Risky Bulletin Newsletter
April 06, 2026
Risky Bulletin: New Cambodian law will put scam compound operators in prison for life
Written by

News Editor
This newsletter is brought to you by application allow-listing software maker Airlock Digital. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
The Cambodian government passed a new law last week that introduces big fines and heavy prison sentences for the operators and workers of cyber scam compounds.
The new bill passed unanimously in the National Assembly and Senate and was sent to the country's king to be signed into law. It comes after major international pressure from both China and the US for the local government to crack down on its sprawling cyber scam ecosystem.
The law introduces tiered penalties depending on a suspect's roles in the scam operation, such as if they acted alone or part of a larger cybercrime syndicate.
The individuals who ran the scam compounds face the highest fines and prison sentences.
Running a scam compound will get you a prison sentence of five to 10 years, and a fine from 500 million to 1 billion riel ($125,000 to $250,000).
If torture or kidnapping was involved, the maximum sentence goes to 20 years and a fine of 1 billion to 2 billion ($250,000 to $500,000).
If deaths have been reported at the scam compound, operators face up to 30 years or life imprisonment.
Not all scam compounds are staffed with kidnapped people and the law also accounts for willing participants. Individuals who worked on their own volition may also be sentenced up to 10 years in prison and fined 500 million to 1 billion riel ($125,000 to $250,000).
The law also strikes the cyber scam compound supply chains. People who recruit or train compound personnel can face up to five years in prison and be fined 200 million to 500 million riel (about $50,000 to $125,000).
If the "recruits" are tortured, kidnapped, or die during the process, sentences go up to 10 years and the fines to 500 million to 1 billion riel ($125,000 to $250,000).
Suspects who collect and sell personal data to scammers can face up to three years in jail and a fine of 100 million to 300 million riel ($25,000 to $75,000). That punishment goes up if it's done in an "organized" environment, to five years and 300 million to 500 million ($75,000 to $125,000).
Cambodia's new law doesn't cover laundering the proceeds of scam compounds because money laundering is already covered by other laws.
The country has been more susceptible recently to cracking down on cyber scam compounds after it saw a net decline in international tourism as travelers became more weary to visit, fearing they might be kidnapped and forced to work in one of the sprawling compounds.
Over the past months, Cambodian police have intensified their crackdown and shut down tens of scam compounds. Back in February, the government promised to dismantle all scam compounds by April. Back then, it raided over 190 locations, detained 2,500 suspects, and freed more than 110,000 foreigners who worked in the compounds.
Since then, officials also arrested and extradited to China two major figures of its scam ecosystem, Chen Zhi, the chairman of the Prince Group, and Li Xiong, the chairman of the Huione Group. The former ran many of Cambodia's scam centers, while the latter was involved in laundering a huge chunk of its scam profits.
Although some experts doubted the government's resolve in February to crack down on its scam ecosystem, for now, Cambodia seems to be living up to its promise.
Local coverage: Mekong Independent // Kiripost // CamboJA News [h/t J. Tesla]
Risky Business Podcasts
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI.
Breaches, hacks, and security incidents
Italy's top art museum hacked: Italy's top art museum has moved its top items to secure bank vaults after a cyberattack in February. The Uffizi Galleries in Florence hosts the House of Medici art collection, including Leonardo da Vinci, Raphael, and Botticelli paintings. The museum said no passwords or security maps were stolen in the hack and the incident is "nothing like the Louvre." [ANSA // Politico Europe]
Hims & Hers breach: Telehealth company Hims & Hers has disclosed a security breach of its customer support portal. The incident took place in February and hackers are believed to have stolen personal data shared in some support tickets. Hims & Hers sells weight-loss drugs and sexual health prescriptions. [TechCrunch]
DocketWise breach: Hackers have stolen the data of 116,000 DocketWise users. The company develops a cloud-based platform for managing immigration-related cases. Hackers allegedly used login credentials from one of its partners to access its servers. The breach took place last October. [Claim Depot]
Die Linke ransomware attack: German political party Die Linke has shut down its IT network after a ransomware attack at the end of March. The incident was claimed by the Qilin ransomware group. The party says hackers stole employee records but no member data was compromised.
SongTrivia2 leak: Hackers have hacked and published almost 300,000 user details from music quiz game SongTrivia2.
Meta pauses Mercor contract: Meta paused its contracts with AI training platform Mercor after the company disclosed a security breach last week. [WIRED]
Duc leaked PII: Money transfer app Duc has leaked the personal information of hundreds of thousands of users. Scans of passports and driver's licenses were found on an unprotected AWS server. The company secured the server after being notified last week. [TechCrunch]
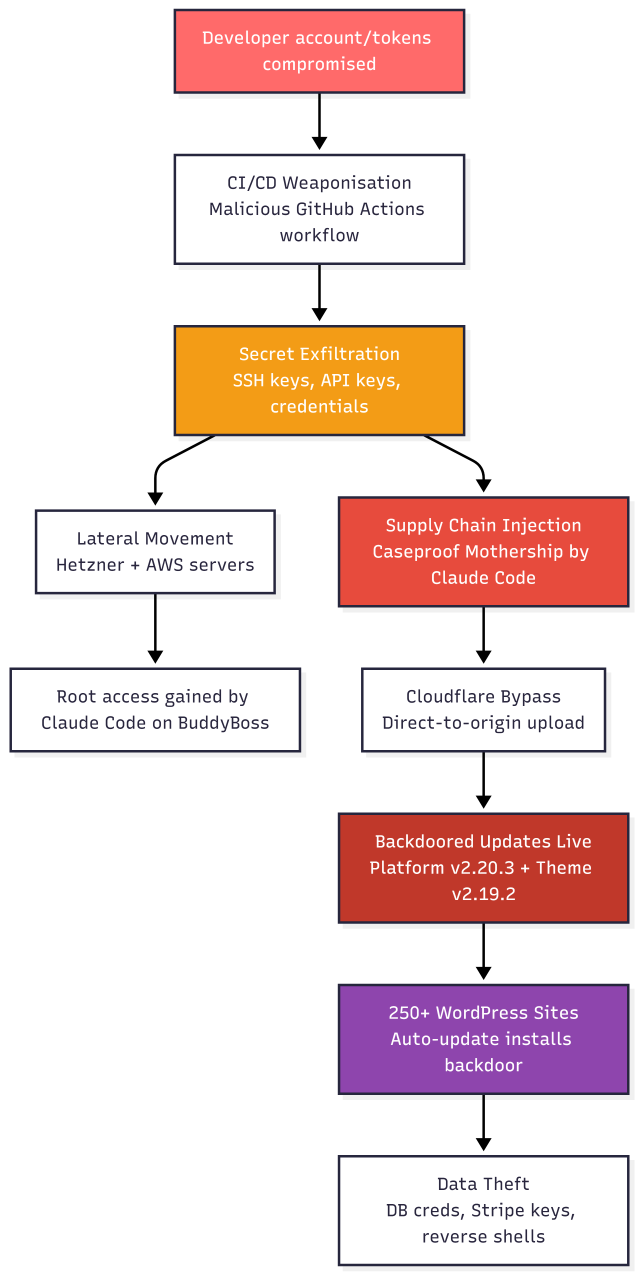
BuddyBoss supply chain attack: A threat actor used Anthropic's Claude agent to carry out a supply chain attack on the BuddyBoss e-learning platform. According to recovered Claude prompts, the attacker instructed the AI agent to use compromised credentials to bypass the developer's security measures and upload a backdoored update package to the BuddyBoss platform. Almost 250 websites were compromised in the attack last month. Most were American universities located in the Middle East. Researchers tracked the attack to a French threat actor. [Ctrl-Alt-Intel part 1, part 2]
General tech and privacy
LinkedIn secretly scans for browser extensions: LinkedIn is allegedly using hidden JavaScript to identify what browser extensions visitors are using. According to a new report, the company is allegedly scanning for thousands of extensions, including over 200 that directly compete with its own sales tools. LinkedIn claims the author of the research is wrong and was previously banned from its site for scraping. It also called the new research an attempt to revive an old lawsuit. [BleepingComputer]
FCC proposes Voxbeam fine: The US Federal Communications Commission has proposed a $4.5 million fine against Voxbeam for routing robocall scams. The agency says the company routed traffic through its network from providers that were not listed on the US Robocall Mitigation Database. Last year, the FCC banned 1,200 voice providers from the US telephone network after failing to deploy robocall protections.
Meta glasses find their niche: Meta's smart glasses are apparently the hottest thing in China when it comes to cheating at exams. They're also being used for live translations and street navigation. [Rest of World]
Trapped in robotaxies: Tens of customers were blocked for hours inside self-driving Apollo go robotaxies in the city of Wuhan last week. The incident was explained as a malfunction, but no other details were provided. [The Guardian]
Peak civilization achieved: Huntress security engineer Adam Rice stored the Doom game in DNS records and then used DNS queries to retrieve and load the game into memory.
IRLid protocol: A new protocol named IRLid is being floated as a possible tech replacement for proof-of-personhood without using biometrics.
Russians migrate to new apps: As the Russian government is cracking down on the use of Telegram, Whatsapp, and VPNs, Russian citizens are slowly moving to other apps that have an IM and video or voice calling feature included, such as KakaoTalk, Duolingo, or dating apps like SOVA. In some cases, even smart cat feeders. [Kommersant] [h/t Vadim R.]
You can get TLS certs with your driver's license now: The CA/B Forum passed a ballot to allow CAs to verify a user via a Mobile Drivers License (mDL) when requesting new certs.
Government, politics, and policy
The Netherlands develops anti-phishing filter: The Dutch government is developing an anti–phishing filter to help telcos block malicious links. The new "Anti Phishing Shield" was tested in a pilot program last year with 200,000 users and blocked more than two million attempts to access malicious sites. The filter was developed by the Dutch government together with banks and telcos. It is similar to a system named BAPS currently in use in neighboring Belgium.
The Netherlands runs a digital sovereignty test: Four Dutch municipalities have entered a pilot program and will test moving their work infrastructure to a Linux and MyOffice setup. The program is part of an effort to move Dutch reliance on US tech. The pilot program will run in the cities of Amsterdam, Ede, Hertogenbosch, and Zaanstad. The four serve almost two million people.
US Army reduces mandatory cybersecurity training: The US Army has reduced the frequency of mandatory cybersecurity training. Soldiers, officers, and civilian personnel will only have to undergo cybersecurity training once every five years, instead of the previous yearly courses. The new policy entered into effect last month. It was enacted following a Pete Hegseth memo last year that aimed to free troops for combat instead of online classes. [DefenseOne]
White House cuts $700m from CISA's budget: The Trump administration wants to cut another $707 million from CISA's budget next year. The cut is about a third of the agency's budget this year. The White House used the same tired and misleading argument that CISA censored political speech as the reason. [CybersecurityDive]
President's FY27 budget request drops around $700 million from CISA
— David DiMolfetta (@ddimolfetta.bsky.social) 2026-04-03T15:00:45.191Z
Sponsor section
In this Risky Business sponsor interview, James Wilson chats with Airlock Digital co-founders, David Cottingham and Daniel Schell, about how they’re moving up the stack from file-based allowlisting to application-based allowlisting. David and Daniel explain how they’re making a seamless and quite logical move into application allowlisting, but with a new take on the technique.
Arrests, cybercrime, and threat intel
Employee hacks and extorts employer: A Missouri man has pleaded guilty to hacking and extorting his employer. Daniel Rhyne deployed scripts that deleted user accounts and shut down servers on his employer's network. He then emailed the company and asked for a 20 bitcoin ransom, which was worth $750,000 at the time of the incident, in November 2023.
Fruitfly malware dev released from jail: A judge has released an Ohio man from jail after spending nine years in pretrial lockup. Philip Durachinsky was arrested in 2018. He was accused of using the Fruitfly spyware to spy on macOS users since at least 2003. The judge released Durachinsky after prosecutors failed to move his case to trial and agreed that he spent enough time in jail already.
FB-ISAO raises threat level: The Faith-Based Information Sharing & Analysis Organization (FB-ISAO) has raised the threat level for its members to "Severe" due to conflicts in the Middle East, Iran, and India. The org says houses of worship are now at high risk of physical and cyber attacks.
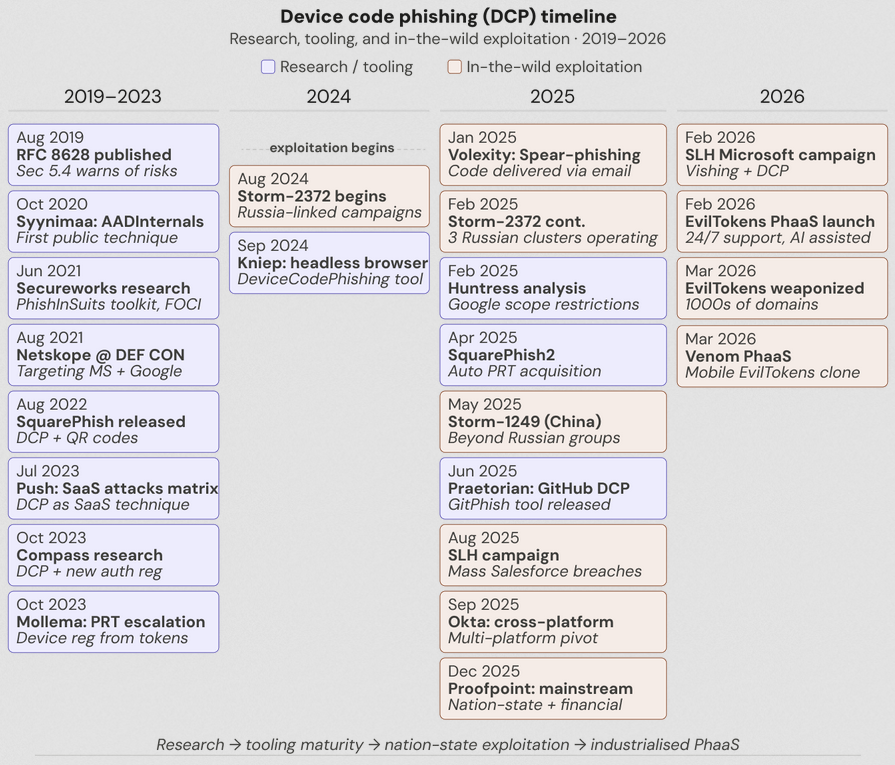
Device code phishing kits proliferate: Device code phishing campaigns have increased by 37.5 times this year, according to Push Security. Attacks that were specific to APT groups last year have now been widely adopted by the e-crime ecosystem. At least 10 distinct phishing kits capable of device code phishing operations have been spotted in the wild. The most popular of these is called EvilTokens, also known as Antibot. The others include the likes of Dolce, DCStatus, Paprika, Flow_Token, DocuPull, Authov, LinkID, Clure, and ShareFile.
Vite scanning: Threat actors are scanning the internet in an attempt to hack apps and websites built using the Vite JavaScript frontend framework. Attacks are exploiting a bug from last year (CVE-2025-30208) that lets them bypass blocklists and retrieve files. According to the Sans Internet Storm Center, hackers are trying to retrieve files that store credentials, environment variables, and cloud tokens.
Major open-source devs targeted by North Korean hackers: High-profile developers from the npm open-source ecosystem have been targeted by the same phishing campaign that compromised the Axios project. Developers behind the main Node.js project, Lodash, Fastify, Mocha, and Express have disclosed attacks on social media. Attackers also targeted engineers at Socket Security, including CEO Feross Aboukhadijeh. The phishing campaign and the Axios supply chain were linked to North Korean hackers. [Socket Security]
This campaign is massive and a great reminder that behind your favorite Open Source dependencies are humans too! I was also targeted, lucky that it takes me years to check my inbox 💀
— Ulises Gascón (@ulisesgascon.com) 2026-04-04T11:27:41.053Z
jokes on them, ignoring my inbox has long been part of my security posture
— jonchurch (@jonchurch.bsky.social) 2026-04-03T22:08:19.440Z
A change in web shells tactics: Microsoft has noted a change in malware trends where more and more PHP web shells are using cookie values for controlling the infected host instead of the classic URL parameters.
Chrome extensions steal browsing history: A popular Chrome extension with more than 400,000 downloads has added malicious code that tracks and collects its users' browsing history. [PiunikaWeb]
New SERPENTINE#CLOUD campaigns: Derp.ca has spotted new campaigns from the SERPENTINE#CLOUD threat actor, the same one spotted by Securonix last year. This time, the group is using ClickFix to drop five different payloads (VenomRAT, AsyncRAT, PureHVNC, XWorm, Brute Ratel).
Claude lure malware campaigns: Trend Micro and Zscaler have published reports looking how threat actors moved rapidly to distribute malware-laced versions of the Claude Code AI agent source code, hours after it leaked online. Payloads included cryptominers, infostealers, and RATS, for all three major desktop operating systems.
Nova RaaS interview: Threat intelligence analyst Marco A. De Felice has published an interview with the operator of the Nova Ransomware-as-a-Service platform. The RaaS launched in April of last year.
Sus IP registrations: A Chinese national has registered at least 28 fiber internet service providers in the UK over the past months. The individual is also the point of contact for a Chinese residential proxy provider named OnesProxy. Security firm Spamhaus says no traffic has originated from the ISPs so far.
Malware technical reports
Phorpiex botnet, Twizt variant: A new version of the Phorpiex (Trik) botnet has infected between 70,000 and 80,000 Windows devices. The new version has already been used to deploy the Global and LockBit Black ransomware. It was also used to send massive waves of sextortion emails. The Phorpiex botnet first emerged in 2011 and survived several takedown attempts. The new variant is tracked as Twizt to distinguish it from previous versions of the botnet.
AMOS variant: Pablo Redondo Castro looks at a new macOS infostealer, which he describes as likely a new variant of the older AMOS infostealer.
Cifrat: Poland's CERT has reverse-engineered a new Android RAT that was being spread in Poland using Booking lures.
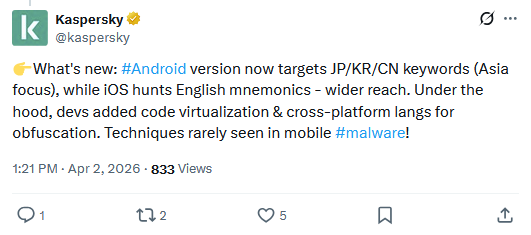
SparkCat returns: SparkCat, the Android and iOS malware that uses OCR to steal crypto-wallet seed phrases, has returned with new versions, per a Kaspersky tweet.
Sponsor section
In this product demo of the Airlock Digital application control and allowlisting solution, Patrick Gray speaks with Airlock Digital co-founders David Cottingham and Daniel Schell.
APTs, cyber-espionage, and info-ops
Axios supply chain attack linked to Bluenoroff: Security firms DCSO and Hunt Intelligence have linked the Axios supply chain attack on a North Korean APT named Bluenoroff. Google previously attributed the attack to UNC1069, a suspected North Korean threat actor. APT naming schemes and cluster visibility… go figure!
New Kimsuky campaign: AhnLab and Fortinet have published technical reports on a Kimsuky phishing campaign leveraging malicious LNK files to deploy malware.
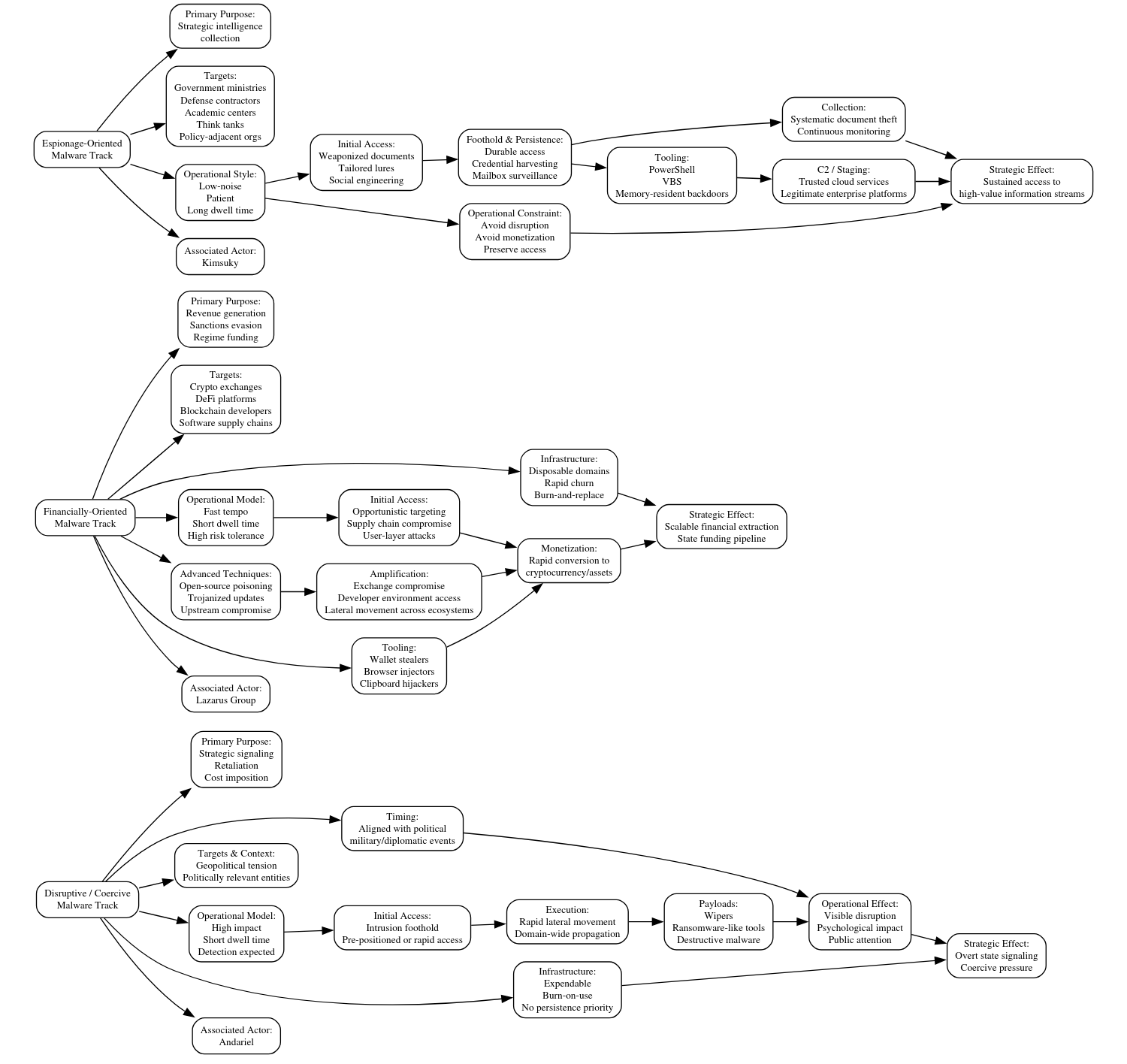
DPRK malware overview: The DomainTools security team has published a report looking at how North Korean hackers have diversified and deliberately split their malware dev into three main categories—for espionage, e-crime, and disruptive attacks.
OtterCookie: And speaking of DPRK malware, the Cyber and Ramen crew published a technical analysis of a recent version of the OtterCookie backdoor found being spread via malicious npm packages.
Winnti Linux variant: Breakglass Intelligence looks at a new Linux variant of the good ol' Winnti backdoor, a common tool of Chinese APTs.
"The sample – a 2.7 MB x86_64 ELF binary obfuscated to near-maximum entropy – connects to three C2 domains that all typosquat Chinese technology companies, resolving to a single Alibaba Cloud IP in Singapore that has been invisible to Shodan for over two years. The backdoor harvests cloud instance metadata from AWS, GCP, Azure, and Alibaba Cloud workloads. And it uses SMTP port 25 as a covert command channel. This is what a well-funded nation-state implant looks like when the operators know what they're doing."
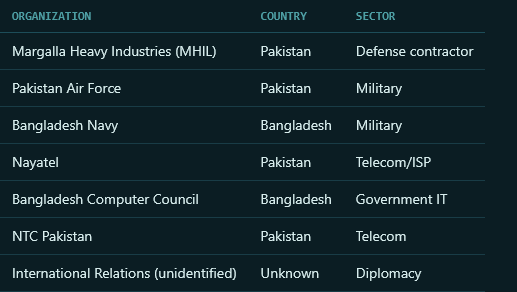
New SideWinder LotL campaign: Indian APT group SideWinder has spent five months breaking into the militaries and defense organizations of Bangladesh and Pakistan. The operation involved phishing portals and malware-laced files hosted on multiple legitimate services. At least six targets have been identified so far.
Sputnik survives in Czechia: After the EU sanctioned Russia's Sputnik news network, its Czech division did a ransomware and rebranded as 42TČen to avoid sanctions.
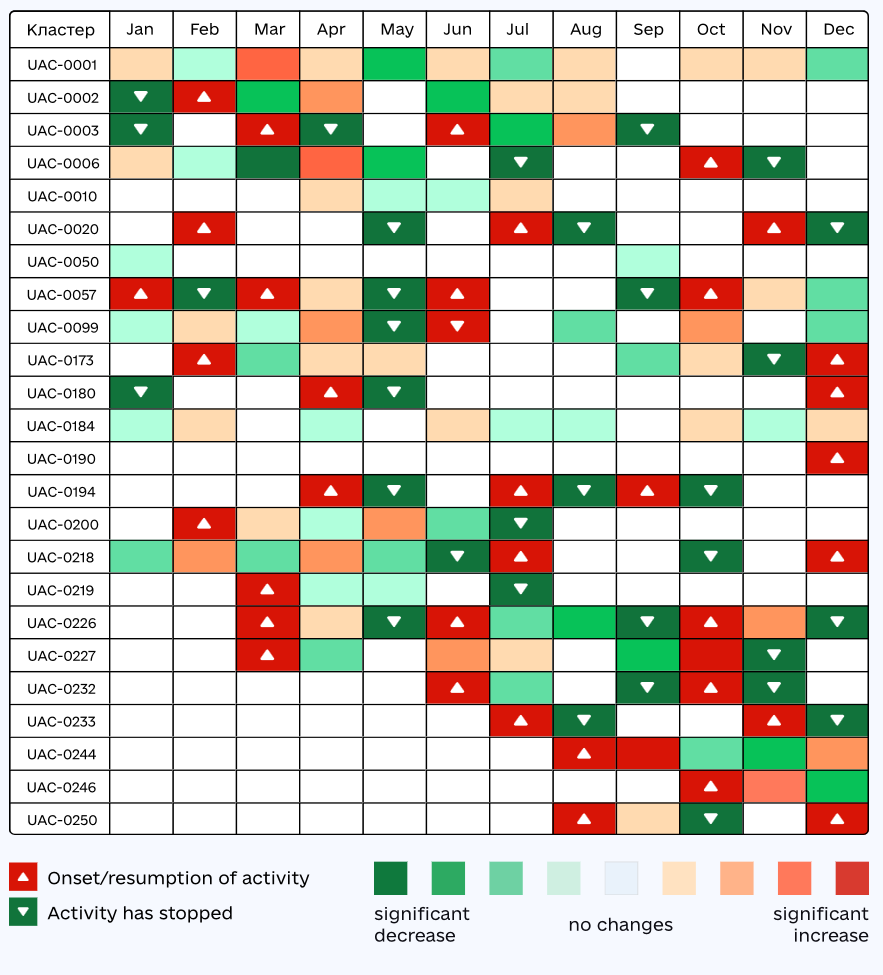
Ukraine landscape: Ukraine's CERT has published a report looking at cyberactivity in the country in the second half of last year. The predominant trend was Russian groups revisiting networks they hacked earlier in the year to verify their access or carry out new operations. [The Record]
Vulnerabilities, security research, and bug bounty
Recent security updates: Kubernetes, OpenSSH.
New CWP RCE: There's a new unauth remote code execution bug in the CentOS Control Web Panel web hosting toolkit, tracked as CVE-2025-70951, that will need patching in the coming days.
GPUBreach attack: A team of academics has developed a GPU-based Rowhammer attack that can elevate privileges and obtain root access on Linux systems. The GPUBreach attack corrupts the GPU memory page tables and then moves to the CPU via the NVIDIA driver to gain full access over the OS. Academics first ported Rowhammer attacks on the GPU last year. Rowhammer attacks compromise memory data by repeated write operations to the same row of memory cells. Most Rowhammer attacks are uncontrollable.
New Fortinet zero-day: Fortinet has released an emergency security update on Saturday to patch an actively exploited zero-day. Tracked as CVE-2026-35616, the vulnerability allows remote attackers to bypass authentication and run malicious code on Fortinet EMS servers via malcrafted requests. Attacks against Fortinet EMS devices spiked last month as a threat actor began exploiting an older February bug. The two are likely related as the zero-day was reported by security firm Defused, which spotted the first wave of attacks.
ICYMI yesterday, the Easter bunny brought us a Fortinet zero day! 🐣 decipher.sc/2026/04/04/f...
— Dennis (@dennisf.bsky.social) 2026-04-05T15:34:54.872Z
Evergreen
— Golden Retrievers Despise Supporters Of Fascism (@zarchasmpgmr.bsky.social) 2026-04-05T17:34:44.183Z
Infosec industry
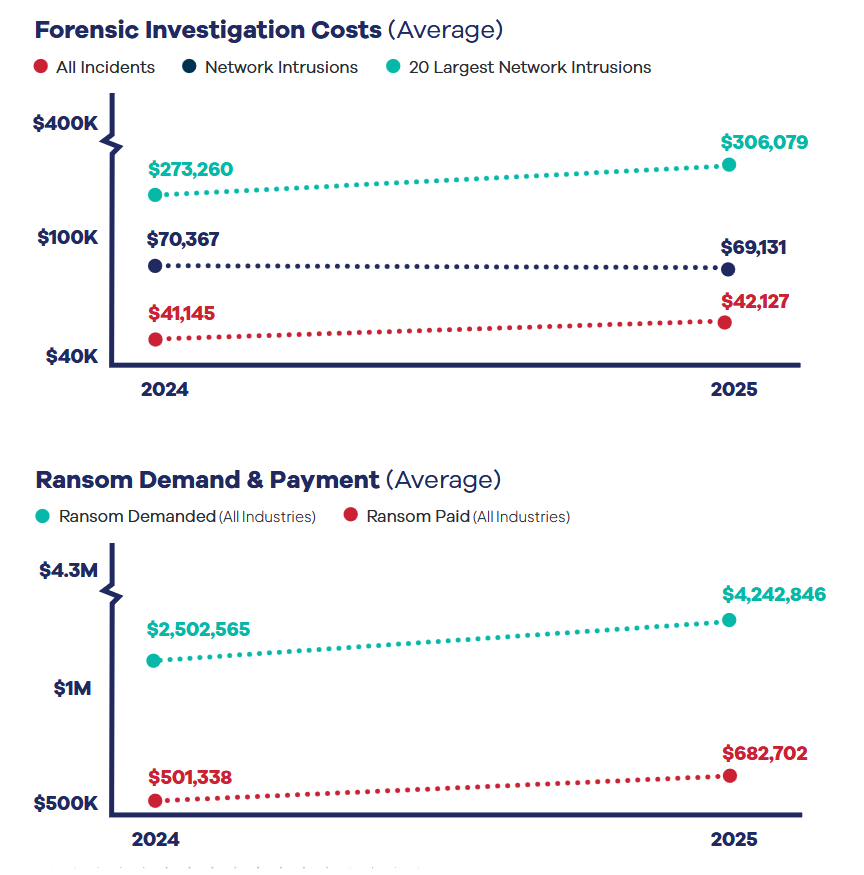
Threat/trend reports: BakerHostetler, CERT-UA, Dr.Web, Health-ISAC, Recorded Future, and Sucuri have recently published reports and summaries covering various threats and infosec industry trends.
Hyppönen profile: Lorenzo at TechCrunch has a profile on Mikko Hyppönen, the Finnish infosec veteran that switched from reversing malware to hacking drone technologies.
Brundage profile: WSJ's Robert McMillan also published a profile on Benjamin Brundage, the college student who founded Synthient and helped track the Kimwolf botnet.
New tool—Vespasian: Security firm Praetorian has open-sourced Vespasian, a probabilistic API endpoint discovery, enumeration, and analysis tool.
New tool—SightHouse: Security firm Quarkslab has released SightHouse, a tool designed to assist reverse engineers by retrieving information and metadata from programs and identifying similar functions.
New tool—sim-unpacker: Rostelecom's security team has published sim-unpacker, a tool to unpack Windows installers created with Smart Install Maker, sometimes also abused to pack and bundle malware.
New tool—Supply Chain Monitor: Elastic's security team has released Supply Chain Monitor, an internal tool that monitors top npm and PyPI packages for supply chain compromises, a tool that also caught the recent Axios incident.
BSides Tallin 2025 videos: Talks from the BSides Tallin 2025 security conference, which took place last September, are now available on YouTube.
Risky Business podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
We recently launched a new podcast series called Risky Business Features. In this episode, James Wilson chats with Brad Arkin (former CISO of Adobe, Cisco and Salesforce) to talk about the mounting pressure that CISOs are under in the AI era. Attackers are operating at unprecedented scale, and internal users are adopting AI faster than security teams can keep up. This requires CISOs to bend on things that would have otherwise been a hard-no in the past, and revisit some fundamental controls that might have seemed too difficult previously.
