Risky Bulletin Newsletter
March 20, 2026
Risky Bulletin: AWS kills bucketsquatting
Written by

News Editor
This newsletter is brought to you by Sublime Security. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
Amazon Web Services has rolled out a new security feature last week that will help customers prevent a type of attack known as S3 Bucket Namesquatting, or Bucketsquatting.
The attack was first described by cloud engineer Ian Mckay in 2019. It happens when an attacker abuses the predictable naming conventions in AWS bucket names to register buckets that have expired or have been deleted by their original owners.
If traffic still flows to the old buckets, this allows attackers to collect data from internal networks or public-facing apps, leading to serious security incidents.
The new feature introduced last week allows AWS admins to tie AWS bucket names to account IDs and a regional namespace, such as:
"This doesn't retroactively protect any existing buckets (or published templates that use a region prefix/suffix pattern without the namespace), but it does provide a strong protection for new buckets going forward," Mckay said. "If you wish to protect your existing buckets, you’ll need to create new buckets with the namespace pattern and migrate your data to those buckets."
Mckay points out that AWS had been supporting bucket namespaces for a while, but this is a much stronger protection.
Both Azure and Google Cloud have protections against bucketsquatting, but they are using different methods.
While bucketsquatting had been known for a while, the issue got fresh attention last February when researchers at WatchTowr Labs registered around 150 AWS S3 buckets that were previously owned by now-abandoned commercial and open-source projects.
At the time, the buckets were still receiving traffic, including from government and military domains and Fortune 500 companies. Some of the traffic suggested some buckets were previously used to deliver software updates or server configurations, which put the researchers in a position to hijack remote networks.
It's 20th anniversary since #AWS S3 was released and we have a regional namespaces preventing name squatting of buckets, which should prevent reusing names 🎉 aws.amazon.com/blogs/aws/in...
— Marko Bevc (@marko.social) 2026-03-13T19:01:13.148Z
Hey look AWS finally discovered addressing
— Evelyn (@kandake.africa) 2026-03-13T07:28:19.464Z
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Cyberattack cripples breathalyzer car locks: A cyberattack has crippled the IT network of car breathalyzer test company Intoxalock. Breathalyzer devices installed in cars across the US have been unable to connect back to Intoxalock servers and confirm successful tests. Drivers under court orders for DUI convictions have been unable to start their cars for at least two days. [DysruptionHub]
Fake security firm linked to crypto-heists: Hackers using the cover of a fake cybersecurity firm have stolen millions worth of cryptocurrency. The hackers used supply-chain intrusions to compromise Electron apps and browser plugins. They collected private keys and seed phrases and emptied out crypto-wallets. The attacks came to light after a disgruntled employee of Chinese security firm Wuhan Anshun exposed the company's secret operations. One of the victims is Trust Wallet, whose users lost $7 million last December. [Crypto.news]
Venus Protocol crypto-heist: Hackers have stolen $3.6 million worth of crypto-assets from Venus Protocol. The attackers allegedly exploited the platform's flash loan system to extract the funds. This is the platform's second hack after losing another $27 million last September. [MEXC]
Bitrefill blames North Korea for hack: Suspected North Korean hackers have breached Bitrefill, an online platform that allows users to buy gift cards and refill SIMs using cryptocurrency. The entry point was traced back to a compromised employee laptop. Bitrefill says hackers stole crypto assets from its wallets, customer records, and attempted to alter gift card inventory. The company says the attack resembled past Lazarus and Bluenoroff intrusions.
Meta AI agent does dumb stuff: A Meta AI agent gave an engineer bad advice that ended up exposing troves of user data to other engineers who did not have permission to access it. [The Information]
Outpost24 exec spear-phishing: SpecOps detected a spear-phishing campaign targeting one of the execs of its parent company Outpost24. The phishing page posed as a Cisco domain.
Stryker begins restoring: Medtech company Stryker has begun restoring IT systems that were hit by Iranian hackers earlier this month. [MedTech Dive]
Iranian defacements: Iranian hacktivists have defaced the website of Orthodox news site Yeshiva World News.[The Jerusalem Post]
BlueLeaks 2.0: A hacker has compromised and leaked data from a law enforcement platform for storing confidential tips. A hacker going by the Internet Yiff Machine says they exploited a vulnerability to breach P3 Global Intel, a platform managed by Navigate360. The hacker has now shared more than 93GB with journalists and the DDoSecrets project. The leak suggests Navigate360 failed to encrypt data and stored enough details to deanonymize those who submitted tips. [Straight Arrow News // DDoSecrets] [h/t Mikael Thalen]
The data, which @ddosecrets.org has dubbed BlueLeaks 2.0, was obtained by a hacker group calling itself 'THE INTERNET YIFF MACHINE." The data comes from P3 Global Intel, a company which provides crime tip management tools to thousands of clients. san.com/cc/millions-...
— Mikael Thalen (@mikaelthalen.bsky.social) 2026-03-18T15:50:02.489Z
General tech and privacy
Turing Award 2026: Charles H. Bennett and Gilles Brassard have been awarded this year's Turing Award for their foundational work on quantum computing.
Built-in VPN coming to Firefox: Firefox 149, scheduled to be released next week, will ship with a free built-in VPN. The service will be available in the US, the UK, France, and Germany, and users will be limited to 50 GB of data.
Pixel tracking research: JScrambler has published a report looking at how Meta and TikTok are using their pixel tracking scripts to collect everything on their users, including details from payment pages, such as the last four digits of a user's card. Creepy, I know.
Meta shuts down its stupid VR bullshit: After spending years funneling billions into its Metaverse VR platform, Meta is now shutting it down after it realized nobody cared. [CNBC]
Government, politics, and policy
Belgium launches its own secure app: The Belgian government has launched its own secure messaging app named Beam. The app was designed for internal government and military use. It is meant to replace foreign apps like WhatsApp and Facebook Messenger for official government communications. Military and intelligence officials gained access to the app last week while government workers will receive it next week. [DeMorgen]
Russian internet censorship is choking local companies: The Russian private sector is desperately asking the government to lift bans on Telegram, WhatsApp, and other foreign messengers, so they can continue contacting and working with foreign partners. [Vedomosti]
Japan active cyber defense: Japan will begin to carry out offensive cyber operations in October this year. Its Parliament passed a law last year that allows its police and military defense forces to preemptively hack adversary networks. The ruling Cabinet approved the law after evaluating its conformity with the country's constitutional principles of non-aggression. [Nippon]
Congress seeks private comms of EU officials: The US House Judiciary Committee has subpoenaed ten US tech companies and asked to provide copies of their communications with EU officials. The subpoenas cover communications related to the EU's DSA enforcement. They also cover messages set to auto-delete. The GOP-led commission has accused the EU of trying to censor Americans through its tech rules. Subpoenaed companies include Alphabet, Amazon, Apple, Meta, Microsoft, OpenAI, Reddit, Rumble, TikTok and X. [Politico Europe]
ODNI releases annual threat assessment: The US Office of the Director of National Intelligence has published its Annual Threat Assessment for 2026. On the cyber side, the report mentions the big four (China, Iran, North Korea, and Russia) but also includes ransomware groups as a threat to national security. It's a pretty shallow look.
Patel admits buying US citizens' data: FBI Director Kash Patel admitted in a Senate hearing this week that his agency is buying Americans' sensitive data off the private market. The data is allegedly being used to track people's movement and location history. US laws prevent law enforcement agencies from getting the data without a warrant from tech platforms, but not buying from data brokers. [Politico]
National US AI law: Senator Marsha Blackburn (R-Tenn) has published a first draft of a bill (TRUMP AMERICA AI Act) designed to become the US national AI legislation and overwrite all state regulation efforts.
Cairncross clarifies private hack-backs: National Cyber Director Sean Cairncross said this week that the US government won't let private companies hack-back threat actor infrastructure, but more like collaborate and share data, but still retain control. [CyberScoop]
Azure got FedRAMP approval despite issues: A ProPublica investigation found that Microsoft's Azure cloud platform got approved for government use even if it failed to adequately explain to government officials how it stores sensitive data.
This is a long article, but very much worth your time. It also tells the story of how FedRAMP has turned into a rubber stamp for well funded software vendors. And yet it still serves as a barrier to entry for new contenders. Meanwhile, the USG suffers massive tech debt, despite massive spending.
— Jason Kikta (@kikta.net) 2026-03-19T03:57:42.865Z
Sponsor section
In this Risky Business sponsor interview, Catalin Cimpanu talks with Alex Orleans, Head of Threat Intelligence at Sublime Security, about the increase in email attacks leveraging Zoom invites and other video conferencing tools.
Arrests, cybercrime, and threat intel
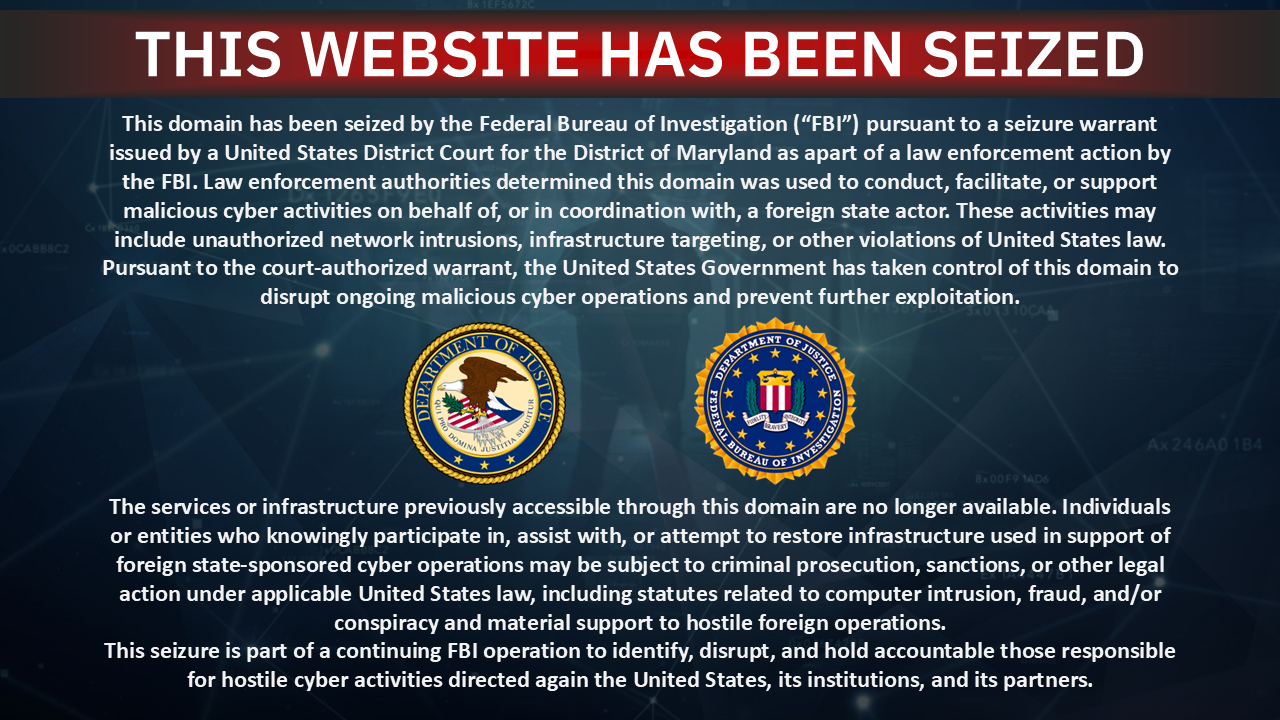
FBI seizes Handala websites: US authorities have seized two websites operated by Iranian hacking group Handala. The group had previously used the websites to leak data and offer bounties on Israeli and US officials. Earlier this month, the group breached US medtech giant Stryker and wiped over 200,000 systems in retaliation for the US attacks on Iran. [TechCrunch]
ShieldGuard takedown: Okta's security team has disrupted a Chrome extension that posed as a security tool but stole crypto-wallet data. The ShieldGuard extension harvested full HTML code from pages after users signed in. It targeted popular cryptocurrency platforms and Google services. It was able to execute malicious code and bypass Chrome security defenses by downloading and running the code in its own custom JavaScript interpreter.
Malicious Windsurf IDE extension: Bitdefender researchers have found a malicious extension for the Windsurf IDE that contained an infostealer.
"The extension, disguised as an R language support extension for Visual Studio Code, retrieves encrypted JavaScript from blockchain transactions, executes it using NodeJS runtime primitives, drops compiled add-ons to extract Chromium data, all the while establishing persistence with the help of a hidden PowerShell scheduled task."
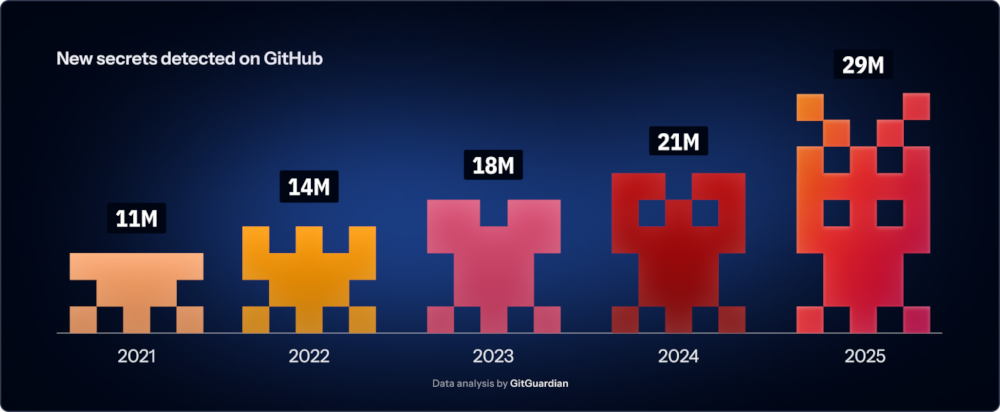
More secrets leaked than ever: Almost 29 million hardcoded secrets have leaked on GitHub last year—more than any other year. According to GitGuardian, the adoption of AI tools played a crucial role in the spike in secrets that leaked last year. AI-assisted code commits leaked almost twice as many secrets as the normal baseline.
More malware on GitHub: The Acronis security team has found hundreds of malicious GitHub repos containing malware-laced files disguised as game cheats. Most contained an infostealer, such as Vidar. Acronis also linked some Reddit posts promoting cheats to the same campaign.
OpenClaw phishing campaign: Threat actors are spamming GitHub issues and tagging other developers with fake promises of OpenClaw tokens. The plan is to lure the devs to phishing sites where they're asked to connect their crypto-wallets, but are getting their accounts emptied.
Intune hardening guide: CISA told US orgs to implement Microsoft's recent Intune-hardening guide to prevent a repeat of the Stryker attacks. The agency said it was aware of malicious activity similar to the one that took place at Stryker but did not provide other details.
Ransomware exfiltration tactics: Cisco Talos has published a useful report on all the exfiltration methods used by ransomware groups in the past to siphon data from compromised networks.
Interlock ransomware had a Cisco zero-day: The Interlock ransomware group exploited a Cisco zero-day for almost a month before patches were available. Attacks began on January 26 before a patch was released on March 4. The vulnerability can allow threat actors to run malicious code on Cisco firewalls running the FMC software. Exploitation occurs via attacker-supplied Java byte streams, don't require authentication, and run the malicious code as root.
A fifth of suspended Telegram channels are cybercrime-related: One in five Telegram channels suspended last year hosted cybercrime activities. This included the trading of card data, stolen information, or hacking services. Check Point says Telegram moderation reached record levels last year but malicious activity persisted, with suspended communities persisted quickly reforming in new groups and channels.
Surveillance intermediaries: The Atlantic Council looks at "intermediaries" in the modern surveillance and spyware market, individuals and companies facilitating the sale of products across jurisdictions and supporting product development and deployment. This includes exploit brokers, resellers, partner companies, and such. The Council argues crackdowns should also target these intermediaries, and now only the main sellers.
LiveChat abuse: Cofense has spotted phishing campaigns that integrated live chat clients from the LiveChat service to help guide targets through the phishing process.
Tax season phishing is here: Microsoft's security team has published a report on the most common tax season-related phishing schemes active this year.
Keitaro TDS: Infoblox has published a profile on Keitaro Tracker, or Keitaro TDS, a cybercrime group running a network of servers and hacked sites designed to hijack legitimate traffic and redirect it to other cybercrime groups renting its infrastructure. Right now, the service is very popular with AI-driven investment scams, but is also used for fake browser updates and affiliate advertising platforms or fed decoy pages.
Malware technical reports
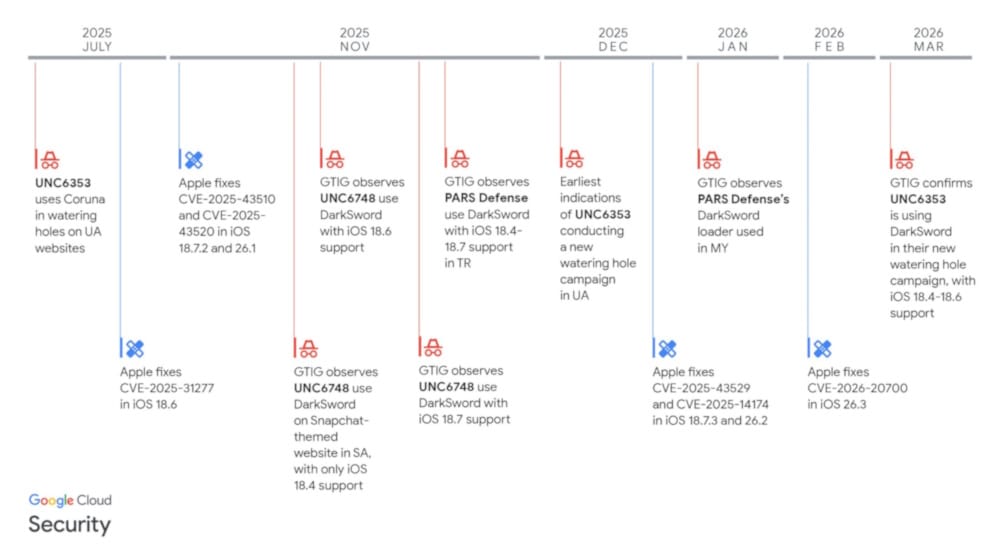
DarkSword iOS exploit kit: A second professional iOS hacking framework has been discovered used in the wild. The DarkSword toolkit was used in attacks against targets in Ukraine, Turkey, Malaysia, and Saudi Arabia. The kit was used in both espionage and financially-motivated operations. According to Google, iVerify, and Lookout, DarkSword used at least six iOS exploits. All are patched.
VoidStealer: Gen Digital has spotted the VoidStealer infostealer using a new method to bypass Chrome's credentials encryption system to steal passwords and cookies.
"The technique relies on attaching to the browser process as a debugger and setting breakpoints at carefully selected locations to extract the v20_master_key directly from the browser process memory."
PureLog Stealer: Trend Micro is seeing a malspam campaign using fake copyright infringement lures to trick victims into infecting themselves with the PureLogs infostealer.
Speagle infostealer: Symantec and Carbon Black have spotted the Speagle infostealer storing stolen data inside hacked Cobra DocGuard servers, a legitimate document security and encryption platform developed in China.
Horabot: Kaspersky has spotted new Horabot campaigns hitting Brazil.
SnappyClient: Zscaler has found a new command-and-control (C2) framework that it tracks as SnappyClient. It is currently used in the wild in HijackLoader campaigns.
Iranian botnet: Hunt Intelligence have discovered a small Iranian SSh-based botnet that appears to have been used for DDoS attacks and censorship evasion.
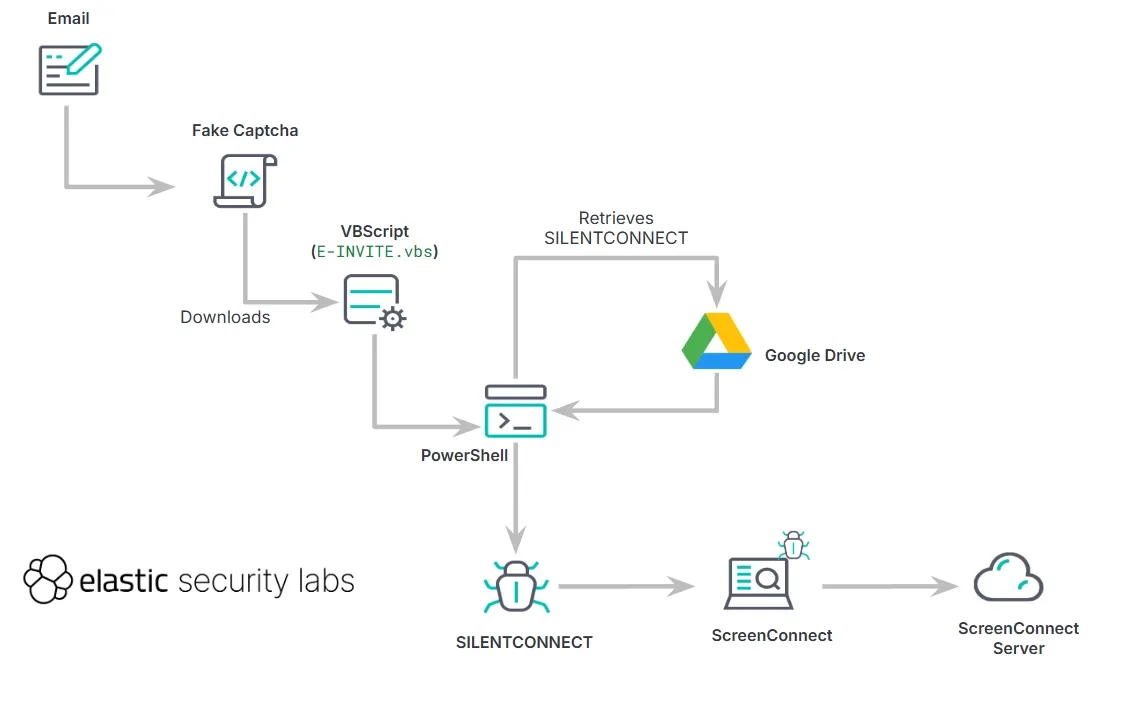
SILENTCONNECT loader: Elastic's security team looks at SILENTCONNECT, a loader used in intrusions to deploy ScreenConnect RMMs that threat actors use to remotely access compromised systems.
The Gentlemen: Group-IB has published a profile on The Gentlemen ransomware operation and tactics used by its affiliates.
Beast ransomware: Team Cymru has spotted new attacks from the Beast ransomware group after the groups went silent in November.
Perseus Android banking trojan: ThreatFabric has published a technical report on Perseus, a new Android banking trojan derived from previous trojans like Cerberus and Phoenix. This one stands out because of a feature that searches the phone for user notes in the hope of finding passwords or seed phrases.
AI in malware: Palo Alto Networks has taken another look at how threat actors are using AI for their malware operations. The conclusion is that many groups are still at the experimentation phase, with samples showing "superficial and ultimately ineffective use of LLMs as AI theater."
EDR killers: ESET analyzed more than 80 EDR killers to understand how this new class of tools work and are being used in intrusions and malware deployments. Here are the main conclusions:
- Affiliates, not operators, pick the EDR killers; larger affiliate pools lead to greater tooling diversity.
- The same driver appears in unrelated tools, and the same tool can migrate between drivers. Consequently, driver-based attribution to groups is often misleading.
- Packer as a service and “EDR killer as a product” increase availability, muddy attribution, and add defense complexity.
- EDR killers implement defense evasion techniques, while encryptors focus purely on encryption.
- We strongly suspect that AI assisted with the development of some EDR killers, and we provide a concrete example with the Warlock gang.
- While BYOVD dominates, custom scripts, anti-rootkits, and driverless EDR killers are utilized as well.
We emphasize that in RaaS gangs, it is the affiliates, not the operators, who select and deploy the EDR killers, complicating defense strategies, but also revealing otherwise hidden affiliations. 3/6
— ESET Research (@esetresearch.bsky.social) 2026-03-19T10:02:18.569Z
Sponsor section
In this sponsored product demo, Sublime Security co-founder and CEO Josh Kamdjou joins Risky Business podcast host Patrick Gray to show off the company's email security platform, including its latest agentic AI bells and whistles.
APTs, cyber-espionage, and info-ops
Operation GhostMail: A Russian cyber-espionage group is exploiting a Zimbra vulnerability to hack Ukrainian government systems. The attacks are exploiting a Zimbra cross-site scripting bug (CVE-2025-66376) patched in November. Security firm Seqrite, which discovered the attacks, believes Russian group APT28 is behind the attacks.
WaterPlum's StoatWaffle: NTT's security team has published a report on StoatWaffle, a new malware family used by North Korean hacking group WaterPlum.
RagaSerpent: PT ITSEC has published a report on RagaSerpent, a subgroup of suspected Indian APT group SideWinder (Rattlesnake).
Vulnerabilities, security research, and bug bounty
Apple pushes a background security update: Apple rolled out its first-ever background security update for iOS this week. The update fixes a low-severity Safari bug. The fix was delivered through an Apple update system named Background Security Improvements. It allows Apple to apply security patches to individual components without restarting the entire OS. The system was first used in 2019 to push a silent fix for macOS.
Unpatched Telnet RCE: A major vulnerability is still unpatched in the GNU InetUtils telnet daemon (telnetd). Tracked as CVE-2026-32746, the bug allows remote unauthenticated attackers to overflow memory on a Telnet server and possibly run malicious code. This is the second major bug disclosed in the GNU InetUtils telnet daemon this year after an authentication bypass in January. The package is a standard install on many Linux systems.
Unpatched IP KVM bugs: Vulnerabilities in four low-cost IP KVMs can allow attackers to take over the devices and any connected systems. According to Eclypsium, only five of the nine reported bugs have released patches. KVMs from Angeet/Yeeso, GL-iNet, JetKVM, and Sipeed are vulnerable.
New MSFT SharePoint exploitation: Threat actors are exploiting an RCE vulnerability to take over Microsoft SharePoint servers. The bug was initially patched in January but was confirmed as under-attack by CISA this week. Attacks were also spotted against a Zimbra bug (see Operation GhostMail).
PolyShell vulnerability: Adobe patched a major bug in the pre-release version of Magento and Adobe Commerce that can allow attackers to upload executable files to any store. According to Sansec, the patch has not been backported to older versions that are still vulnerable. No exploitation has been spotted so far.
BMC FootPrints RCE: WatchTowr researchers have found four vulnerabilities that can be used to bypass authentication and run malicious code on BMC FootPrints IT help desk servers. I'd expect these to enter exploitation soon.
Ubiquiti patches 10/10 bug: Ubiquiti has released a security update to patch a critical vulnerability in its UniFi internet gateway and WiFi management application. The firmware update fixes a path traversal bug that can allow threat actors to access configuration files and take over UniFi gateways. The vulnerability has a severity rating of 10/10.
Jenkins security updates: The Jenkins project has published three security updates for the project's core files and one of its plugins.
ConnectWise security update: MSP software provider ConnectWise has released a security update to fix an exposed ScreenConnect machine key that was abused to pass boobytrapped installers as valid.
Snap EoP: Ubuntu has fixed a bug in the Snap package installer that could have been abused for elevation of privilege root attacks. [Qualys]
Infosec industry
Threat/trend reports: Claroty, Crogl, GitGuardian, LevelBlue, and Red Canary have recently published reports and summaries covering various threats and infosec industry trends.
New tool—NemoClaw: NVIDIA has released NemoClaw, an NVIDIA OpenShell plugin for safely installing and running OpenClaw AI assistants.
Russia's cyber push in SE Asia: The East Asia Forum warns that Russian cybersecurity companies are expanding their presence in Southeast Asia through exports, training programs, and partnerships with local governments.
RIP Sergey Mineev: Kaspersky Lab security researcher Sergey Mineev has passed away.

Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about how successfully achieving America's war goals could force Iran to double down on cyber power. It's resilient to bombing and is the cheapest, quickest way for the regime to get some wins post-war.
We recently also launched a new podcast series called Risky Business Features. In this episode James Wilson takes a (ridiculously) deep dive into the Coruna exploit kit.
