Best Western International is notifying guests who stayed at its hotels of a security breach. The hotel chain says a hacker had access to its reservation systems for over six months between October and April this year. The company operates several hotel brands, such as Best Western, Sure Hotels, and WorldHotels. [/r/BestWestern]
UK fines water utility for negligence: The UK's ICO has fined South Staffordshire Water with almost £1 million for failing to detect hackers in its network for almost two years.
Nitrogen gang claims Foxconn hack: A ransomware attack has disrupted the activity of Foxconn's North American factories earlier this month. The company confirmed the incident after workers leaked some of its internal messages on social media last week. The Nitrogen ransomware group claimed the attack in a blog post on Tuesday. The group claims it stole 8TB of data, including confidential projects and chip drawings for Apple, Google, and NVIDIA orders. [DysruptionHub]
Ransomware disrupts West Pharmaceutical: A ransomware attack has disrupted the operations of a major manufacturer of pharmaceutical drug packaging. The incident took place last week and impacted West Pharmaceutical Services. The attack impacted West business operations globally. Manufacturing, shipping, and receiving operations have been restored at some locations, per an SEC filing. [DysruptionHub]
Hackers leak Vodafone data: The Lapsus$ hacking group has leaked some source code from EU telco Vodafone after the company refused to pay. [h/t Kevin Beaumont]
TanStack supply chain attack: The npm packages of the popular TanStack web development framework were compromised to deliver a self-propagating worm and credential stealers. TanStack npm packages were modified on Monday in a supply chain attack that quickly spread across the npm ecosystem. Almost 400 packages were compromised, including libraries from AI company Mistral and business automation giant UiPath. The incident is part of the Shai-Hulud worm infestation that has plagued the dev ecosystem since November. The destructive behavior is still there, and the worm now wipes systems where owners try to revoke or change stolen tokens. [Aikido Security // Endor Labs // JFrog // Mend // OpenSourceMalware // Safedep // Semgrep // Snyk // Socket Security // Step Security // TanStack post-mortem // Wiz]
General tech and privacy
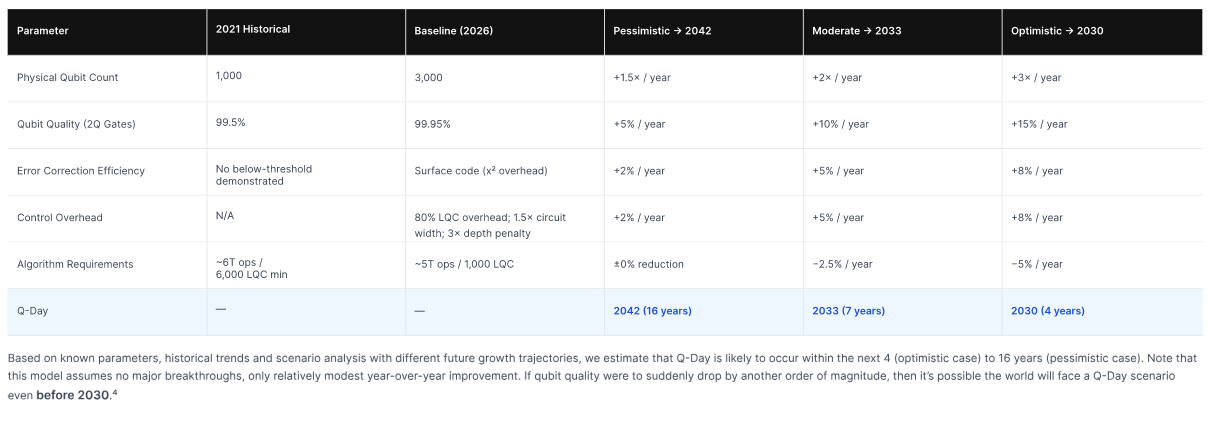
Q-Day gets closer: PQC expert group P11 has updated its Q-Day timeline to 2033, with optimistic and pessimistic scenarios at 2030 and 2042. The Q-Day term is used in the cryptography industry to refer to the moment a quantum computer breaks classic encryption algorithms. [Project Eleven]
Texas sues Netflix: The Texas Attorney General has sued Netflix for tracking user behavior without their consent. The lawsuit accuses Netflix of logging everything happening on its platform and selling user behavioral details to third-parties. The lawsuit seeks to stop the data collection and also order Netflix to disable the autoplay feature for children's profiles. [Texas AG]
OpenAI welcomes EU authorities: OpenAI has opened its new GPT-5.5-Cyber model to EU authorities. Anthropic has yet to do so, which has been pissing off EU officials for the past weeks. [Politico Europe]
OpenAI launches Daybreak: OpenAI has launched Daybreak, a project to deploy frontier AI models in popular software projects to detect and patch vulnerabilities. Daybreak will use multiple OpenAI models, including the company's new GPT-5.5-Cyber specialized model. The project is a direct response to Anthropic's Project Glasswing and Mythos cybersecurity model.
Europe is guilty too: While Israeli spyware and surveillance vendors have been getting all the bad rep lately, a new Human Rights Watch report has found that EU companies are just as guilty and are also selling surveillance tools to oppressive regimes. [Human Rights Watch]
Firefox to deliver weekly updates: Mozilla is now releasing weekly bug fixes for Firefox. The new release schedule went live with Firefox 151 last week. [Soeren Hentzschel]
Forza Horizon mega-leak: The Forza Horizon 6 game has already been pirated ahead of its official release after the game's developer pre-loaded an unencrypted version of the game on Steam. Playground Games later denied its actions even if they were plainly visible and threatened bans for players accessing the code. Stay classy! [Insider Gaming]
GitLab layoffs: GitLab is firing a bunch of staff because it's pivoting to "rewiring" its internal processes with AI. Good luck with that! This strategy worked wonders for Salesforce last year, I've heard.
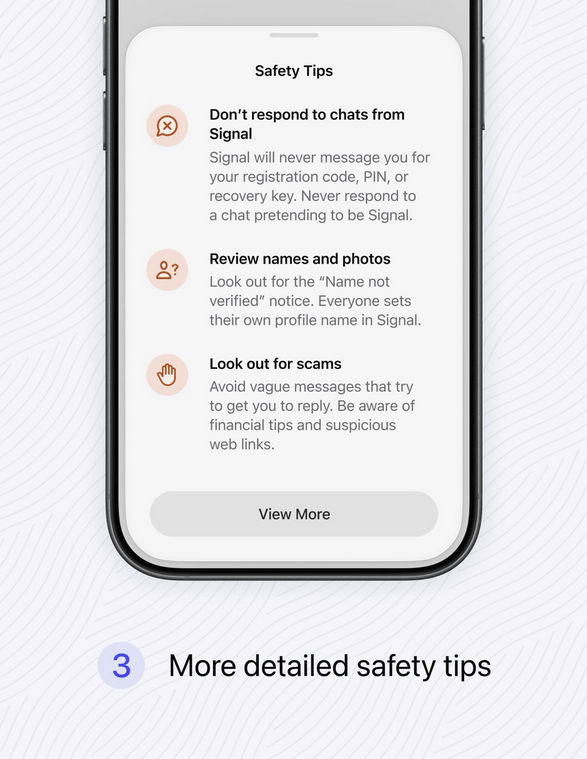
Signal rolls out new warnings: E2EE messenger Signal is rolling out new security alerts when accepting new chat requests. The new popups were designed to counter scams and attempts to phish registration, recovery, and PIN codes. [Signal on Mastodon]
Windows 11 Low Latency Profile: Microsoft is testing a new Windows 11 mode named "Low Latency Profile" that aims to boost performance for the OS by increasing the CPU frequency for a short period of time while apps are booting up. [Windows Central]
Microsoft Israel put under new leadership: Microsoft's Israel business unit was placed under the management of its French division because of rumors of "alleged unethical use of Azure by the [Israeli] Ministry of Defense." [Globes]
E2EE RCS arrives on Apple devices: Support for end-to-end encrypted RCS messaging has rolled out to Apple devices. Support has been added in iOS 26.5, released on Monday. E2EE RCS has been supported on Android for several years. The feature will allow Android and iPhone users to exchange encrypted messages between each other. The RCS technology was designed as a replacement for SMS. [ArsTechnica]
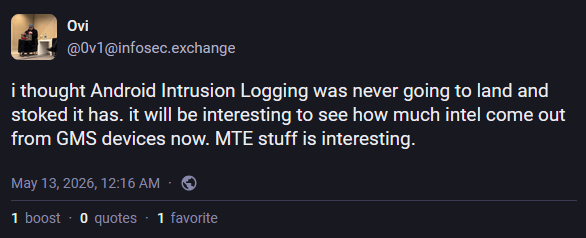
Android rolls out Intrusion Logging: Google is rolling out a new security feature to Android smartphones to help malware investigations. The new Intrusion Logging feature allows Android to create privacy-preserving forensics logs that don't expose a user's sensitive data. The feature was designed together with the security teams at Amnesty International and Reporters Without Borders. It is rolling out to all devices running the Android 16 December update and newer. [Amnesty // Google // Reporters Without Borders]
Google being shifty with its TOS: Redditors have caught Google secretly updating its Chrome terms of service to remove a line that guaranteed that local AI models won't send data to Google servers. That's now gone, meaning your local AI sends data to Google, so it's not that local. [Reddit]
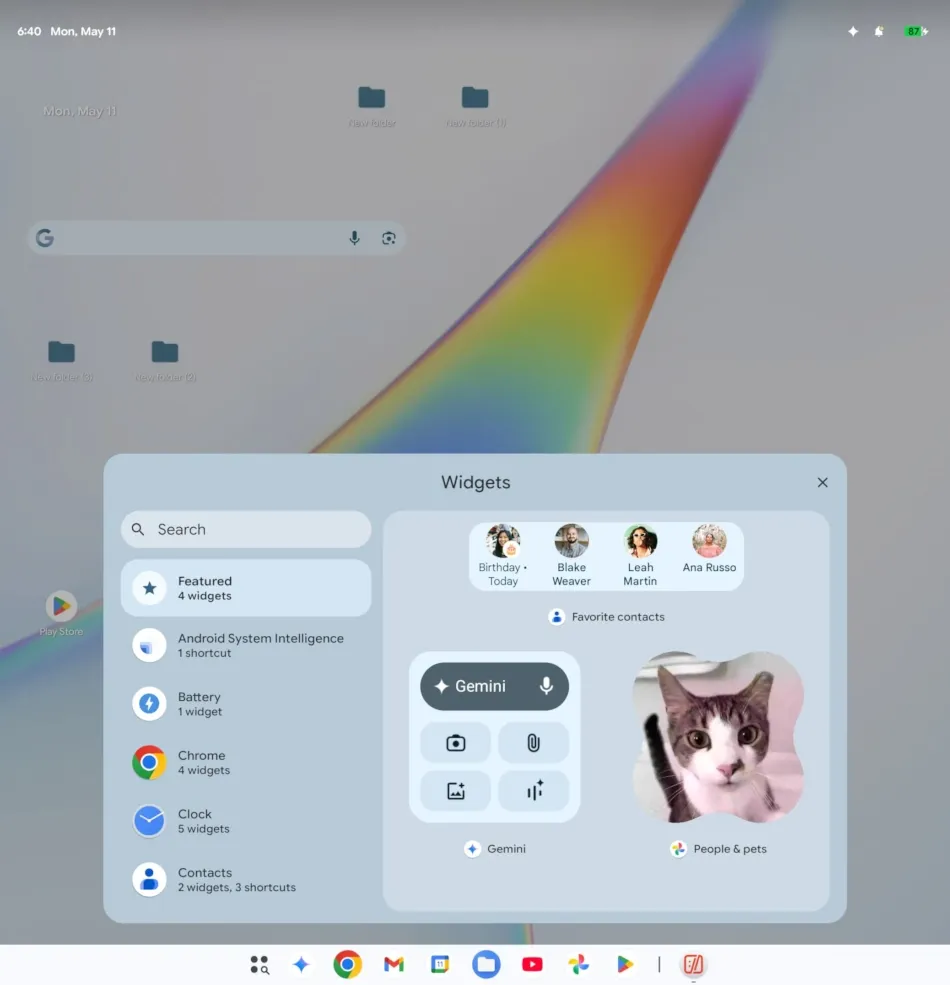
Google's Aluminium OS leaks: Leakers have shared the first videos of Aluminium OS, a version of Android designed for big screens. [AndroidAuthority]
Government, politics, and policy
EU kids social media ban expected this summer: The EU is expected to propose a bloc-wide social media ban for children as early as this summer. The new regulations will ban children under the age of 15 from creating new accounts on social media platforms. The EU is also considering banning social media platforms from using certain addictive design features such as infinite scrolling and autoplay. [Euronews]
SBOM for AI: Cybersecurity agencies from G7 countries released joint guidance on using a software bill of materials (SBOM) format for AI models.
DHS plans to spend big on hacking tools: The Department of Homeland Security plans to spend up to $100 million on Cellebrite hacking tools over the next five years. The tools will primarily be used by ICE. Cellebrite tools and software has been broadly deployed across US law enforcement last year. [FedScoop]
Kenya suspends Microsoft AI data center project: The Kenyan government halted talks on a Microsoft AI data center after it became clear that the project would consume half the country's daily power output. [Tom's Hardware]
Russia hints at a GitHub ban: Russia's internet watchdog has denied blocking access to GitHub after access to the site has deteriorated over the past week. Alexander Gorelkin, a Russian lawmaker behind the bans of western tech services in Russia, blamed the issues on Microsoft and claimed they could soon hit 100% error rates. The same exact pattern of Roskomnadzor denials and Gorelkin taunts also predated Russia's bans of YouTube and WhatsApp last year. [Meduza // Alexander Gorelkin]
Russians lose access to Claude: Russian users are reporting that they can't access their Claude AI accounts anymore. Experts believe the blocks are occurring because of a change to Anthropic's backend designed to block users from accessing its services using VPNs and distilling its models. [RBC]
Russia admits it can't block VPNs: The head of Russia's human rights council (ironic, I know) has become the first Kremlin official to admit for the first time that the Russian government can't block VPNs and if they did, their whole internal internet, known as the RuNet, would collapse. [RBC]
Sponsor section
In this Risky Business sponsor interview, Patrick Gray chats with Knocknoc CEO Adam Pointon about their Greynoise integration.
Arrests, cybercrime, and threat intel
Scam compound converted into deportation center: Cambodian authorities have converted the former Mango Park 2 scam compound into a pre-deportation center. [The Phnom Penh Post]
E-crime group used AI to discover zero-day: A cybercrime group used AI tools to discover a zero-day in a popular open-source, web-based system administration tool. The zero-day would have allowed the group to bypass 2FA during login operations if they had valid credentials. Google's security team says it detected the zero-day before it was used in mass attacks. [Google Cloud]
Ransomware groups resort to violence: An increasing number of ransomware and data extortion groups are now using threats of physical violence to intimidate victims to pay. Threats of violence have doubled last year, and are more prevalent in the US. Threats are being sent to staff, executives, and even ransomware negotiators. Most threats are being sent through Violence-as-a-Service communities. [BBC]
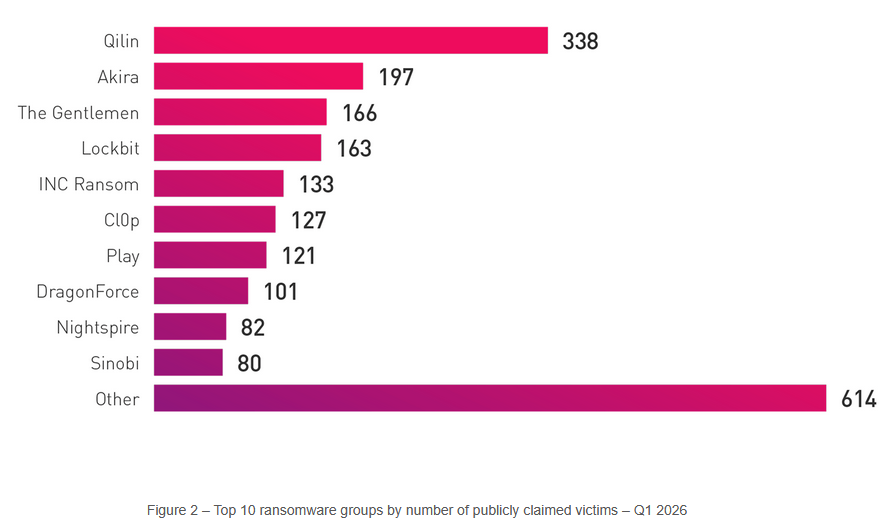
The Gentlemen RaaS gets hacked: The database and internal comms of The Gentlemen ransomware operation has been hacked and put up for sale on an underground hacking forum. The data was being offered for just $10,000 before the forum's admins took it down. The data is believed to have been stolen from the ransomware's web hosting provider, a shady service known as 4VPS. [BankInfoSecurity]
Cloudflare's shady role in the Ubuntu DDoS attacks: Security researcher Davi Ottenheimer explains Cloudflare's shady tactics of monetarily profiting from fronting for free the DDoS booter service that attacked Canonical, until Canonical turned around and paid Cloudflare a shit ton of money to protect it from the same attacks. Never change, Cloudflare! Maybe, in 2046, some of these useless law enforcement agencies will get their heads out of their asses and investigate your executives for once. [FlyingPenguin]
Mr_Rot13 targets cPanel: A threat actor tracked as Mr_Rot13 is exploiting a recent cPanel vulnerability to hack cloud environments and plant the Filemanager backdoor. [QiAnXin]
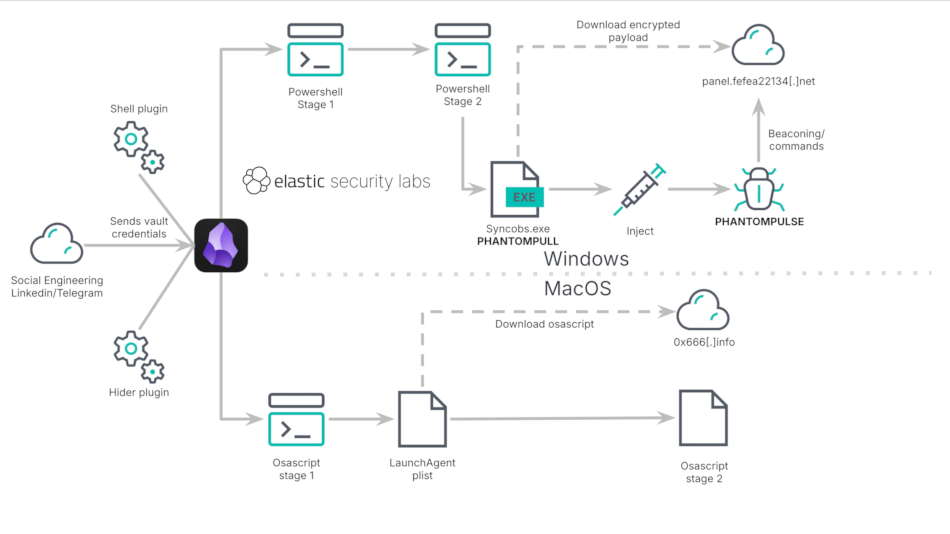
Obsidian app abuse: A threat actor is using the Obsidian note-taking app to execute malicious code on a victim's system in a campaign that targets the crypto and financial sectors. The final payload in these attacks is PhantomPulse, which appears to be an AI-generated Windows RAT. macOS users are only infected with a malicious AppleScript. [Elastic]
Malware technical reports
TrickMo variant: Mobile security firm ThreatFabric has found a new version of the TrickMo Android banking trojan. This new version uses The Open Network (TON) as its command-and-control channel in the early phases of the infection to avoid security solutions. [ThreatFabric]
crpx0 ransomware: There's a new ransomware strain in town targeting enterprises with malspam campaigns. [Aryaka]
The Gentlemen ransomware: There's a The Gentlemen affiliate using the EtherRAT as an entry point and delivery system for their ransomware. [The DFIR Report]
Sponsor section
In this product demo, Knocknoc CEO Adam Pointon walks Patrick Gray through the Knocknoc secure access platform. Knocknoc is a platform that restricts network and service availability to authenticated users via existing network security equipment. Users don't need to install an agent. It also has an identity-aware proxy component that supports web applications and RDP.
APTs, cyber-espionage, and info-ops
Seedworm breaches South Korean electronics maker: Iranian state-sponsored hackers breached a major South Korean electronics maker. The intrusion took place in February and lasted for a week. It was part of a sprawling cyber-espionage campaign that breached at least eight other organizations across the world. Symantec didn't name the company but linked the attacks to a group known as Seedworm and MuddyWater. [Symantec]
Vulnerabilities, security research, and bug bounty
Unpatched ipTIME RCE: Attackers can take over ipTIME home routers via the protocol used by their ISP to manage the devices. The attack does not require authentication and targets the CWMP protocol, also known as TR-069. It remains unfixed after the vendor did not reply to security researchers. [SSD Disclosure]
Unpatched ATutor bugs: Poland's CERT has found two XSS bugs in the ATutor LMS, which won't get patched because the project has been abandoned for eight years now. [CERT-PL]
Mythos and curl: The curl project's creator, Daniel Stenberg, says Mythos found five bugs in the curl code, with three being false positives, one being a plain bug, while only one was an actual security issue. [Daniel Stenberg]
"The single confirmed vulnerability is going to end up a severity low CVE planned to get published in sync with our pending next curl release 8.21.0 in late June. The flaw is not going to make anyone grasp for breath. All details of that vulnerability will of course not get public before then, so you need to hold out for details on that."
AI FI attack: Security firm Raelize used Claude to automate a fault injection attack and bypass Secure Boot, which appears to be "the first publicly-documented AI-driven Fault Injection attack." [Raelize]
New GhostLock technique: Security researcher Kim Dvash has discovered GhostLock, a new technique that locks access to files indefinitely inside Windows networks. The technique relies on Windows APIs and can be exploited from a low-privileged Windows domain user's account with access to a normal SMB share. GhostLock doesn't use encryption, doesn't write on disk, and produces zero signals for normal EDRs. [Website // GitHub PoC // Paper]
OverDoS vulnerability: A vulnerability in the n8n AI automation server can allow unauth remote attackers to exhaust its memory and deny service to legitimate processes. This is tracked as CVE-2026-42236 and nicknamed OverDoS. [Checkmarx]
Dead.Letter vulnerability: XBOW's AI found an unauth RCE in Exim. The bug is being called Dead.Letter and tracked as (CVE-2026-45185). Patches are out. [XBOW // Exim]
The Meari catastrophe: There are more than 1.1 million baby monitors, pet cams, and doorbell cameras that are leaking their feeds via a public MQTT broker. All are from Meari, a maker of white-label hardware products. The devices can all be enumerated via an API endpoint using the same hardcoded key that you can find embedded in any of the company's Android apps. [Sammy Azdoufal]
Patch Tuesday: Yesterday was the May 2026 Patch Tuesday. We had security updates from Adobe, Apple, Microsoft, Intel, AMD, SAP, IBM, HPE, Dell, ChromeOS, Tails, Firefox, Fortinet, Ivanti, Supermicro, Palo Alto Networks, Juniper, Synology, TP-Link, Kubernetes, Zoom, Exim, dnsmasq, ABB, Schneider Electric, and Siemens. Other projects and companies like Android, Cisco, Chrome, WhatsApp, Samsung, Qualcomm, AWS, WatchGuard, cPanel, Apache HTTPD, Apache Camel, Thunderbird, Axis, and ASUS released security updates earlier this month.
Researcher drops new Windows zero-days: A security researcher dropped two Windows zero-days minutes after Microsoft released this month's Patch Tuesday. The two zero-days include a privilege escalation bug named GreenPlasma and a BitLocker bypass bug named YellowKey. The same researcher, going by the nickname of Nightmare Eclipse, also dropped the BlueHammer and RedSun zero-days last month.
Infosec industry
Threat/trend reports: Binance, Canada's OIC, Check Point, Google Cloud, Hiscox, Kaspersky, and Sophos have recently published reports and summaries covering various threats and infosec industry trends.
New tool—LUKSbox: Hardware security firm PentHertz has open-sourced LUKSbox, a Rust-based encrypted-container that you can use to store sensitive files in the cloud without exposing them to the host.
CYBERWARCOM 2025 videos: Talks from the CYBERWARCOM 2025 security conference, which took place last November, are available on YouTube.
Risky Business podcasts
In this episode of Risky Business Features, James Wilson chats with Niels Provos about his research into using older AI models to successfully hunt for 0day vulnerabilities.
