Risky Bulletin Newsletter
April 03, 2026
Risky Bulletin: Russia will revoke licenses for unruly ISPs
Written by

News Editor
This newsletter is brought to you by Knocknoc. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
The Russian government will tighten operating requirements for internet service providers in an effort to kill small neighborhood providers.
The new requirements will include higher license fees, larger minimum operational capital, and mandatory deployment of the FSB's SORM traffic interception equipment.
According to reports from Izvestia and RBC, the new proposed rules would give the Russian Ministry of Digital Development, Communications, and Mass Media the power to revoke licenses without a court order for those who fail to comply.
Providers who lose their license will also be banned from obtaining a new one for a decade.
The move is a straight and unapologetic attempt to force smaller ISPs off the Russian market.
Ever since Russia invaded Ukraine and the Kremlin had cranked up internet censorship, smaller ISPs have been its weak spot. Many providers delayed or blatantly refused to deploy SORM equipment, choosing instead to pay the fines but advertise their services as uncensored to their customers.
Ever since last year, the Kremlin appears to have had enough of the constant shenanigans and is now on a war path to separate the RuNet from the global internet and implement a China-style firewall, a system where local unruly ISPs have no place.
Multiple disconnection tests have taken place, internet censorship has reached millions of domains, and the government is now pushing a full-on crackdown against VPNs.
The FSB has also received the power to cut internet access at will everywhere in Russia and at least three major cities have had their mobile internet access replaced with a whitelist-based system where only certain approved websites are allowed to load.
The leaked plans have also spurred intense conversations online in Russia, with many arguing that internet access will soon be controlled by a handful of large providers subservient to the Kremlin and Putin.
The main concern is that users are seeing the last days of the free internet in Russia and that full and unescapable surveillance will soon follow.
In addition, financial concerns are also being raised, as the larger telcos will be free to impose larger tariffs without the fear of customers migrating to smaller neighborhood providers.
Unlike many other countries, Russia has a large and thriving pool of small providers, numbering in the realm of thousands and accounting for a huge chunk of internet subscribers.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
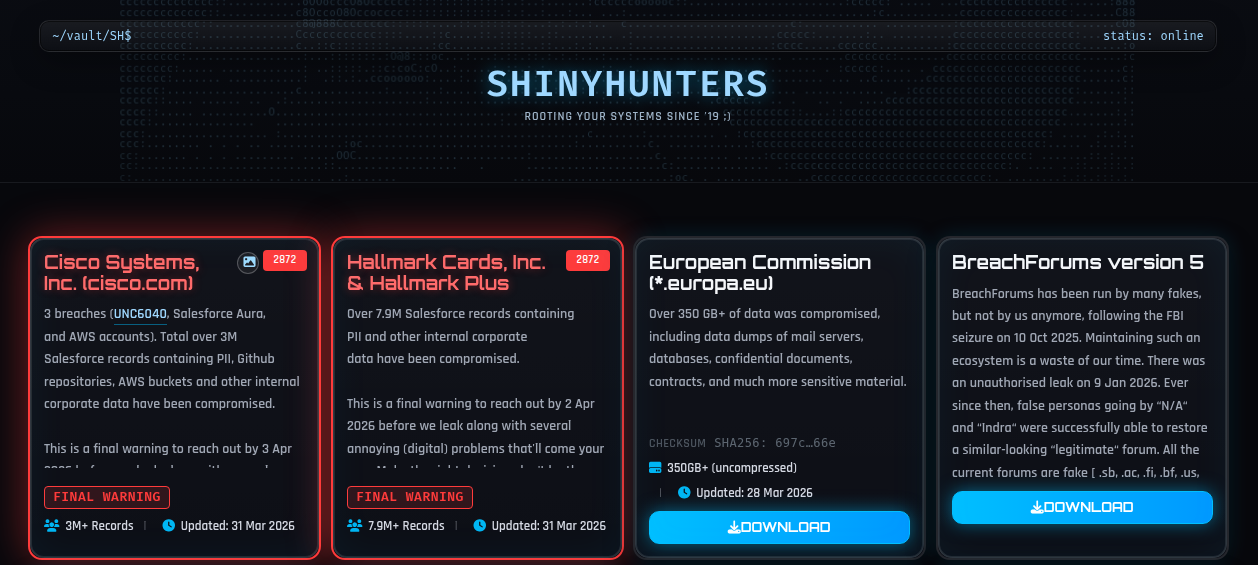
Hackers steal Cisco source code: Hackers claim to have stolen source code from American router and firewall maker Cisco. The attackers used a malicious GitHub Action to steal credentials from the company's development environment. The attackers stole source code from internal systems and credentials for some of Cisco's AWS servers. The hackers are now trying to extort the company. [BleepingComputer]
Cyberattack disrupts access to newspaper archives: A cyberattack on a Utah company has disrupted access to digital newspaper archives across the US. The incident took place in late February and is still ongoing. The NewspaperArchive service initially hoped to restore all services by the end of last month. Most of the impact is at libraries, many of which have used the company's service to create digital archives of local newspapers. [DysruptionHub]
Hasbro breach: American toymaker Hasbro has been hit by hackers over the past weekend. The company shut down affected systems and deployed intermediary infrastructure to continue taking orders and shipping products. In an SEC filing this week, Hasbro said it would take weeks to recover. No hacking or ransomware group has taken credit for the breach yet. [TechCrunch]
Mercor breach: AI hiring startup Mercor has disclosed a security breach caused by the supply chain attack on the LiteLLM Python library. The company says it contained the breach as soon as it discovered it. Mercor is valued at $10 billion. The company helps other AI companies get in touch with experts in various fields to train specialized AI models.
EU links recent breach to Trivy supply chain attack: The EU's security team has linked a recent security breach of the European Commission's AWS environment to the Trivy supply chain attack. A hacking group named TeamPCP compromised the Trivy security scanner last week to steal credentials and access tokens from its user. Those credentials were allegedly sold to other hacking groups who used them to steal data and extort victims. CERT-EU says a group called ShinyHunters used its stolen creds to access the EU's AWS account, steal over 90GB of data, and leak it on the dark web.
Cyberattack hits multiple Mass. towns: A cybersecurity attack has disrupted police and fire departments in at least four towns in the US state of Massachusetts. The towns of Ashby, Dunstable, Pepperell, and Townsend reported disruptions to department services and phone lines this week. The attack was traced back to Patriot Regional Emergency Communications Center, an emergency comms center shared by all four. [Lowell Sun]
Water plant ransomware attack: A ransomware group has hit the water treatment plant for the city of Minot, North Dakota. Even if some IT systems were encrypted, the plant remained operational. [StateScoop]
Axios incident linked to social engineering attack: Axios project admin Jason Saayman says he lost access to the project through a social engineering attack where a threat actor lured him to collaborate on another project but infected him with malware that stole cookies, tokens, and credentials from his system.
Drift hacked for $280 million: Hackers have stolen $280 million worth of crypto-assets from the Drift DeFi platform. The company said the attack had been prepared weeks in advance before it took place on April 1. Drift says hackers obtained multisig transaction approvals in advance from its Security Council, allowing them to move funds when the time came. [The Block]
WhatsApp notified SIO spyware victims: WhatsApp has notified around 200 users who were infected with spyware after installing a fake WhatsApp iOS version. Most of the victims are located in Italy. WhatsApp also sent a cease and desist letter to the app maker, Italian surveillance vendor SIO Spa. On its website, the company says it only works with intelligence and law enforcement agencies. [La Repubblica // TechCrunch]

General tech and privacy
Proton Meet: Proton, the company behind ProtonVPN, has launched Meet, a new E2EE video conferencing platform. The platform is currently free to use and doesn't even require a Proton account to access.
GitHub Actions security features to arrive sooner: Following a series of supply chain attacks on GitHub that originated from the abuse of GitHub Actions, GitHub says it will accelerate the development and rollout of some Actions security features from its 2026 roadmap it had planned for later this year.
Flipboard launches Surf: News aggregation service Flipboard has launched Surf, an app and website to build custom social feeds from multiple sources, such as RSS, BlueSky, Mastodon, Threads, YouTube, podcast feeds, and more.
Thunderbird will evaluate encryption keys: The Mozilla Thunderbird email client will evaluate users' encryption keys and tell them if they are weak or secure enough.
Apple's ClickFix protection: Patrick Wardle has reverse-engineered Apple's new system that blocks ClickFix attacks.
1.1.1.1 DNS privacy: Cloudflare has reaffirmed its promise not to store or sell the personal data of users who use its 1.1.1.1 private DNS service.
EmDash CMS: Cloudflare has released EmDash, a TypeScript-based CMS modeled after WordPress. The company coded EmDash with AI, focused on plugin security, and called it WP's "spiritual successor."
Anthropic races to take down Claude source: Anthropic has allegedly sent more than 8,000 DCMA complaints in an attempt to take down the source code of its Claude Code AI coding agent after devs accidentally leaked it earlier this week. [PCMag]
Google lets you change your username: Google has rolled out a new feature that lets users change their current username. The feature was tested last year in India and has now rolled out in the US as well. Users will be able to change their username every 12 months. Old usernames will still be valid and redirect messages to the new one.
Government, politics, and policy
EU tells staff to stop yapping on Signal: EU top officials and their staff were told to stop discussing sensitive information on Signal over fears their accounts could be hacked. The warning comes after the Commission became aware of a Signal group where high-ranking officials discussed sensitive matters. The officials were told to delete the group and stop using Signal for sensitive matters. Intelligence agencies in the EU and the US warned that Russian state-sponsored hackers were seeking to hack Signal and WhatsApp accounts of top officials for espionage purposes. [Politico Europe]
EU tells staff to stop using genAI: The European Commission has told staff from using AI-generated content, such as text and images, in official communications. I think someone in the EU administration has seen all those cringe White House posts with AI-generated images and videos and responded with a resounding "nope nope nope." [Politico Europe]
NGOs protest Germany's new surveillance laws: Fourteen German NGOs have signed an open letter and asked the German government to vote down the country's new surveillance law draft that gives intelligence agencies broad new data collection and analysis powers.
Gutted board backs FISA 702 renewal: After the Trump administration fired all but one member of the Privacy and Civil Liberties Oversight Board, that member is now backing up a renewal of the FISA Section 702 in what experts are calling an obvious lack of independence. [NextGov]
US suddenly regrets shutting down GEC: The US State Department has ordered embassies and consulates to push back against foreign influence operations. The move comes as Iranian, Chinese, and Russian info-ops are leveraging the Iran war to discredit US politics. The State Department shut down all of its disinformation fighting offices and programs last year because they allegedly "cEnSoReD cOnSeRvAtIvE vOiCeS," so this comes as a FAFO vindication moment for everyone who had a brain and understood what those offices actually did. [The New York Times]
There was an entire office in the State Department dedicated to this problem that Republicans in Congress defunded and Marco Rubio eliminated completely in his first month as Secretary.
— Derek B. Johnson (@derekbjohnson.bsky.social) 2026-04-02T10:27:45.418Z
Sponsor section
In this Risky Business sponsor interview, James Wilson chats with Adam Pointon, CEO of Knocknoc, about how AI is making old school security controls and paradigms like deny-by-default cool again.
Arrests, cybercrime, and threat intel
Another Prince Group member sent to China: Cambodian officials have extradited to China another member of the Prince Group. Li Xiong was described as a core backbone member of the organization. He also served as chairman of Huione Group, a subsidiary of the Prince Group. Both Huione and Prince Group have been sanctioned by the US. The Prince Group was sanctioned for running tens of cyber scam compounds, while Huione for laundering the scammed funds. [OCCRP]
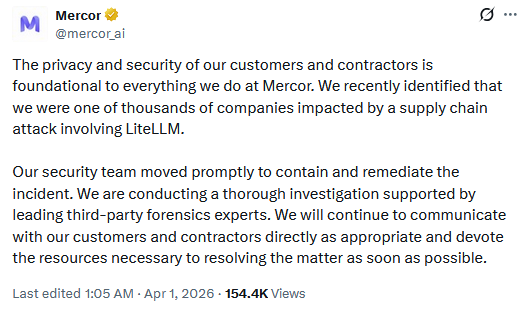
PHISLES: Group-IB has published a profile on PHISLES, a threat actor targeting e-banking app users in the Philippines.
UNC1069 profile: Google's threat intel team has published a profile on UNC1069, the North Korean e-crime group behind the Axios supply chain attack, and a report on the attack itself. CrowdStrike, Microsoft, Palo Alto Networks, and Veracode also published their own reports on this.
Keitaro TDS: Infoblox has published its third report on Keitaro, an advertising performance tracker used by marketers and cyber criminals to route and measure traffic.
Mustard Tempest: PT Technologies looks at Mustard Tempest, an IAB behind the FakeUpdates/SocGolish operation that appears to have rented its infrastructure to the Cloud Atlas APT.
UAT-10608: A new threat actor is targeting Next.js-based applications vulnerable to the React2Shell vulnerability. The group, tracked by Cisco as UAT-10608, has already compromised over 750 hosts.
LofyGang returns: JFrog has spotted the LofyGang threat actor return with new malicious packages uploaded to npm, all delivering a new RAT/infostealer mix to steal victims' credentials and crypto-wallet data.
TasksJacker campaign: North Korean hackers have breached more than 400 GitHub repositories to plant malicious tasks.json files. Users loading or cloning one of the hacked repos in the VS Code IDE would have malware installed on their systems. The campaign, named TasksJacker, abused a VS Code feature that auto-executes instructions placed in a tasks.json file.
Residential proxy ecosystem: According to a new GreyNoise report, 39% of IPs seen in suspicious activity originate from the residential address space, and each residential IP averages fewer than 3 sessions before disappearing and never being seen again.
Proxy.am rebrands as ProxyBox: Synthient says that a defunct residential proxy provider named Proxy.am did not shut down last year, but merely rebranded under a new name of ProxyBox.
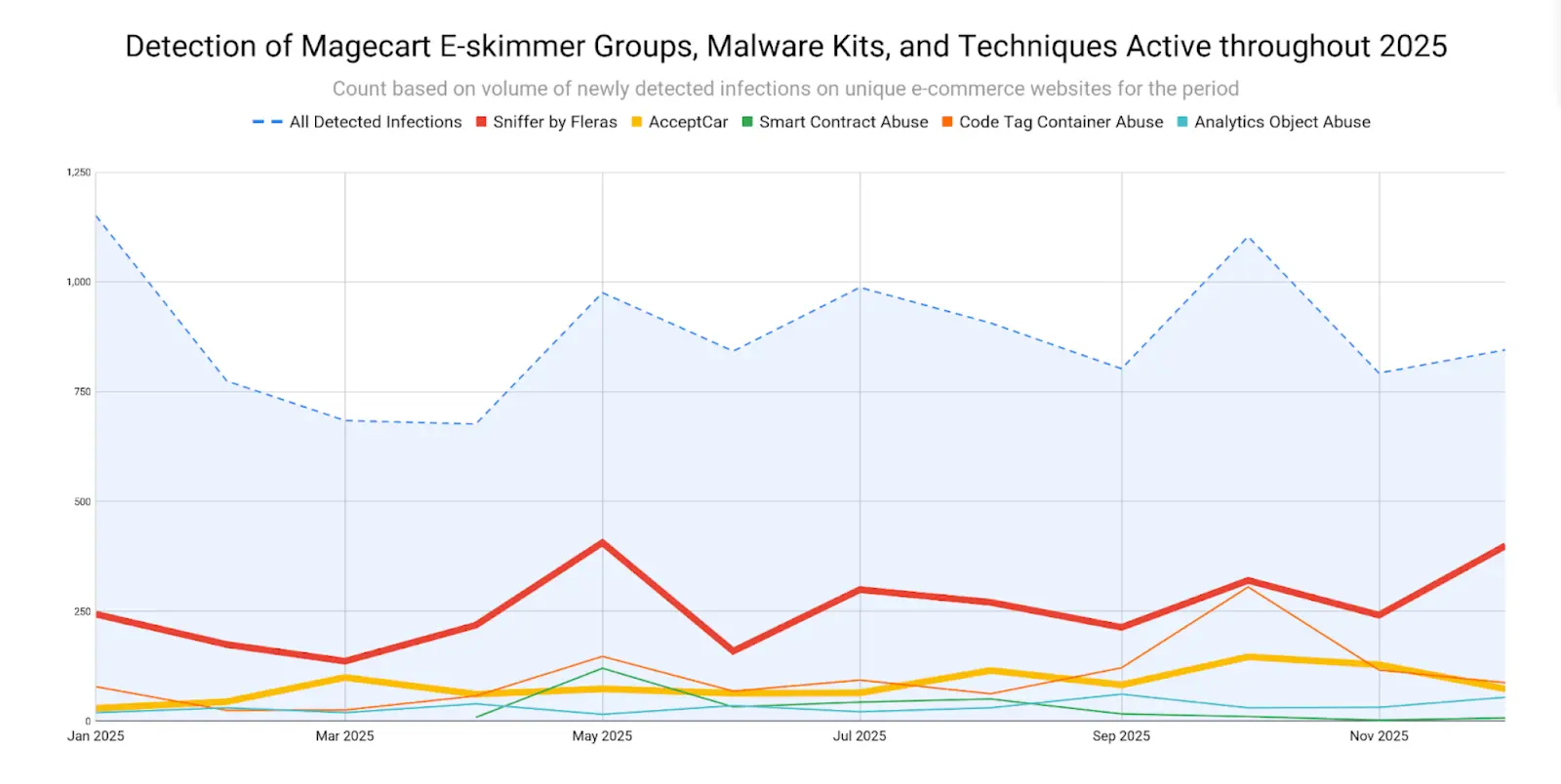
"Sniffer by Fleras" dominates skimmer market: More than 142 million stolen card details were posted online last year. While the number is smaller than the previous year, Recorded Future says the quality of the cards was far superior, putting more users at risk than usual. The company described the card fraud ecosystem as getting more industrialized, with several web skimmer kits now being broadly available on the market. One kit alone, named Sniffer by Fleras, was responsible for a quarter of all skimmer incidents.
Malware technical reports
PlugX: Security researcher Abdullah Islam has published an analysis of new versions of the PlugX malware.
GlassWorm returns, again: CheckMarx has spotted new VS Code extensions spreading GlassWorm, in what appears to be the umpteenth flare-up of this campaign.
VENOM PhaaS: The team at AbnormalAI has discovered a new phishing-as-a-service platform named VENOM. The service is advertising a phishing kit capable of AitM attacks and MFA interception, and its innovative use of HTML code to render QR code phishing that doesn't rely on images.
Qilin EDR killer: The Qilin ransomware group appears to be running the most powerful EDR killer available today, with the capability to terminate over 300 different EDR drivers from almost every vendor in the market. [Cisco Talos]
Yurei ransomware leaks tools: The operators of the Yurei ransomware have leaked all their malware and hacking tools through a server open directory. Unfortunately no source code or databases that could be used for free decryptions were included.
New Blog! Stranger Strings: Yurei Ransomware Operator Toolkit Exposed Through my research with Team Cymru’s data, we have discovered another ransomware operator’s server with Stranger Things-themed tools, check it out👇 www.team-cymru.com/post/yurei-d...
— Will T (@bushidotoken.net) 2026-04-01T11:31:47.725Z
Akira ransomware: A Halcyon report looks at the Akira ransomware and its recent operational upgrades to allow it to deploy in less than one hour after initial compromise.
Akira lookalike: ESET researchers have identified a new ransomware group posing as the bigger Akira gang in attacks against South African entities.
https://bsky.app/profile/esetresearch.bsky.social/post/3miiouhsy322i
RetroRAT: Seqrite researchers look at Operation DualScript, an e-crime campaign spreading the RetroRAT and clipboard hijackers, an obvious effort to steal funds from cryptocurrency users and e-banking apps.
Xloader: Zscaler researchers analyze the version 8.1 of the Xloader infostealer. The report focuses on "the latest obfuscation methods and provide[s] an in-depth analysis of the network communication protocol."
Storm infostealer: Varonis has published a report on Storm, a new infostealer that appeared earlier this year and is being rented for under $1,000/month—which is kinda pricey, if you ask me.
CrystalX MaaS: A Kaspersky report looks at CrystalX, a new RAT offered through a MaaS model.
"On the panel provided to third‑party actors, in addition to the standard features of RAT‑like malware, a stealer, keylogger, clipper, and spyware are also available. Most surprisingly, it also includes prankware capabilities: a large set of features designed to trick, annoy, and troll the user. Such a combination of capabilities makes it a rather unique Trojan in its category."
NoVoice Android rootkit: A rootkit has been spotted hidden inside more than 50 Android apps available through the official Play Store. The NoVoice rootkit is designed to survive factory resets and steal WhatsApp sessions. It works only on older smartphones running Android 7 and earlier, which last received security updates in 2021. According to McAfee, the infected apps have been downloaded more than 2.3 million times.
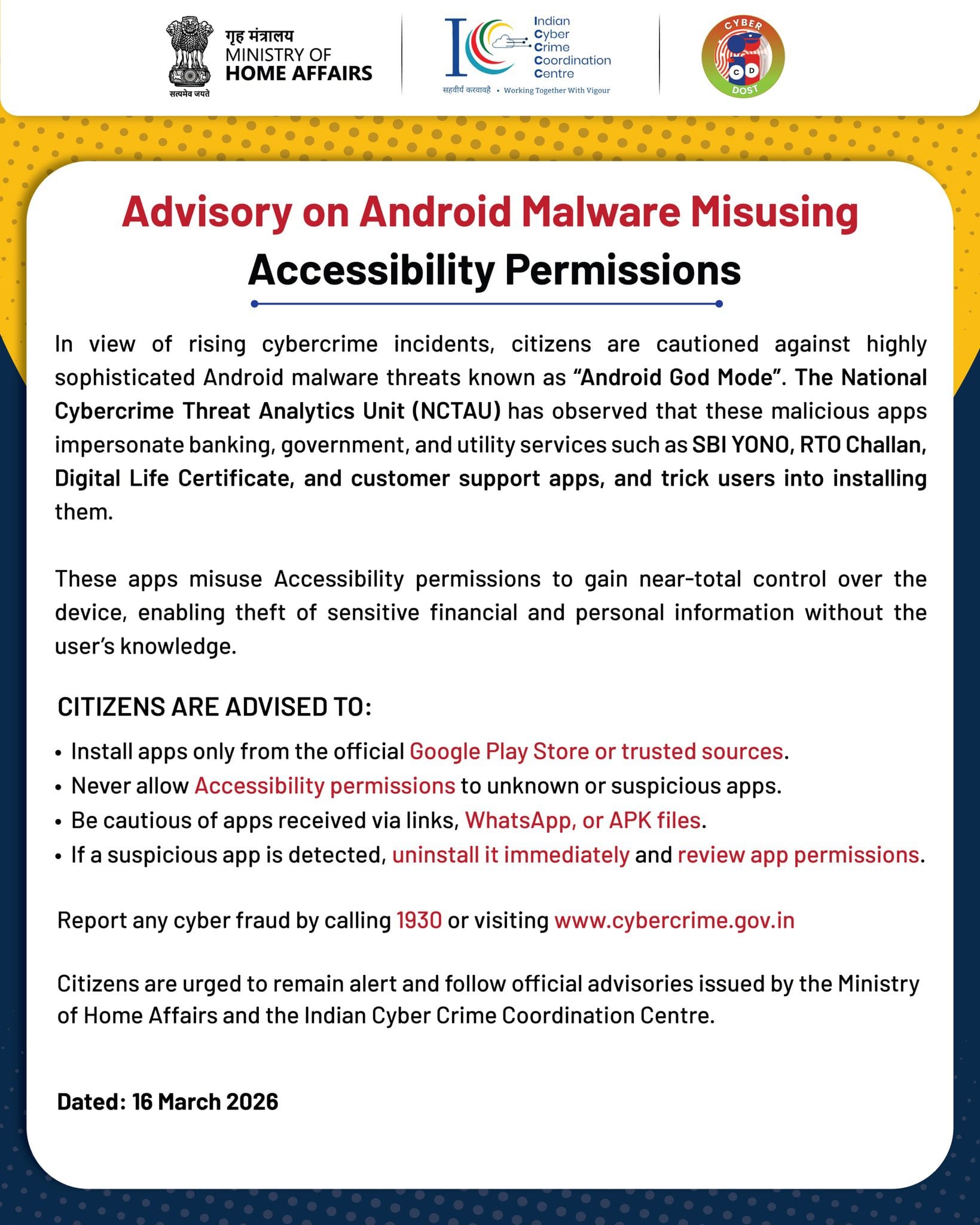
Android God Mode: A new Android malware strain named God Mode is spreading across India. God Mode is distributed via messenger spam and disguised as apps for government services, Indian banks, and utility services. India's cybercrime agency has warned the public about God Mode campaigns this week. [The 420 // NCTAU advisory, PDF]
Sponsor section
In this product demo, Knocknoc CEO Adam Pointon walks Patrick Gray through the Knocknoc secure access platform. Knocknoc is a platform that restricts network and service availability to authenticated users via existing network security equipment. Users don't need to install an agent. It also has an identity-aware proxy component that supports web applications and RDP.
APTs, cyber-espionage, and info-ops
TA416 targets the EU: A new Proofpoint report has highlighted that a Chinese espionage group tracked as TA416 (RedDelta, Red Lich, Vertigo Panda, SmugX, DarkPeony) has returned to targeting EU governments after a period of inactivity.
This renewed focus, observed since mid-2025, most heavily targeted individuals or mailboxes associated with diplomatic missions and delegations to NATO and the EU. The timing aligned with heightened EU–China tensions over trade, the Russia–Ukraine war, and rare earths exports.
— ThreatInsight (@threatinsight.proofpoint.com) 2026-04-01T15:25:07.692Z
Election disinformation report: DFRLab has published a report on the influence operations that targeted elections in Georgia, Moldova, Armenia, and Azerbaijan.
Sanctioned Gagauznews returns: The same DFRLab also traced the assets of a new pro-Kremlin news agency, Media Pulse Moldova, to Gagauznews, an older news portal sanctioned and dismantled by Moldovan authorities after its invasion of Ukraine. Media Pulse Moldova seems to be spending most of its time these days promoting other sanctioned Russian and Moldovan figures, as well as organizing pro-Russian protests.
Vulnerabilities, security research, and bug bounty
Security updates: Apple, Chrome, Cisco, Gigabyte, Mongoose.
Node.js pauses bug bounty program after funding lapse: The Node.js project has paused its bug bounty program after a lapse of its external funding sources. The program had been running for almost ten years, since 2016. It had been sponsored by the Internet Bug Bounty, a program itself sponsored by several tech giants, such as Microsoft, Meta, and Adobe. Node.js is the fifth most popular web server and is used by around 6.0% of all sites on the internet.
Cyber Workforce CTF: The University of North Georgia has won the CTF contest at the US DOW's Cyber Workforce Summit last month. [GovInfoSecurity]
Apple backports DarkSword patches: Apple has backported security updates for its older iOS 18. The updates patch exploits used in the DarkSword iOS hacking framework that leaked online last month. The exploit framework has been used in the wild and mass-exploitation is expected. [WIRED]
Chrome zero-day: Google has released a security update to patch a Chrome zero-day exploited in the wild. Tracked as CVE-2026-5281, the zero-day is a memory corruption bug in Chrome's web graphics component Dawn. It is the fourth Chrome zero-day patched this year.
Vertex AI double agent: PAN researchers have found a way to abuse the permission model of Google's Vertex AI agent to secretly perform malicious actions in what they called a double agent attack.
FreeBSD root RCE: The FreeBSD project released security updates last week to patch a rare remote code execution attack that can allow attackers to run code as root on unpatched servers. Tracked as CVE-2026-4747, the vulnerability resides in the Generic Security Services (GSS), an API that lets remote apps establish private comms with the server. Malcrafted oversized packets sent to the GSS service can allow attackers to run malicious commands.
Major Mongoose vulnerabilities: The Mongoose web server project has released a security update this week to patch three major vulnerabilities. The vulnerabilities include an authentication bypass and two remote code execution issues. All are independently exploitable from each other. The Mongoose server is typically used on embedded devices due to its super light size and built-in TLS support.
Android GPU bug write-up: Google's offensive security team has published a technical deep-dive into CVE-2024-23380, a memory corruption bug in the Qualcomm GPU component that can be used to run malicious code as root on Android.
Cisco security updates: Cisco has released nine security advisories for various products, including three bugs that look like RCEs.
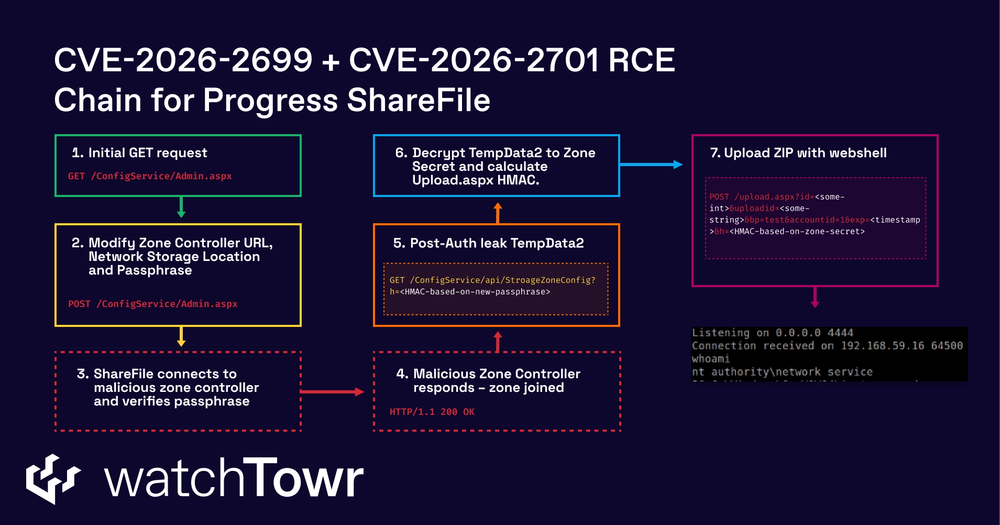
Progress ShareFile pre-auth RCE: Security updates are available for Progress ShareFile servers that patch an authentication bypass and remote code execution vulnerabilities (CVE-2026-2699 & CVE-2026-2701). The two bugs can be combined to upload webshells to unpatched servers. While there are more than 30,000 ShareFile servers available online, only the 5.x branch is vulnerable to attacks.
Infosec industry
Threat/trend reports: Dr.Web, Endor Labs, GreyNoise, KPMG, Recorded Future, and RH-ISAC [PDF] have recently published reports and summaries covering various threats and infosec industry trends.
Acquisition news: Software giant Fortra has acquired cyber training company Zero-Point Security.
KubeCon+CloudNativeCon 2026 videos: Talks from the KubeCon+CloudNativeCon Europe 2026 conference, which took place last month, are available on YouTube.
New tool—SandyClaw: Cloud security firm Permiso has released SandyClaw, a tool that scans OpenClaw skills and assesses their safety.
New tool—ghostsurf: Security firm SpecterOps has released ghostsurf, a tool to relay NTLM auth tokens and then proxy to a victim for browser session hijacking.
New tool—CertGraveyard: A security researcher going by Squiblydoo has released the CertGraveyard, a centralized place to document the abuse of code-signing certificates.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about how incredibly good AI models have gotten at finding and exploiting vulnerabilities. That will upend the cyber security industry and it has implications for state cyber organisations such as NSA and Cyber Command.
We recently launched a new podcast series called Risky Business Features. In this episode, James Wilson is "joined" by one of his OpenClaw AI agents for a chat about whether or not an LLM can understand, modify or even create a sophisticated nation-state grade iOS exploit kit.
