Risky Bulletin Newsletter
April 02, 2025
Risky Bulletin: DPRK worker scheme expands to Europe after US crackdown
Written by

News Editor
This newsletter is brought to you by Kroll. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
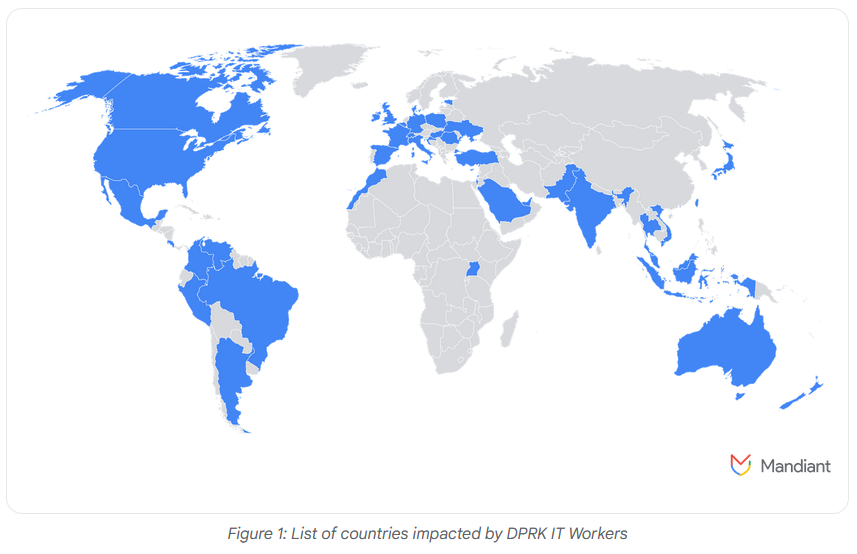
North Korean IT worker schemes have expanded globally and are now heavily targeting European companies after a crackdown from US authorities last year.
Towards the end of 2024, North Korean workers started creating fake personas tailored for the European job market and seeking IT jobs at European small and large tech giants.
In a report this week, Google's security teams say they've spotted at least 12 fake personas linked to the Pyongyang regime.
These fake personas sought employment at companies in Europe's defense industrial base and government sectors.
Google says it also discovered "facilitators" for the European market, a term that refers to people who host laptop farms in Europe so North Koreans can pass as locals—with one facilitator found located in London.
Resources found by Google analysts include instructions on how North Korean workers could search the EU job market, the contact information for a broker specializing in creating false passports, and information on the proper use of European timezones.
The tactics of these workers are identical to what has been seen in the US last year. North Korean IT workers are tasked with obtaining as many remote IT jobs as possible, sometimes working multiple jobs at once, obtaining a salary, usually paid in cryptocurrencies, which then gets sent back to North Korean authorities to be used for the development of its weapons program.
The FBI warned last year that in some cases, such as early termination, some workers have also engaged in extorting former employers.
Google says that after US authorities started warning companies, arresting laptop farm operators, and exposing its DPRK IT workers, the North Koreans have turned up the aggression and ramped up extortion operations.
"GTIG [Google Threat Intelligence Group] assesses that since late October 2024, IT workers have increased the volume of extortion attempts and gone after larger organizations. In these incidents, recently fired IT workers threatened to release their former employers' sensitive data or to provide it to a competitor. This data included proprietary data and source code for internal projects. The increase in extortion campaigns coincided with heightened United States law enforcement actions against DPRK IT workers, including disruptions and indictments."
A similar report from insider risk management company DTEX echoes the same warnings of the Google report—warning that DPRK IT worker schemes have now expanded globally.
DTEX co-founder and president Mohan Koo told CyberScoop in an interview this week that 7% of their customers are running investigations related to accidental hires of North Korean remote workers.
"Some of the roles that we're investigating, the infiltrators that we're investigating right now, have actually got the keys to the kingdom, Koo said. They have privileged-access rights. They have the ability to turn on access and turn off access for other workers. They have the ability to install and uninstall software. They have the ability to write code."
The problem is far larger than people realize and primarily impacts large corporations where HR departments are in constant need of new IT workers or startups that lack proper hiring procedures and are desperate for cheap labor.
Outside of KnowBe4 and HYPR, most companies have kept their intrusions and accidental hires secret, but the list is long if you ever listen to anyone following these operations. Content moderation platform Cinder said in a similar report that around 80% of job applicants last year were suspected North Korean IT workers, or at least gave a vibe they might be using a fake persona. A random CoinDesk investigation last year found 12 crypto-related companies that hired North Korean IT workers last year, and that investigation was conducted by non-experts.
Resources on how to identify DPRK workers in your company are available from several security vendors, including Palo Alto Networks, Google Cloud, DTEX, Recorded Future, and the UK government [PDF].
Tracking these groups down should be easy, but Google also warns that workers are now choosing to go after companies that rely on virtualized infrastructure, where remote staff work inside virtual machines. This allows insiders to hide their tracks better, compared to the old scenario of having to find a laptop farm to host a physical laptop delivered by the employer and having to match the fake persona's location with the laptop farm's general geographic location.
Risky Business Podcasts
Risky Business is now on YouTube with video versions of our main podcasts. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Check Point data breach: After a threat actor published some of the company's data on a hacking forum, Check Point confirmed the breach but said the attacker stole the data of only three customers.
APIsec leak: API testing company APIsec has leaked customer data after leaving an internal database exposed on the internet without a password. The leak lasted for several days and exposed customer names, email addresses, credentials, and other technical details. Some APIsec employee details were also exposed. The company has since secured the exposed system. [Additional coverage in TechCrunch]
Russian railway disruptions: Russia's state-owned railway and the Moscow subway system suffered IT disruptions on Monday due to suspected cyberattacks. Travelers were unable to access official websites and apps and purchase tickets. Both incidents are believed to be DDoS attacks and the work of Ukrainian hacktivists. The attacks are likely retaliation for a Russian cyberattack that crippled the websites and apps of Ukraine's state railway last week.
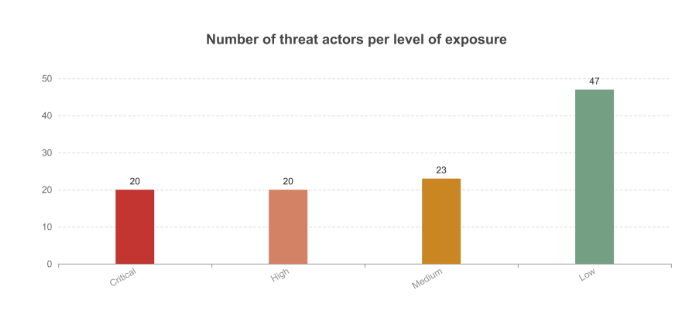
EU cyber incidents: Twenty of the 110 threat actors who attacked EU institutions last year successfully breached their targets. CERT-EU says most of the attacks were cyberespionage-related. Five of the attackers are new groups the agency had not seen before. Five incidents involved the use of a zero-day as the initial access point.
General tech and privacy
Thunderbird will launch webmail service: The Thunderbird email client project has announced a major expansion of its project, which will soon launch a webmail service, along with a universe of connected apps, such as an appointment calendar, a file sharing service, and an AI assistant.
Trae secret extensive data collection system: Security firm Unit221B has found an "extensive data collection system" inside Trae, an AI coding assistant from TikTok's parent company ByteDance.
PQC in OpenJDK: The OpenJDK project has released JDK 24. The new version supports PQC algorithms (ML-KEM and ML-DSA) that can protect data against quantum computing attacks. It also removes the ancient Security Manager module.
"The Security Manager has not been the primary means of securing client-side Java code for many years, it has rarely been used to secure server-side code, and it is costly to maintain."
OpenSNP shuts down citing rise in authoritarian regimes: OpenSNP, an open-source database of genetic information, is shutting down, citing "a rise in far-right and other authoritarian governments." The project plans to delete all user data at the end of the month, on April 30. OpenSNP founder Bastian Tzovaras said the project's biggest adopters were not scientific research groups but law enforcement agencies. Tzovaras fears the project's genetic data may end up being used for repression purposes.
Apple fined €150 million in France: France's competition authority has fined Apple €150 million for anti-competitive practices over the implementation of an iOS privacy feature. The agency says the introduction of the App Tracking Transparency (ATT) framework led to multiple consent popups being displayed to iOS users. Authorities say this made using non-Apple third-party apps "excessively complex" and punished app developers and online advertisers.
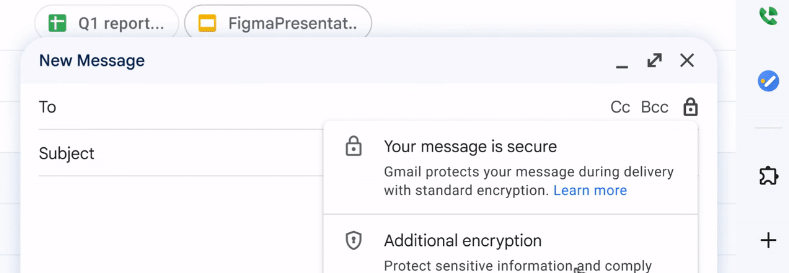
Gmail rolls out E2EE for enterprise users: Google is adding support for sending end-to-end encrypted emails for Gmail enterprise users. The feature will be easily accessible through the Gmail interface and will not require the use of any additional software or special configurations. Support for encrypted emails has already rolled out this week for emails sent in the same organization. Gmail users will be able to send encrypted emails to other Gmail users in the next weeks and to any email address by the end of the year.
Government, politics, and policy
White House extends cyber national emergency EO: The White House has extended the executive order that declared a cyber national emergency. The order allowed US government agencies to sanction foreign hackers and individuals and companies aiding their operations. The executive order was initially signed by President Barack Obama in 2015 and was frequently extended over the past years. It was set to expire yesterday, on April 1.
CyberCom hunt-forward missions in LATAM: According to retired Lt. Gen. Dan "Razin" Caine, CyberCom hunt-forward missions in LATAM have helped the US military uncover new Chinese malware. [Additional coverage in DefenseScoop]
Sponsor section
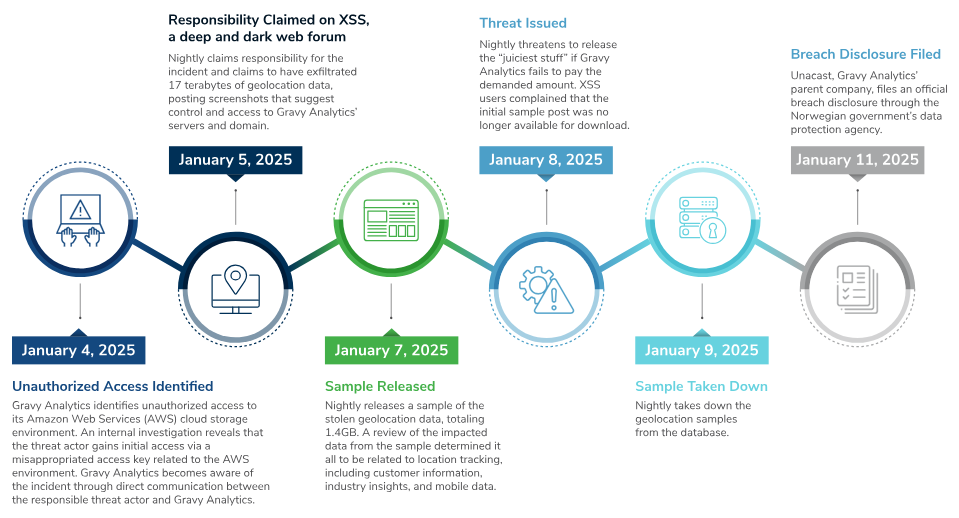
In this Risky Bulletin sponsor interview, Ed Currie from Kroll Cyber talks to Tom Uren about the recent hack of the Gravy Analytics geolocation data provider. He explains the hack and how geolocation data can be used by malicious actors.
Arrests, cybercrime, and threat intel
Scam gang arrests: The Cambodian national police arrested 186 foreign nationals who operated a cyber scam compound in the country's capital. The suspects were all Chinese and Taiwanese and operated out of a large villa in Phnom Penh. They targeted Chinese-speaking nationals in phone-based scams. [Additional coverage in the Cambodia-China Times]
Coinbase phishing campaign hits big: Hackers have stolen $46 million worth of crypto-assets from Coinbase users following a phishing campaign over the past two weeks. One Coinbase user alone lost 400 Bitcoin, worth around $35 million. According to blockchain investigator ZachXBT, Coinbase users have lost over 100$ million to phishing scams since December last year. [Additional coverage in CryptoSlate]
Slovenly Comet hacks SMS gateways: A hacking group named Slovenly Comet has hacked SMS gateways in Argentina to bypass MFA and hijack user accounts. The hack went unnoticed for several weeks before it was noticed by an organization investigating cryptocurrency security incidents. The attackers allegedly hijacked accounts on Telegram, Signal, crypto services, email accounts, and Latin American banks.
Terrorgram profile: ProPublica has published an extensive deep dive into the rise and fall of Terrorgram, an online Telegram community that encouraged members to carry out murders, physical attacks, and hate crimes.
Quishing explosion: Similar to other reports from Proofpoint and Sublime Security, Palo Alto Networks also reports seeing a huge rise in quishing—the practice of hiding phishing links in QR codes sent to users via email.
STAC4365: Sophos says that a threat actor (STAC4365) known to target MSP admins for years has now switched to the Qilin RaaS.
PAN GlobalProtect scanning: Security firm GreyNoise has identified a cluster of almost 24,000 IP addresses that have scanned the login pages of Palo Alto Networks GlobalProtect VPN gateways. The scans took place over the past month. GreyNoise warns the scan activity is likely a precursor to future exploitation attempts. Several GlobalProtect vulnerabilities have been disclosed over the past months.
Malware technical reports
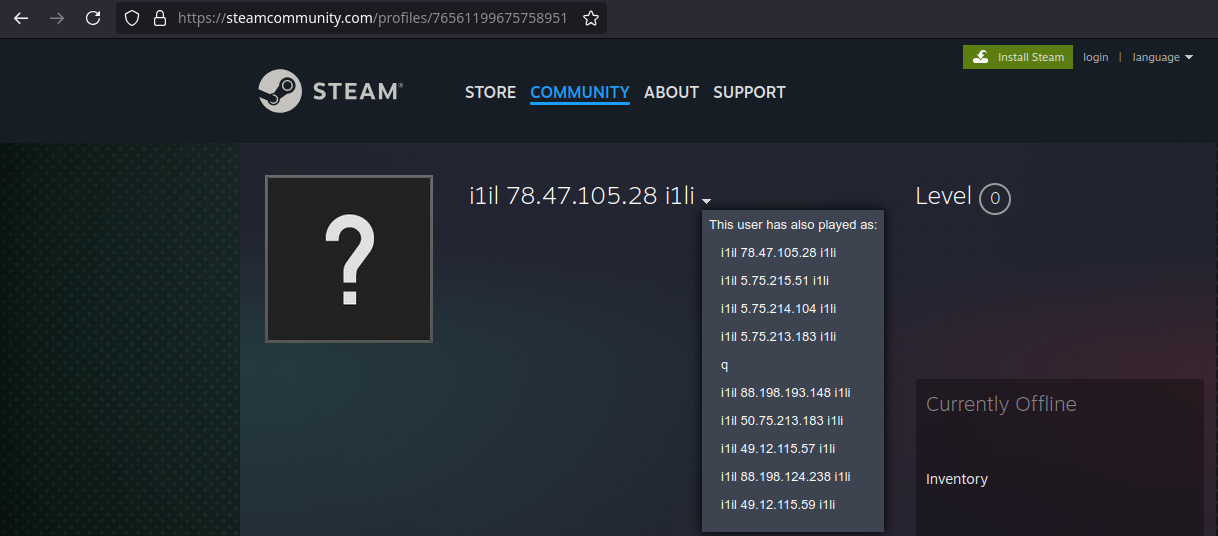
BlackSuit ransomware: The DFIR team has published one of their IR reports from a BlackSuit ransomware infection that originated from a fake Zoom app installer. The most interesting part of this report is how BlackSuit used a Steam profile page to store the IP address hosting various second-stage malware strains.
CPU_HU cryptominer: A hacking group named JINX-0126 has compromised over 1,500 PostgreSQL databases with a new crypto-malware strain named CPU_HU.
Auto-color backdoor: Security researcher Mohamed Ezat published a technical analysis of Auto-color, a new Linux backdoor deployed in the wild at the end of last year.
"It was first observed between November and December 2024 and is designed to avoid detection while remaining hidden in systems for a long time. The malware acts as be benign color-enhancement tool and uses common file names like 'door,' 'egg,' and 'log' to disguise itself."
New Triada versions: Kaspersky researchers have found a new version of the Triada malware preinstalled on Android devices sold in Russia. The new version gives the trojan extra features to intercept content on the device, such as calls, SMS, instant messaging apps, and network traffic. It can also intercept and replace phone numbers and cryptocurrency addresses to redirect users to scams or steal their funds. So far, the new version has been linked to the theft of over $270,000 of various crypto assets.
Salvador Stealer: ANY.RUN published a technical analysis of Salvador Stealer, a new infostealer targeting the Android space.
HijackLoader: Zscaler has published a technical report on HijackLoader (IDAT Loader, GhostPulse) and its recent changes, such as its new call stack spoofing module, anti-VM module, and support for scheduled task persistence.
Gootloader changes: The Gootloader malware has gone through another change of its code and infrastructure.
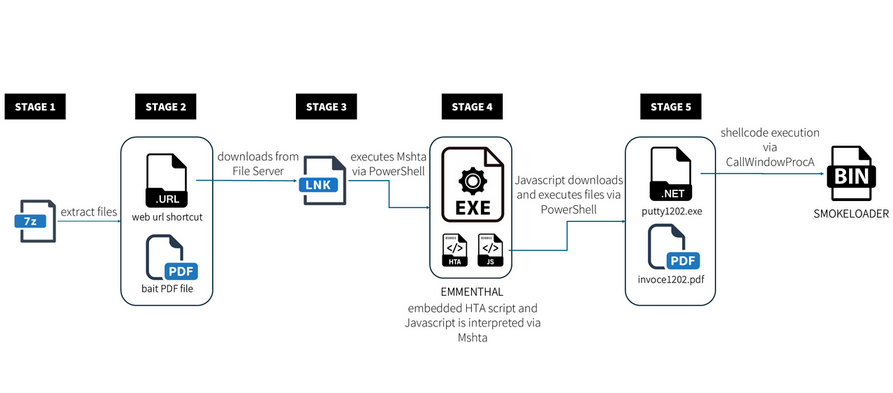
Emmenhtal: G Data looks at a campaign targeting Ukrainian banking users with the Emmenhtal loader.
Sponsor section
The Kroll team takes a look at the cyber risks emerging from leaks at data analytics and aggregators, using the recent leak of geolocation data from Gravy Analytics as a case study.
APTs, cyber-espionage, and info-ops
Earth Alux: Trend Micro has published a report on a super secretive Chinese APT named Earth Alux and its malware arsenal, including its main tool, the VARGEIT backdoor.
"The first sighting of its activity was in the second quarter of 2023; back then, it was predominantly observed in the APAC region. Around the middle of 2024, it was also spotted in Latin America. Earth Alux has also been observed to conduct regular tests for some of its toolsets to ensure stealth and longevity in the target environment."
APT37's Konni RAT: CyFirma has published a report on APT37's Konni remote access trojan, one of their favorite payloads.
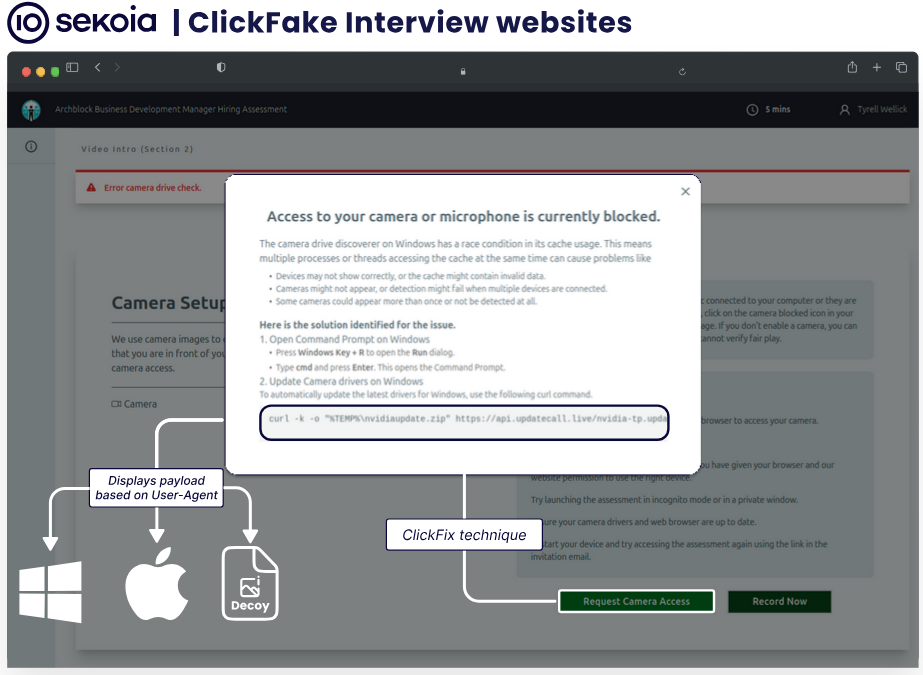
Lazarus adopts ClickFix: North Korean state hackers have adopted the ClickFix technique for recent operations. The technique uses fake error popups to trick users into running malicious commands in the Windows or macOS command-line interface. Sekoia says North Korean hackers are showing these popups on fake job interview websites where they lure targets. The malicious commands deploy a new macOS and Windows backdoor named GolangGhost. This campaign targeted individuals from the cryptocurrency ecosystem.
Vulnerabilities, security research, and bug bounty
Apple security updates: Apple has released security updates for basically every piece of software it has. No zero-days were mentioned.
ImageRunner GCP vulnerability: Tenable security researchers have discovered and helped patch a vulnerability in the Google Cloud platform. The vulnerability, named ImageRunner, abuses the relationships between the Cloud Run, Container Registry, and Artifact Registry services to pull private customer artifacts into an attacker's account.
Bootloader vulnerabilities: Microsoft has discovered 20 vulnerabilities in open-source bootloaders such as GRUB2, U-boot, and Barebox.
Brocade switch vulnerabilities: Security researcher Pierre Kim has found ten vulnerabilities in Brocade Fiber Channel switches. Some of the worst bugs are two pre-authentication RCEs and default and weak device credentials. Brocade patched only seven of the bugs, while three remain unpatched because they impact now-retired devices.
PAN vulnerabilities: The same Kim also published a write-up on three vulnerabilities in Palo Alto Network's firewalls.
Canon printer vulnerability: Microsoft has found a vulnerability that can allow malicious apps to run code via some Canon printer drivers.
Carbon Black Cloud vulnerabilities: ERNW has found three vulnerabilities in the VMware Carbon Black Cloud agents. All are now patched.
CrushFTP PoC and exploitation: Project Discovery has published a technical write-up and PoC for a recent CrushFTP authentication bypass tracked as CVE-2025-2825. Aaaaaand it's now exploited.
"CVE-2025-2825 demonstrates how parameter overloading in authentication systems can lead to critical vulnerabilities. This case shows that reusing a flag meant for password lookup as an authentication bypass control creates a severe security flaw."
Apache Camel exploitation: Threat actors have started scanning and attempting to exploit Apache Camel servers for a recently disclosed vulnerability tracked as CVE-2025-27636. They're very likely using a recently released PoC.
Infosec industry
New tool—GoResolver: Security firm Volexity has released GoResolver, a tool for symbol extraction from Go-based malware.
RWC 2025 videos: Live streams from the Real World Crypto 2025 security conference, which took place last week, are available on YouTube.
Threat/trend reports: CERT-EU, CertiK, Cisco Talos, DTEX, and ImmuneFi have recently published reports and summaries covering various infosec trends and industry threats.

Risky Business Podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq look at all the strands of evidence that make people think the NSA is a top-tier cyber actor.
Tom Uren and Patrick Gray discuss how the Signalgate messages betray an alarming lack of security nous at the highest levels of the US natsec leadership. It's head-scratchingly bad.
