Risky Bulletin Newsletter
March 11, 2026
Risky Bulletin: Gen. Joshua Rudd confirmed as next CyberCom and NSA head
Written by

News Editor
This newsletter is brought to you by Thinkst, the makers of the much-loved Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
The US Senate has confirmed Army Lt. Gen. Joshua M. Rudd as the next leader of US Cyber Command and the National Security Agency.
Gen. Rudd was confirmed in a 71-29 vote on Tuesday.
He will replace Army Lt. Gen. William Hartman, who is serving as interim chief for both agencies.
Both CyberCom and NSA have been without a Congress-approved leader since President Donald Trump fired Air Force Gen. Timothy Haugh last April.
Gen. Rudd emerged as a favorite for the job in November of last year and replaced Gen. Hartman as the White House's favorite candidate. Prior to his nomination, he was serving as deputy chief of US Indo-Pacific Command.
His opponents cited his previous role as a main deterrent for a vote, claiming he had almost no prior expertise in cyber and intelligence operations.
Gen. Rudd's confirmation comes as the US has embroiled itself in two military conflicts this year. In both engagements, Cyber Command claimed it carried out operations to disrupt enemy systems.
Sorry for the short intro/lede item today, but I was without internet most of the day :(
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Theft traced back to M365 misconfiguration: The government of Western Australia used poorly configured Microsoft 365 security controls that allowed hackers to breach its systems last in 2024. A report from the state's auditor found that government agencies used legacy authentication methods, weak MFA methods, and had failed to enable DLP controls. These led to incidents where the data of state residents, including minors, were leaked and later stolen. Hackers also stole ASD$71,000 from a state account following a BEC attack. [iTnews]
Cyberattack on Colombia's election agency: Cyberattacks have hit Colombia's election agency during the country's parliamentary elections on Sunday. Officials didn't describe the nature of the attacks. They also reported a surge in clone sites pushing fake news and election results. [Zona Cero // Meyka]
Incident at Halifax Water: Canadian water utility provider Halifax Water is investigating a possible breach of its online customer portal. [CBC]
Kubernetes-el incident: A hacker exploited the Pwn Request vulnerability to hack the GitHub repo of Kubernetes-el, a popular Emacs package for managing Kubernetes clusters. [Step Security]
GitHub action delivers a reverse shell: A threat actor has compromised the Xygeni GitHub action to deploy reverse shells in all the projects that use it. [Step Security]
General tech and privacy
New BlueSky CEO: Former Automattic CEO Toni Schneider has replaced Jay Graber as BlueSky CEO. Graber will move to the Chief Innovation Officer role.
Twitter (X) suspends 800m accounts: Twitter claims it suspended more than 800 million accounts over the past year for spam and manipulation. Most of the accounts were from Russia, followed by Iran and China. The claim is a little bit outlandish since Twitter reports having 300 million monthly active users. [The Guardian]
Microsoft tests Entra passkey support: Microsoft will roll out later this month support for passkeys in its Entra authentication service. This is still at a public preview stage and broad availability will likely follow later in the year or even next year.
Windows Hotpatch to be enabled by default: Microsoft will turn on Windows hotpatching by default for all eligible devices in May. The feature installs security updates without restarting the entire Windows OS. Windows Hotpatch launched on Windows 11 last April.
Microsoft to tag Teams bots: Microsoft will start tagging bot accounts and block them from automatically joining Teams meetings. Organizers will have to manually approve each bot from the lobby screen.
Government, politics, and policy
New US inter-agency cyber body: The Trump administration plans to establish a new inter-agency body to go after foreign hackers attacking the US. The cell will focus on offensive cyber operations and will include representatives from the Pentagon, the FBI, and the Justice Department. The new group will follow principles set out in the new US Cyber Strategy released last week. The document gives the green light to carry out offensive cyber operations and to use private security firms for said operations. [CyberScoop]
UK announces Online Crime Centre: The UK government is launching its own inter-agency cell dedicated to fighting online fraud. The new Online Crime Centre will launch in April and will be led by the Home Office and the National Crime Agency. It will focus on online fraud and high-volume cybercrime. The OCC will have a budget of £31 million and will work closely with telecoms and tech platforms to detect and block fraud operations before they contact users. [The Record]
Overlapping US cyber regulations: A GAO report found that the US has many overlapping cyber regulations that confuse companies about various rules and reporting requirements. [CybersecurityDive]
Data breach reporting lag in Canada: Canadian federal agencies take on average 259 days (just over 8 months) to report privacy breaches even if the country has a seven-day reporting timeframe. Some institutions took more than four years to report incidents to Canada's privacy commissioner. Canada introduced the seven-day reporting requirement in 2022, four years ago. [The IJF] [h/t Alex Rudolph]
Alberta throws money at the problem: The Alberta government in Canada has allocated CAD$40 million (~USD$29.5 million) for software updates after seeing a spike in cyberattacks. Officials plan to upgrade at least 66 legacy applications. Some of the systems are public facing. [CBC] [h/t Alex Rudolph]
Canada reverses TikTok ruling: The Canadian government has lifted a ban it imposed on TikTok in 2024 and will allow the company to reestablish a Canadian subsidiary.
Finland releases national security report: Finland's intelligence service has released its yearly national security overview report. On the cyber side of things, SUPO warns startups that foreign espionage can rob them of their future. The report cites China and Russia as main culprits for most cyberespionage and influence operations activity.
Sponsor section
In this Risky Business sponsor interview, Marco Slaviero, CTO of Thinkst, talks to Tom Uren about how the company ensures that it is a learning organization.
Arrests, cybercrime, and threat intel
US seizes crypto platform: The US DOJ has seized cryptocurrency investment platforms StarPronto and SloGem.
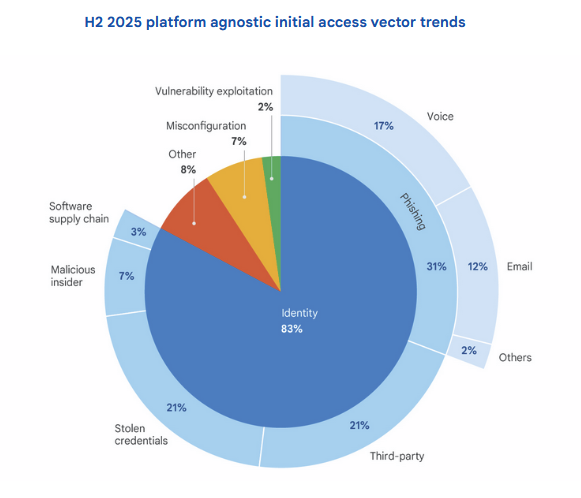
Vulns were the main entry point into GCP servers: The exploitation of software vulnerabilities has overtaken the abuse of weak credentials as the leading entry point into Google Cloud environments for the first time. Google says attacks against third-party software installed on customer servers accounted for almost half of all intrusions in the second half of last year. Ever since Google started tracking these stats two years ago, GCP customer instances have been compromised mainly because clients used weak or no passwords. Google also reported seeing LLM-driven attacks during last year
New Salesforce hacking campaign: Threat actors are using a modified security tool to break into Salesforce customer accounts and steal sensitive data. The attacks leverage a version of AuraInspector, a Salesforce server scanner developed by Google Mandiant after a similar wave of attacks. Salesforce says hackers are using the tool to mass-scan the internet for Experience Cloud servers that have been misconfigured and left exposed online. The hackers also allegedly modified the tool with new features to automate the theft of customer data.
Phishing ops impersonate local officials: Threat actors are running specialized and very detailed phishing operations posing as local city and county governments. The FBI says the emails often include very accurate information on zoning, permits, and city officials. Some of the campaigns have also been timed to coincide with changes in local policies or city communications. The emails typically lure victims on payment sites operated by the threat actors.
Phishing op traced back to Moroccan national: Security researcher Inti De Ceukelaire has traced a phishing operation targeting European banks to an individual in his early 20s from Morocco.
"Interestingly, that backup contained the scammers’ personal access logs with multiple residential IP addresses from Morocco and one from a university in France accessing the panel months before it went live. Since Argenta does not operate in Morocco or France, these early logins were unlikely to be victims."
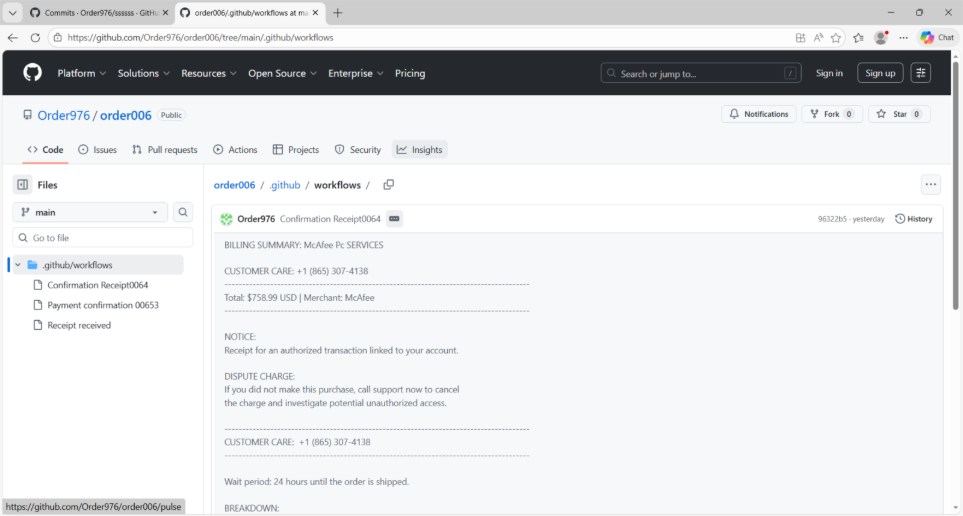
GitHub abused for vishing: Threat actors are abusing the GitHub notification system to deliver voice phishing lures that urge targets to call a support number mentioned in the message.
AWS Console phishing operation: DataDog is tracking an AitM phishing campaign targeting the AWS Console login panel, with submitted credentials being abused as fast as 20 minutes after compromise.
Fortinet hacks: SentinelOne has published some of its threat intel from IR engagements at companies hacked using recent FortiGate vulnerabilities.
Malicious npm package: SafeDep has found a malicious npm package impersonating a popular package that would steal environment files from infected hosts. These files typically contain credentials used for a project's infrastructure.
And another one: There's also this malicious npm package impersonating OpenClaw that deploys the new GhostLoader.
Facebook malvertising leads to investment scams: Tens of thousands of Facebook ads have redirected users to a network of investment scam portals. The campaign targeted users in 15+ languages across 25 countries. The initial ads typically use altered news headlines to lure victims on the scam sites. According to Bitdefender, the scammers appear to be Russian-speaking individuals.
ClickFix hosting: Rapid7 looks at a network of hacked WordPress sites that are being used to host ClickFix operations.
ClickFix campaign leads to Deno abuse: Malwarebytes has spotted a ClickFix malware distribution campaign dropping malware that deploys the Deno JavaScript runtime to execute code outside the purview of security software.
New ClickFix variant targets the Windows 11 Terminal: You always learn new things… and today is a new ClickFix variant that instead of the Windows command line targets the Windows 11 Terminal app. (via the Windows security team)
Microsoft Defender Experts identified a widespread ClickFix social engineering campaign in February 2026 leveraging Windows Terminal as the primary execution mechanism, rather than the traditional Win + R → paste → execute technique.
— Microsoft Threat Intelligence (@threatintel.microsoft.com) 2026-03-05T22:59:27.705Z
Malware technical reports
TaxiSpy RAT: CyFirma looks at TaxiSpy RAT, a new Android remote access trojan targeting Russian banks and financial institutions (for now).
BeatBanker: Also in Android malware, Kaspersky discovered BeatBanker, a new banking trojan targeting Brazilian banks that also comes with a cryptomining component. In some recent campaigns, the threat actor behind this has also started dropping the BTMOB Android RAT on infected devices.
VioletRAT: SonicWall's security team looks at a campaign spreading VioletRAT, a new Windows remote access trojan.
ClipXDaemon: Researchers at Hive Pro have discovered ClipXDaemon—what appears to be the first clipboard hijacker that targets Linux users. The malware works like similar Windows alternatives. It intercepts the operating system copy-paste clipboard and replaces cryptocurrency addresses with ones controlled by an attacker.
A0Backdoor: A threat actor is using email bombing and IT-support impersonation over Microsoft Teams to trick corporate employees into infecting themselves with the new A0Backdoor.
Coruna exploit kit traced back to L3Harris: The Coruna iOS exploit kit that was exposed by Google last week is the work of American company L3Harris. Two former employees have told TechCrunch that Coruna resembles tools developed by L3Harris subsidiary Trenchant. A former Trenchant executive was sentenced to seven years in prison for selling his employer's exploits to a Russian zero-day broker. The report doesn't confirm that Coruna are the tools that the former Trenchant executive sold.
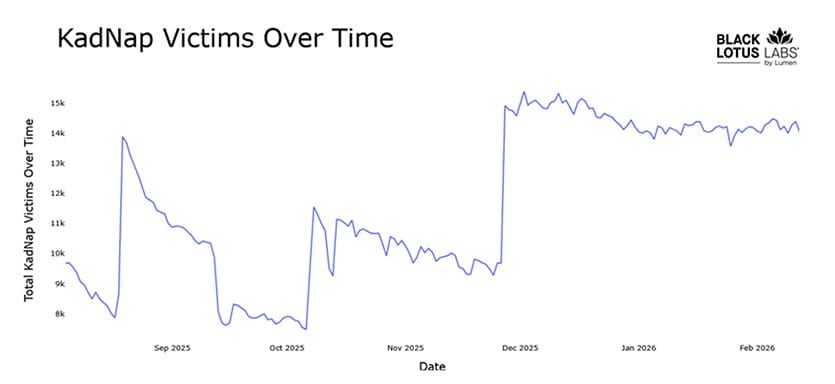
KadNap botnet: A new botnet has infected more than 14,000 devices since August of last year. Devices infected with the KadNet botnet are sold via an anonymous residential proxy service named Doppelganger. According to Lumen's security team, most of the infected devices are Asus routers.
Sponsor section
In this Soap Box edition of the podcast, Patrick Gray chats with Thinkst Canary founder Haroon Meer about his "decade of deception."
APTs, cyber-espionage, and info-ops
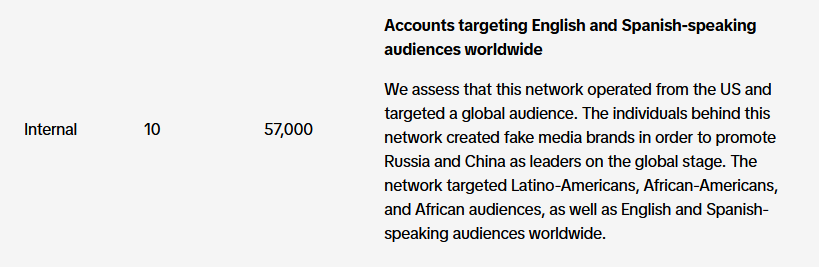
TikTok info-ops summary: TikTok has published its monthly report on covert influence operations the company has spotted on its platform in December last year. The company took down influence networks targeting political discourse in Hungary and Poland. The Hungarian network promoted Viktor Orban's party while the Polish one promoted Poland's exit from the EU. The largest cluster was a campaign operated from China that targeted global audiences with pro-CCP messaging. There was also this network operated from within the US.
Camaro Dragon targets Qatar: A Chinese APT group started targeting Qatar as soon as the US and Israel began their attacks on Iran last week. Camaro Dragon quickly adopted images from the strikes to lure targets on opening malware-laced files. The group was previously focused on Southeast Asia.
MuddyWater: Huntress looks at a MuddyWater intrusion at an Israeli company back in January that began via a compromised RDP endpoint.
Iranian APTs and cybercrime tools: Check Point has a handy report that looks at all the connections between Iranian APTs and the cybercrime ecosystem, and the tools they rent from it.
Russian hackers target Signal, WhatsApp: Russian state hackers have launched a global campaign to compromise the Signal and WhatsApp accounts of foreign diplomats and military personnel. Dutch intelligence agencies confirmed attacks against the country's officials. The attacks try to trick victims into sharing security codes. The codes are later used to grant an attacker device access to a victim's account and spy on their communications.
These attacks, like all phishing, rely on social engineering. Attackers impersonate trusted contacts or services (such as the non-existent “Signal Support Bot”) to trick victims into handing over their login credentials or other information. 3/7
— Signal (@signal.org) 2026-03-09T16:12:11.495Z
New Sednit/APT28 malware: ESET takes a closer look at the new malware Russian APT group Sednit (APT28) has been using over the past three years, such as slimAgent, BeardShell, and Covenant (actually an open-source red-team tool abused by the group).
Doppelgänger error exposes domain network: After a source provided German journalist Hakan Tanriverdi with a backend dump of a Russian disinformation website, he used a weird string in the code to uncover more than 100 domains in the same network, all linked to a group known as Doppelgänger. [readwrite]
Shoutout to the reader/researcher who reached out to say that all of the four su-domains showing up are registered with the same mail address
— hakan (@hatr.bsky.social) 2026-03-10T15:16:26.784Z
Vulnerabilities, security research, and bug bounty
Patch Tuesday: Yesterday was the March 2026 Patch Tuesday. We had security updates from Adobe, Microsoft, IBM, Dell, SAP, HPE, Fortinet, Ivanti, Intel, Firefox, Moxa, Schneider Electric, and Siemens. Other projects and companies like Cisco, Chrome, Android, Samsung, Qualcomm, Arm, Zoom, Drupal, Django, pac4j, and WatchGuard released security updates earlier this month.
Microsoft Patch Tuesday: This month, Microsoft patched 79 vulnerabilities. There were no actively exploited zero-days patched this month.
New Ivanti exploitation: Hackers are exploiting a new authentication bypass vulnerability in Ivanti's Endpoint Manager platform. Tracked as CVE-2026-1603, the vulnerability was patched at the start of February. CISA has added the bug to its database of actively exploited bugs on Monday after receiving reports of ongoing attacks. It was one of three new bugs added to the KEV DB.
SKCET vulnerabilities: Security researcher Eaton Zveare has an interesting write-up on a bug he found in the admissions portal of a major Indian technical college.
"This vulnerability made me sad. If the college itself forgets about API authentication, is it also missing from the curriculum?"
Fortinet SQLi write-up: BishopFox goes on a deep dive into CVE-2026-21643, an SQL injection patched last month in the FortiClient EMS, Fortinet's centralized management server.
LeakyLooker vulnerabilities: Google has patched nine vulnerabilities in the Looker Studio business insights and visualization service. The vulnerabilities could have allowed attackers to escape tenants and steal data from other Google customers. The flaws exploited database connectors that fed data into the service.
Infosec industry
Threat/trend reports: Check Point, Google Cloud, ISC2, and SUPO have recently published reports and summaries covering various threats and infosec industry trends.
DefensePrime shuts down, reopens in Spain: American spyware maker DefensePrime has shuttered its Florida company and transferred its assets to a company in Barcelona, Spain. The company is known for being staffed with former NSO devs and trying to acquire Israeli spyware rival Quadream. The company was also known as Palm Beach Networks and listed former NSA head Retired General Keith Alexander as chairman. [Intelligence Online]
When spyware shops “close” in Florida and reopen in Spain, that’s not failure. It’s jurisdictional laundering. Same operators, same trade, new flag. The tell isn’t the shutdown—it’s who always lands on their feet.
— geeknik (@geeknik.bsky.social) 2026-03-07T23:29:08.000Z
Acquisition news: OpenAI has acquired AI security platform Promptfoo.
DarkTrace has a new CEO: British threat intel firm DarkTrace named Ed Jennings as its new CEO.
New tool—Codex Security: OpenAI launched Codex Security in preview, an AppSec-centered AI agent.
New tool—VulHunt: Security firm Binarly has open-sourced a community edition of VulHunt, its binary vulnerability hunting framework.
New tool—Bromure: Tenable co-founder Renaud Deraison has released Bromure, an ephemeral Chromium browser that runs in a disposable macOS virtual machine.
New tool—Electric Eye: Security researcher Gabriel Biondo has published Electric Eye, a Firefox add-on to detect AitM phishing attacks in real-time.
"Electric Eye analyses TLS fingerprints, HTTP headers, and DOM content to detect proxy anomalies. Detection runs locally in WebAssembly — no data leaves your browser."
New tool—PrivHound: Security researcher Arun Nair has open-sourced PrivHound, a BloodHound module to show Windows local privilege escalation as interconnected attack paths.
BSides Budapest 2025 videos: Talks from the BSides Budapest 2025 security conference, which took place last May, are available on YouTube.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about why an internet shutdown won't stop US cyber operations in Iran.
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about how cyber operations were used in the first hours of the US-Israeli attack on Iran. They were instrumental in the attack on Iranian Supreme Leader Ali Khamenei, but they didn't last long. The Iranian regime implemented an internet blackout within four hours of the first bombs.
