Risky Bulletin Newsletter
May 04, 2026
Risky Bulletin: DigiCert hacked with a malicious screensaver file
Written by

News Editor
This newsletter is brought to you by PortSwigger. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.

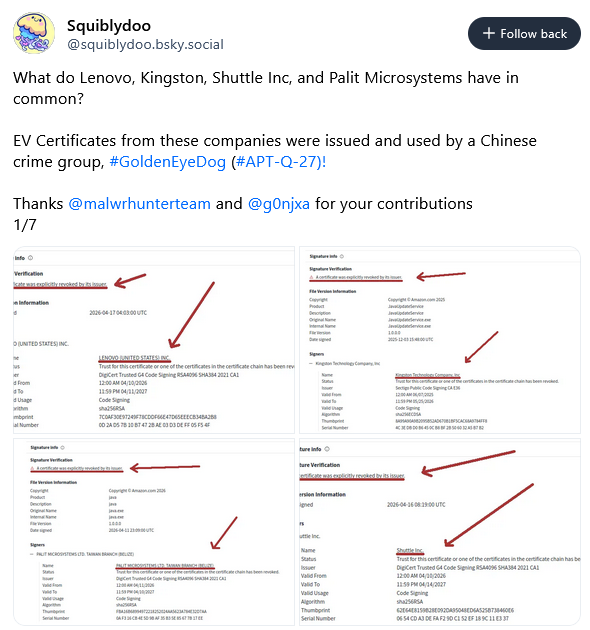
A threat actor gained access to DigiCert's backend and stole 27 code signing certificates they later used to sign malware.
The incident took place last month and was traced back to a social engineering attack that successfully compromised two employees of DigiCert's tech support team.
According to DigiCert's post-mortem, the attacker posed as a customer and tricked the tech support staff into running an SCR file, a format used to install and configure Windows screensavers.
DigiCert says the campaign was blocked on all but two of its tech support staff systems. On the first, the attacker maintained access for less than a day.
On the second, the attacker maintained access for almost two weeks. DigiCert says this happened because the CrowdStrike EDR agent had been misconfigured and was not connected to its central management server, so it never detected and reported the intrusion.
During that time, the attacker accessed tech support tickets for EV certificates DigiCert was in process of approving, stealing the future customer's "initialization code."
"Possession of an initialization code, combined with an approved order, is sufficient to obtain the resulting certificate (see Contributing Factors discussion below). Since the threat actor was able to obtain these two pieces of information for a finite set of approved orders, they were able to obtain EV Code Signing certificates across a set of customer accounts and CAs."
DigiCert says that during the time window the attacker was in its backend, it processed 60 orders for EV certificates, all of which it has now revoked. The attacker stole and actively abused almost half of those.
"27 of the revoked certificates were explicitly linked to the threat actor (11 were identified in certificate problem reports provided to DigiCert by community members linking the certificates to malware, and 16 were identified during our own investigation)."
The stolen certificates were used to sign payloads that delivered the Zhong Stealer, a malware family used in the past by cybercrime groups involved in cryptocurrency thefts.
The Zhong Stealer campaign was linked to GoldenEyeDog (APT-Q-27), a well-known Chinese e-crime group, but it's unclear if they're the ones who hacked DigiCert.
DigiCert called itself lucky because a third-party security researcher spotted the abuse of its certificates and reported the incident back to them, which led to the discovery of the compromised tech support accounts so quickly.

Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, James, and special guest Dmitri Alperovitch at the helm!
Breaches, hacks, and security incidents
Trellix security breach: Hackers have gained access to the source code of security firm Trellix. The company says no changes were made to any of its products. Trellix, which is one of Europol's closest partners, says it also notified law enforcement.
Major leak of personal data in Alberta: The data of 2.9 million voters from the Alberta province in Canada has been leaked online. The data was made available in a public, searchable database by a separatist political party. The Republican Party of Alberta took down the database after it was sued by the state's election agency. [CBC]
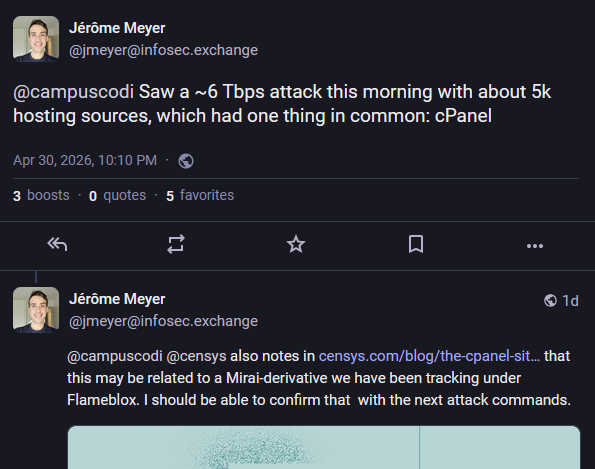
Fakestortion campaign hits cPanel sites: Threat actors are using a recent cPanel vulnerability to wipe public websites and post fake ransoms on their homepages. The attackers are asking for $8,000 paid in Bitcoin. Thousands of websites were defaced so far, but no ransom has been paid in the attacker's wallet. The cPanel vulnerability allows attackers to take over websites on shared hosting providers if the provider is using the cPanel software. It was patched last week and was also exploited to deploy cryptominers and DDoS malware. According to the Shadowserver Foundation, more than 44,000 cPanel systems appear to have been compromised in one form or another. [Censys // Ctrl-Alt-Intel // DataBreaches.net]
Guam government sites go down: It's because of the cPanel bug. They got hacked and taken offline. [DysruptionHub]
Rockstar stock went up after the hack: Rockstar Games stock has gone up after the company suffered a security breach and hackers leaked internal documents last month. Shares for Take-Two Interactive, the video game studio's parent company, have gone up by 10% and remained in that range since the hack. Gaming industry experts attributed the spike due to the extremely positive financial details that leaked online. This included healthy active user numbers and a whopping $1.3 million daily revenue from the GTA Online platform alone. [Video Games Chronicle]

Hacker leak exposes HU-RU propaganda coordination: A hacking group has leaked data from Hungarian media conglomerate Mediaworks. Mediaworks, the largest private news agency in Hungary, was listed by the World Leaks hacking group last week. An analysis of the leaked files found meeting notes where content directors said they'd contact Moscow for help in publishing anti-Ukraine content. Mediaworks threatened to sue anyone who used the leaked data and has already filed a lawsuit against a publication that covered the leak. Hungary's pro-Kremlin party lost the elections last month. [Telex] [h/t rqm]
HSBC India incident: Something we missed from the end of March was this weird story from HSBC India, with the bank asking customers to type their passwords in uppercase when they login, which suggests some sort of technical/crypto glitch might have happened. [OfficeChai]
Wasabi Protocol crypto-heist: Hackers have stolen $5 million worth of crypto assets from the Wasabi Protocol trading platform. The attack targeted the platform's integration across multiple blockchains. The attacker allegedly compromised an admin and set the delay on admin actions to zero to carry out malicious transactions instantly. [The Block]
Canonical DDoS attacks: A major DDoS attack has brought down most of the web infrastructure supporting the Ubuntu operating system. The attacks took place on Thursday and Friday and targeted several Ubuntu and Canonical domains and APIs. Users couldn't install or update their operating systems as a result of the attacks. A pro-Palestinian hacktivist group named the 313 Team took credit for the DDoS. This is the same group that took down BlueSky and Mastodon last month.
General tech and privacy
Agentic AI deployment guide: Countries from the Five Eyes intelligence-sharing alliance have published joint guidance on the proper adoption and deployment of agentic AI services. Looks like intel agencies have grown tired of their own government employees installing dumb AI agents everywhere and leaking data.
US lab develops GPS spoofing detector: A US research lab has developed a new technology to detect GPS spoofing attacks. The detector is a software-defined radio that analyzes radio frequencies for signs of GPS manipulation. The Oak Ridge National Laboratory says it successfully tested the new system at a DHS test event. The Oak Ridge National Laboratory is one of the research labs established by the US government for the Manhattan Project during the Second World War. [h/t Denaro]
RentTech told to calm down: Australia's privacy commission told RentTech, the company behind the 2Apply renting platform, to stop demanding so much personal information from its users. [Choice] [h/t Asher Wolf]
New Windows Run app: Microsoft is testing a new app and new UI for the old Windows Run app.
Linux on the PS5: There's now a tool to run Linux on the PlayStation 5 gaming console.
IBM Bob: IBM has launched Bob, an AI coding assistant for large enterprises.
Oscars ban AI: The Academy of Motion Picture Arts and Sciences announced new eligibility rules for the Oscars and have banned AI from the acting and screenwriting categories. [Gizmodo]
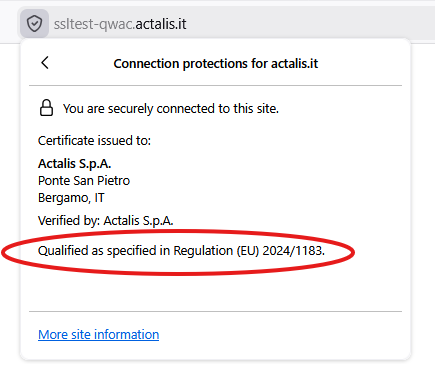
Firefox now displays QWACs: Firefox 150, released at the end of last month, now shows if a site is QWAC compliant. QWAC stands for Qualified Certificates for Website Authentication and is a new type of digital certificate that the EU wants browser makers to support just for EU audiences.
Ask Jeeves shuts down: Ask Jeeves, one of the internet's first search engines, has shut down on Friday a month short of its 29 years anniversary.
Government, politics, and policy
NSA is testing Mythos: The US National Security Agency has gained access and is testing Anthropic's Mythos cybersecurity model. NSA officials have allegedly been impressed by the model's ability and speed to find new vulnerabilities. Staff has found vulnerabilities in Microsoft products and other widely used software. [Bloomberg]
White House questions tech companies on AI defenses: The White House has asked a group of more than 30 tech companies on how to defend against AI-driven cybersecurity attacks. US officials had a meeting last week and tech execs were asked to answer a set of questions by Friday about their use of AI and how they're defending it. The meeting comes as the White House is preparing another executive order for the AI industry. [Politico]
Minnesota bans AI nudification apps: The US state of Minnesota has banned AI nudification apps. The state Senate passed the ban in an unanimous 65-0 vote. The Minnesota House passed the ban a week earlier in a similar near unanimous vote. Minnesota becomes the first US state to ban such apps. The new law will allow survivors to sue the nudify app makers for damages and let the state attorney general to fine app makers up to $500,000 per violation. [MinnPost]
Russia bans import of dual-use satellites: The Russian government has banned the import of dual-use satellite terminals. The Kremlin's ban does not name any vendors but likely covers Starlink terminals. The terminals have played a crucial role in keeping the Iranian population online after the country disconnected from the global internet in February. [TASS]
Russia starts fining gaming companies: Russia's internet watchdog has started slowly fining gaming companies for failing to store the data on Russian players on local Russian servers. Fines have been leveraged against EA, Rockstar Games, Battlestate Games, Lesta, and NetEase. Cases are also ongoing against Epic Games, Embracer, and Digital Extremes. [Meduza]
Iran is rebuilding its entire internet around whitelists: The Iranian government is following through on its plan to restrict internet access to its entire population. Tehran is currently building a whitelist-based internet access model where everything is tied to real identities and restricted to regime-approved individuals. [The Miaan Group]
Sponsor section
In this Risky Business sponsor interview, James Wilson talks with James Kettle and Daf Stuttard from PortSwigger about the incredible research James will unveil at Black Hat US this July, and how that research will be productised into Burp Suite.

Arrests, cybercrime, and threat intel
Ransomware negotiators sentenced to prison: Two former employees of US cybersecurity firms have been sentenced to prison for deploying ransomware. Kevin Tyler Martin, a former ransomware negotiator at DigitalMint, and Ryan Clifford Goldberg, a former incident response manager at Sygnia, have been sentenced to four years each. The two worked with a third DigitalMint employee to deploy the BlackCat ransomware and extort US companies. They allegedly made more than $1.2 million dollars from ransom payments. The third suspect is set to be scheduled in July.
Pharmacist investigated for installing spyware: A former Maryland pharmacist has been charged with hacking more than 200 co-workers at the University of Maryland Medical Center. Dr. Matthew Bathula deployed spyware on work computers to steal credentials and spy on victims through webcams. Over the course of eight years, he stole hundreds of sexually explicit photos and videos, including female staff undressing, pumping breastmilk at work, and having sexual relations at home. [The Baltimore Banner]
Russian hacker "Digit" pleads guilty: A Russian national has pleaded guilty to hacking oil and gas infrastructure in the US and Europe. Artem Vladimirovich Revenskii was arrested in the Dominican Republic last November and extradited to the US. He went online under the hacker pseudonym of Digit. He was a member of a pro-Kremlin hacktivist group named Sector16 and carried out attacks against countries deemed to be enemies of the Russian government. [Bloomberg]
Versus admin extradited to US: The administrator of a defunct dark web marketplace has been extradited from Colombia to the US. Patrick Schmitz, 37, of Germany, was charged with running the Versus Project marketplace. The site sold drugs, malware, hacking and fraud services. It had more than 300,000 registered users before it was taken down in 2022.
Uganda raids scam centers: Ugandan authorities have raided two cyber scam call centers in the country's capital Kampala. Almost 170 foreigners have been detained and are set to be deported. The call center operators targeted their home audiences in India, Pakistan, and other countries across Southeast Asia. [Reuters // Modern Ghana] [h/t Agness Dembe]
SafeMoon co-founder flees to Russia: Kyle Nagy, one of the two co-founders of the SafeMoon cryptocurrency platform, has fled to Russia. He is sought by US authorities for misappropriating the platform's funds. His co-conspirator was sentenced to eight years and four months in prison earlier this year. [RadioFreeEurope]
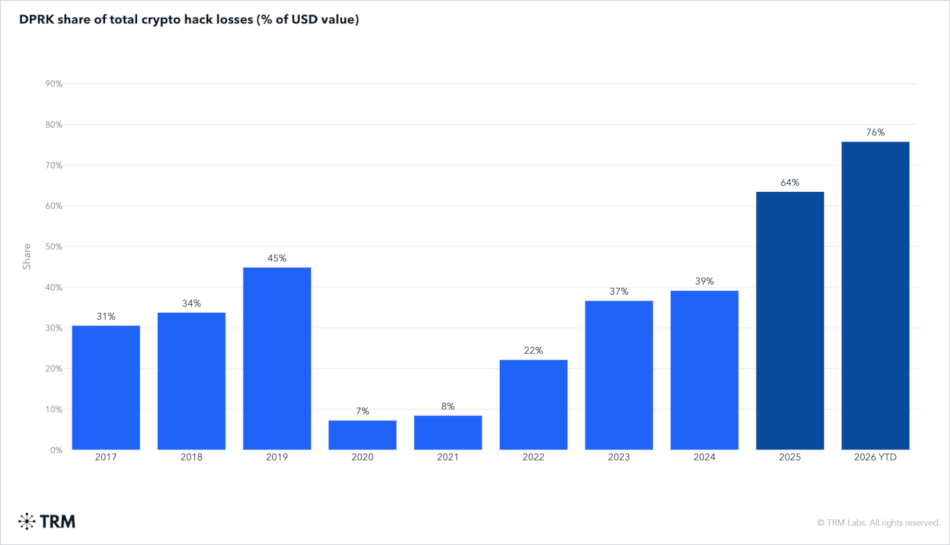
North Korea stole 3/4 of all crypto this year: North Korean hackers have stolen $577 million worth of crypto-assets since the start of the year, accounting for three-quarters of all crypto stolen in 2026. Two groups have been responsible for all hacks this year, according to TRM Labs. This brings North Korea's total crypto thefts to more than $6 billion since 2017.
Qilin affiliate profile: The Ctrl-Alt-Intel team has published a profile on an affiliate of the Qilin RaaS and their operations after they kept leaking data from their operations.
RDP and VNC exposure: More than 1.8 million RDP and 1.6 million VNC servers are currently exposed on the internet, according to a new Forescout report.
Malicious Ruby gems and Go modules: Socket has discovered a threat actor that published a cluster of malicious Ruby gems and Go modules designed to steal developer credentials and poison their tools and CI/CD pipelines.
Malicious ClawHub skills: Manifold Security has found 30 malicious skills on ClawHub, all published by the same user.
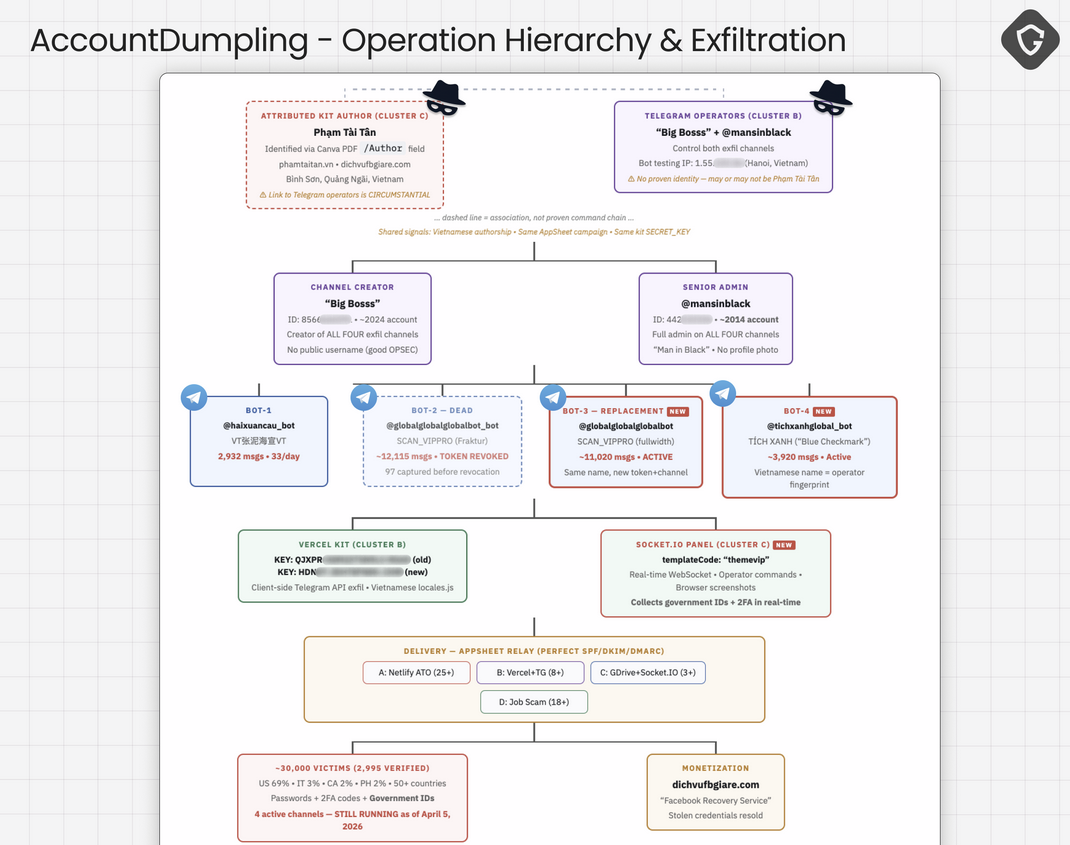
AccountDumpling campaign compromises 30k Facebook users: More than 30,000 Facebook users have been compromised in a phishing campaign. The campaign was linked to a Vietnam-based group that seeks access to Facebook business accounts. The operation abused and turned Google's AppSheet service into a phishing relay, making the emails appear from legitimate Google email infrastructure. The stolen accounts were later sold on Telegram channels. [Guardio Labs]
Malware technical reports
Cerberus Anti-theft app: Security researcher Mark Esler says that Cerberus Anti-theft, a Google Play-listed app and sold by LSDroid SRL in Italy, contains all the usual features of stalkerware. Although, it's one with a very shady business model.
"When the abuser’s €5/month subscription lapses, Cerberus reads the timestamp on the next boot, finds it expired, and reverses its concealment. It cancels its hidden-mode notifications, builds a notification with a “Buy” button, re-enables the launcher icon, stops its background service, and relinquishes its device-admin claim — allowing the victim to uninstall normally. An unfamiliar app called Cerberus suddenly appears in the launcher with a persistent notification asking the user to renew a subscription they never bought."
Mini Shai-Hulud spreads to PHP: The Mini Shai-Hulud malware and supply chain attack has now spread to Packagist, one of the PHP package installers.
Sponsor section
Join Burp AI developers, Dan and Pete, as they walk us through the new agentic AI functionality in Burp Suite Professional's Repeater.
APTs, cyber-espionage, and info-ops
Antiy accuses SentinelOne of "psychological warfare": Chinese security firm Antiy has accused SentinelOne of "psychological warfare" for publishing its report on the Fast16 malware. The Chinese company claims the report was released to aid the US' war in Iran. Several Chinese companies have attacked SentinelOne in the past, mainly due to its extensive research on the Chinese cybersecurity landscape and its ties to the Chinese government.
Shadow-Earth-053: Trend Micro looks at a new suspected Chinese APT cluster targeting government entities and critical infrastructure across South, East, and Southeast Asia, as well as a NATO member state.
Famous Chollima's PromptMink campaign: North Korean hackers are using a new malware named PromptMink to steal cryptocurrency from web developers. The malware is distributed via malicious npm packages. ReversingLabs says the first traces of the malware were found in libraries in February, added to the code via an Anthropic's Claude Opus commit. It's unclear if the author was spoofed or if Claude mistakenly added malicious to the project somehow.
More Famous Chollima: Kieran Miyamoto (KMSec) has also published a report on the Famous Chollima group, focusing on their abuse of Cloudflare infrastructure for its malicious job interview campaigns.
Vulnerabilities, security research, and bug bounty
Copy Fail vulnerability exploited in the wild: The Copy Fail Linux vulnerability is being exploited in the wild, according to CISA. Attacks began a day after the vulnerability was disclosed by Theori researchers on Thursday. The vulnerability impacts all Linux distros released since 2017. It allows threat actors with a foothold on a compromised system to gain root access.
Android VRP rewards: Google says it will pay between $750,000 and $1.5 million for bug reports of zero-click chains against Pixel devices with a Titan M2 chip. The rewards have gone up for Android, while also going down for Chrome.
PQC migration status: Cisco researchers looked at how nine protocols are implementing and migrating to quantum-resistant cryptography. The research analyzed TLS, IPsec, BGP, DNSSEC, SSH, QUIC, OpenID Connect, OpenVPN, and Signal Protocol and found that efforts are underway but at various stages of implementation/rollout, with most issuing being around hardening the authentication parts of the protocol.
Windows patch bypass: The Synacktiv team has published a two-part report on CVE-2026-24294, an attack that bypasses the patches for CVE-2025-33073, a bug from last year that can allow attackers to bypass Windows authentication without user interaction.
Security updates: Kubernetes, WhatsApp, WireShark.
Infosec industry
Threat/trend reports: Antiy, Expel, Incogni, Positive Technologies, Prossimo, Wasabi, and Wiz have recently published reports and summaries covering various threats and infosec industry trends.
Acquisition news: Infosec giant Palo Alto Networks will acquire Portkey, a platform for managing AI agents.
New tool—VisualSploit: Security researcher Max Harari released VisualSploit, a tool to backdoor Visual Studio project files with custom shellcode that executes whenever the project is opened or built.
New tool—Rustinel: Hexanion's Théo Foucher has open-sourced Rustinel, an endpoint detection tool for Windows and Linux.
New tool—SEC Cybersecurity Incidents: Duke Security has launched a web tool that tracks and alerts users on security incidents disclosed in SEC filings.
Bsides Exeter 2026 videos: Talks from the Bsides Exeter 2026 security conference, which took place last month, are now available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the US government stepping in to fight 'distillation attacks' by Chinese AI labs. These are methods used to steal the special sauce of frontier AI models simply by asking questions.

In this episode of Risky Business Features, James Wilson explores how distillation techniques are both a legitimate way to train smaller models, as well as a way to steal model capabilities.


