Risky Bulletin Newsletter
May 06, 2026
Risky Bulletin: Extremely targeted supply chain attack hits DAEMON Tools
Written by

News Editor
This newsletter is brought to you by PortSwigger. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
A supply chain attack is currently ongoing on the website of DAEMON Tools, a popular app for burning CDs and DVDs, and for creating bootable USB drives.
DAEMON Tools installers have been shipping with a backdoor since at least April 8. The installers were signed with the vendor's legitimate certificate, suggesting deep access to the AVB Disc Soft's internal network and processes.
The backdoor triggers every time the user runs their PC, collects data about the host, and uploads it to a remote server. Collected data includes the machine's MAC address, hostname, system locale, DNS domain name, and a list of active processes and installed software.
The collected data is enough to help attackers identify what kind of system they infected.
The threat actor behind the hack seems to be interested in only a few selected systems, where it deploys a more powerful second-stage payload in the form of the QUIC RAT.
Security firm Kaspersky has seen several thousands of infections but the second payload was deployed only on a dozen of systems at government, scientific, manufacturing and retail organizations in Russia, Belarus and Thailand.
While Kaspersky did not attribute the attack, it said it found evidence that this may be the work of a Chinese-speaking threat actor.
The DAEMON Tools compromise is eerily similar to what happened last year at Notepad++, when a Chinese APT hacked a popular software vendor to go after high-value targets in select networks for espionage purposes.
This has been the M.O. of Chinese hackers for several years now, dating as far back as 2017, when they also hacked Avira's CCleaner app in a similar way, and again, to target only high-profile CCleaner users inside extremely high-value networks.
Although, my theorizing on this topic is a little bit too early, as Kaspersky has not even attributed the hack yet, as they graciously explained in their blog post.
"This manner of deploying the backdoor to a small subset of infected machines clearly indicates that the attacker had intentions to conduct the infection in a targeted manner. However, their intent – whether it is cyberespionage or ‘big game hunting’ – is currently unclear."
Risky Business Podcasts
In this edition of Between Two Nerds, Two Nerds Tom Uren and The Grugq discuss the breakdown of cyber norms. What would have been an unthinkable cyber operation just a few years ago is now a regular occurrence.
Breaches, hacks, and security incidents
Instructure hack: K-12 edtech platform Instructure has confirmed a security breach after the ShinyHunters group listed the company on its leak site last week. [DataBreaches.net]
The Foxconn mystery: Foxconn's Wisconsin plant, its main US production line, has had "networking issues" since last Friday. It's unclear if this is a cybersecurity incident for now, but worthy to keep an eye on. [DysruptionHub]
X user tricks Grok and steals $200k: A Twitter user tricked the Grok and Bankrbot AI agents into sending them $200,000 in crypto tokens. The user wrote the malicious instructions in Morse code to bypass the two agents' safety features. The user deleted their Twitter account after the transaction went through. [Cryptopolitan]
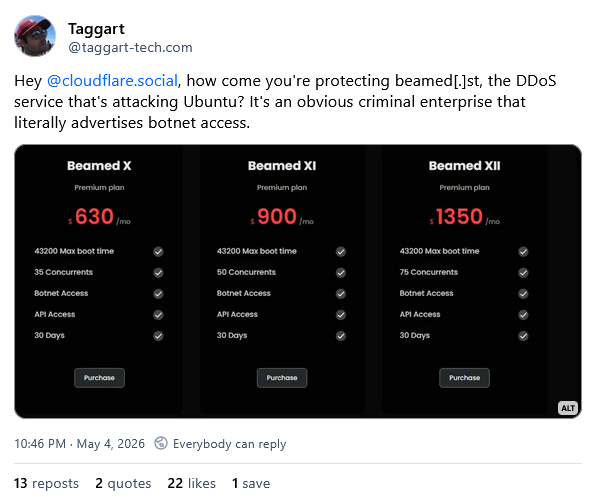
Canonical DDoS attacks are still ongoing: The DDoS attacks against Canonical's server infrastructure are still ongoing, which means you still can't install Ubuntu thanks to some s***ty hacktivist group and their DDoS-for-hire service.
General tech and privacy
Notepad++ warns users over clone: The Notepad++ team has warned users of a clone website/project claiming to bring the app to macOS.
Chrome deploys 4GB AI model: Google is deploying a 4GB AI model to all Chrome installs. The model is installed without consent, is not visible in the browser's settings, and removing it will reinstall it later. The model contains weights for Google's Gemini Nano feature that the company has recently added to Chrome. [That Privacy Guy]
Podslop: Almost 40% of newly published podcasts are now AI-generated in what the podcast industry is calling podslop. [Bloomberg]
Utah's dumb VPN law goes into effect: A Utah law has entered into effect this week that aims to hold websites liable if a Utah resident accesses their content via a VPN in order to avoid age verification checks. [EFF]
US forgets where its border ends: The DHS demanded from Google the personal data, activity, and geolocation information on a Canadian citizen who criticized ICE and President Trump after the killing of Renee Good and Alex Pretti. [Wired]
FTC bans Kochava from selling geolocation data: The US Federal Trade Commission has settled with data broker Kochava and barred the company from selling precise geolocation data without explicit user consent. The ban also applies to Kochava subsidiary Collective Data Solutions (CDS). The FTC sued Kochava in 2022 for selling geolocation data that exposed visits to sensitive locations, such as healthcare providers.
Police can be tracked via BLE devices: Criminal groups can track the precise location of police officers that wear bodyworn cameras and carry Bluetooth-capable tasers. Devices sold by Axon do not employ MAC address randomization, allowing threat actors to keep track of their precise movements. Mobile apps and a mesh of Bluetooth scanners can be used to create a live map of cops in a city. The company has been notified but officers will need new hardware to be fully protected. [ABC]

Government, politics, and policy
Australia creates Cyber Incident Review Board: The Australian government has created a special board to investigate cybersecurity incidents. The Cyber Incident Review Board will conduct no-fault, post-incident reviews of major cyberattacks to help organizations learn and avoid similar incidents. The board is modeled after the Cyber Safety Review Board, which the Trump administration disbanded in January 2025. The first board will have seven members and will be chaired by Narelle Devine, Global CISO at Telstra. [CyberDaily]
Mythos comes to save Europe: EU officials would like you to know they have been blessed by the AI gods and now have access to Anthropic's Mythos agent. [Reuters]
New CISA favorite: A former IBM cybersecurity executive has emerged as a favorite for the CISA Director role. Tom Parker's name has been rumored as the Trump administration's next candidate for the CISA top job. He will replace Sean Plankey, who withdrew his name from consideration last month after failing to secure a Congress vote for more than a year. [NextGov]
CISA prepares for war: CISA launched a new project this week to help critical infrastructure operators defend their networks in the case of an armed conflict. The CI Fortify project is designed to help operators defend against destructive attacks and to operate without an internet connection. The project encourages operators to isolate networks and have recovery plans in place.
DHS staff used insecure phones: The DHS Office of Intelligence and Analysis failed to secure employee phones, exposing them and their data to malware and data theft. Devices did not use recommended security settings and employees were allowed to install third-party apps. An audit found that employees installed VPNs, mobile games, and private messengers without authorization. The DHS blamed the misconfiguration of its mobile fleet on the mean, evil Biden and the Democrats. [UPI // DHS OIG, PDF]
US pulls the rug on AI companies: The Trump administration is working on a policy that would limit the ability of tech companies to dictate how their technology is used by the US government. Officials started working on the policy after AI companies said they'd work with the government only if their tools were used for "lawful purposes." [NextGov]
White House wants oversight over AI models: The Trump administration is considering introducing government oversight over the release of new AI models. The new rules are expected to arrive with a new executive order this month. The oversight would be a complete reversal of the Trump administration initial noninterventionist approach to AI regulation. The White House rescinded Biden-era AI rules shortly after President Trump was sworn in. Anthropic, Google, Microsoft, OpenAI, and xAI have already agreed to grant the US Commerce Department early access to their models. [Axios // NYT]
Sponsor section
In this Risky Business sponsor interview, James Wilson talks with James Kettle and Daf Stuttard from PortSwigger about the incredible research James will unveil at Black Hat US this July, and how that research will be productised into Burp Suite.
Arrests, cybercrime, and threat intel
Sri Lanka raids scam center: Sri Lankan authorities have arrested 37 Chinese nationals following a raid on a scam center in the capital Colombo. This is the third scam center raided by authorities in the last two months. They also detained 152 foreign nationals running a scam operation out of a hotel in April and another 135 in March. Most were Chinese nationals. [The Straits Times]
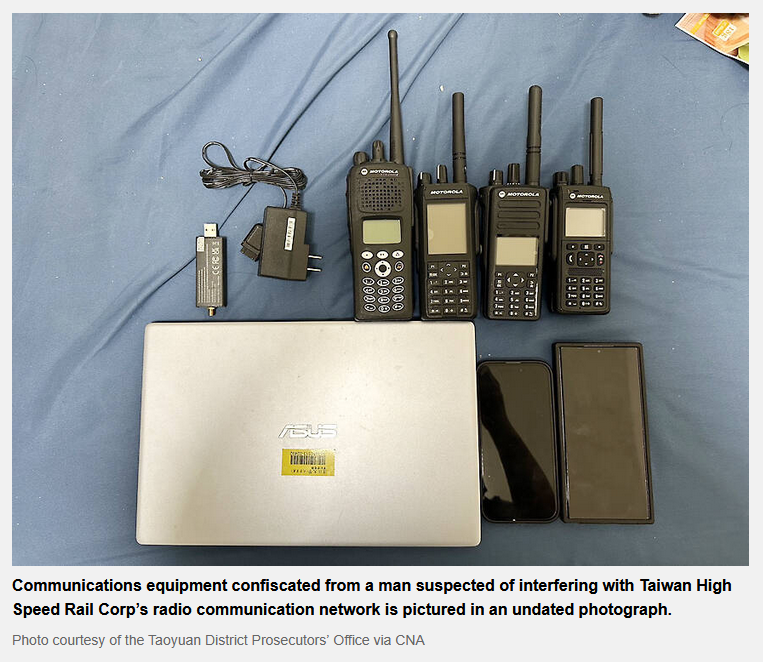
Taiwan arrests railway hacker: Taiwanese police have detained a 23-year-old student who hacked the radio network of the country's railway network. The hack took place on April 5 and caused at least three high-speed rail trains to activate their emergency brakes. The student, only identified as Lin, was released on bail. He faces up to 10 years in prison. [Taipei Times]
VOIP server hacker extradited: A Romanian national was extradited to the US to face charges related to a complex banking fraud scheme. Gavril Sandu hacked into VOIP servers and deployed automated scripts that contacted Americans. The scheme posed as banks and financial institutions and collected credit card details and PINs from victims. Sandu and his co-conspirators created copies of the cards with the stolen data and emptied bank accounts at ATMs. He was arrested in Romania in January but the scheme dates back to the late 2000s.
Karakurt member sentenced to prison: A Latvian national was sentenced to 8.5 years in prison for ransomware attacks. Deniss Zolotarjovs was a member of the Karakurt gang. He was involved in 54 attacks, including on a government entity whose 911 system was forced offline. He also targeted hospitals and deliberately used children’s health information for extortion.
Two SMS blasters arrested in Thailand: Thai officials have arrested two Chinese nationals last month for driving with an SMS blaster around the country's capital Bangkok. The fake cell tower was allegedly hidden inside the car's front passenger footwell. The device was detected by local telcos a month earlier after it interfered with their signals in populated areas. [CommsRisk]

FinFisher case stalls in Germany: The legal case filed by the Munich prosecutor's office against German spyware maker FinFisher for selling surveillance tools to Turkish intelligence agencies without approval has stalled for three years now. [h/t Andre Meister]
Dutch sentenced to prison for stolen data: A Dutch man has been sentenced to two years in prison for trading hacked data.
DragonBreath has a zero-day: The Dragon Breath (APT-Q-27) Chinese e-crime group is exploiting a zero-day in dragoncore_k.sys, a Windows kernel-mode driver.
FEMITBOT campaign: CTM360 has spotted a malicious campaign that abuses the Telegram Mini Apps feature to impersonate large brands and defraud gullible users.
Amazon SES abuse: Kaspersky has seen threat actors abuse Amazon's SES emailing platform for mass-phishing operations since the start of the year.
VENOMOUS#HELPER campaign: Securonix looks at a campaign targeting at least 80 orgs with malicious phishing emails impersonating the US government and seeking to deploy a duet of RMM tools.
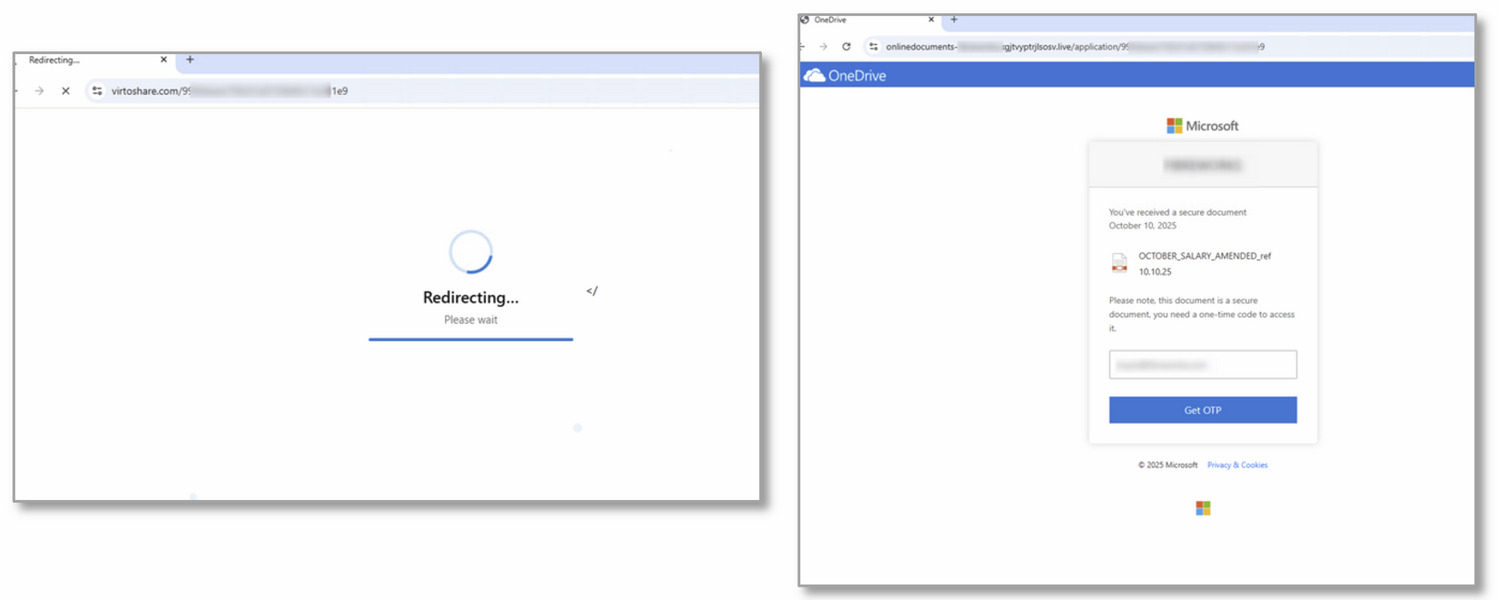
Massive phishing campaign: Microsoft's has spotted a massive AitM phishing campaign that's targeting more than 13,000 orgs across 26 countries. The campaign used a "code of conduct" subject as its main lure, which may explain why it's been so successful so far.
Device code phishing trends: Proofpoint says it's now tracking multiple threat clusters engaging in device code phishing campaigns, a trend that exploded this year after the rise of a platform automating the process. Now, Proofpoint says another PhaaS platform named ODx has also added the capability.
Malware technical reports
CloudZ RAT steals OTP codes from Phone Link: Cisco Talos has discovered a never-before-seen piece of malware that targets Phone Link, a Microsoft app for syncing smartphones to the Windows OS. The CloudZ remote access trojan watches the app's database for new synced SMS messages in order to steal one-time passcodes. The feature is likely used to bypass MFA on accounts that rely on SMS for the second factor.
Quasar RAT: Trend Micro looks at Quasar, a Linux RAT that comes with a PAM backdoor and a built-in rootkit.
Sponsor section
Join Burp AI developers, Dan and Pete, as they walk us through the new agentic AI functionality in Burp Suite Professional's Repeater.
APTs, cyber-espionage, and info-ops
APT-C-08 (Bitter): Qihoo's security team looks at a recent APT-C-08 campaign spreading the NUITKA loader.
Iranian op hacks Oman's government: Iranian hackers have breached 12 ministries inside the Omani government. At least 26,000 user records and case data have been stolen from the Ministry of Justice alone. The intrusions were discovered after the hackers left some of their servers misconfigured online. [Hunt Intelligence]
ScarCruft supply-chain attack: North Korean hackers have breached a Chinese gaming platform and backdoored its Android and Windows apps. The hack has been ongoing since late 2024. The gaming platform is popular in a Chinese region near the North Korean border. According to ESET, the campaign's goal appears to be to spy on refugees and defectors.
UAT-8302: Cisco Talos has published a report on UAT-8302, a newly discovered Chinese espionage cluster. The group has been targeting government entities in South America since at least late 2024 and government agencies in southeastern Europe in 2025. Its primary tools are the NetDraft and CloudSorcerer backdoors.
"Talos assesses with high confidence that UAT-8302 is a China-nexus advanced persistent threat (APT) group tasked primarily with obtaining and maintaining long-term access to government and related entities around the world. Post-compromise activity consisted of information collection, credential extraction, and proliferation using open-source tooling such as Impacket, proxying tools, and custom-built malware."
Russian disinfo on Claude doubles: The number of replies that repeat Russian propaganda and disinformation has doubled in Anthropic's Claude chatbot from last year. Replies containing Kremlin talking points are now at 15%, compared to last year's 7%. NewsGuard says that since the start of the US-Israel-Iran war, Claude has also started repeating Iranian propaganda, something it did not do before.
Vulnerabilities, security research, and bug bounty
Oracle switches to monthly security updates: Oracle has updated its security policies and will release monthly security updates going forward. The company had been previously releasing security updates every quarter. The first monthly security updates will start this month. Oracle cited the use of AI for the change.
MetInfo exploitation: A recently disclosed unauth PHP code injection bug (CVE-2026-29014) in the MetInfo CMS is being exploited in the wild.
New Ouroboros technique: Andrew Schwartz of Huntress and Yuval Gordon from Akamai have published details on Ouroboros, a new technique for credential extraction technique on Windows Server 2025 that abuses the new Delegated Managed Service Accounts (dMSAs) added with the 2025 release.
The cPanel auth bypass was a zero-day for two months: A major cPanel vulnerability had been secretly exploited as a zero-day for more than two months before a patch was released. Attacks have been recorded as far back as February 23; 64 days before a patch came out. Web hosting providers have been rushing to take down and secure cPanel systems but more than 44,000 servers are believed to have been hacked already. Recorded cases include threat actors defacing websites, deploying ransomware, cryptominers, and DDoS malware. [WebHostingToday]
Weaver E-cology bug under attack: Hackers are exploiting a vulnerability in the Weaver E-cology office collaboration platforms. Attacks started five days after a patch was released. The bug (CVE-2026-22679) allows remote code execution. Threat actors have been using it to take over platforms and run initial reconnaissance activity.
Bleeding Llama vulnerability: Cyera has published a write-up on Bleeding Llama, a vulnerability in the Ollama AI server that can allow unauthenticated attackers to leak the entire server process memory. This was patched back in February.
Security updates: Android, Apache HTTPD, Juniper, Qualcomm.
Infosec industry
Threat/trend reports: CyFirma and Internet Matters have recently published reports and summaries covering various threats and infosec industry trends.
Pulitzer prizes for infosec reporters and reporting: A collection of Reuters cybersecurity stories on Meta's fraudulent ad ecosystem has won the Pulitzer Prize for beat reporting this week. Reuters cybersecurity reporters Raphael Satter and A.J. Vicens were also among the winners for the national affairs category. Yael Grauer, an independent privacy and security reporter for more than 15 years, also won the Pulitzer with the AP staff for her reporting on how US tech companies helped China build its mass surveillance machine.
ATT&CK v19: MITRE has released v19 of the ATT&CK framework.
New tool—VanGuard: Ridgeline Cyber has released VanGuard, a self-contained incident response toolkit built in Go.
New tool—CodeNeedle: Security researcher Cas van Cooten has published CodeNeedle, a VSCode plugin to execute arbitrary JavaScript code at runtime over a local HTTP endpoint and backdoor an editor.
New tool—VSXSentry Guard: The VSXSentry team has released VSXSentry Guard, a VSCode extension that prevents users from installing other malicious extensions that are listed in the VSXSentry database.
Risky Business podcasts
In this episode of Risky Business Features, James Wilson and Brad Arkin chat about emerging trends in AI agent identity and credential management.
