Risky Bulletin Newsletter
March 13, 2026
Risky Bulletin: Another residential proxy provider falls as authorities continue crackdowns
Written by

News Editor
This newsletter is brought to you by Thinkst, the makers of the much-loved Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
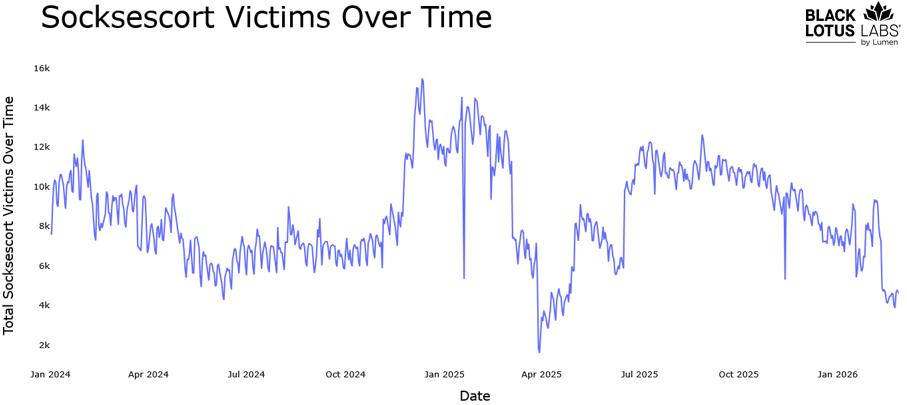
American and European law enforcement agencies have seized the infrastructure of a residential proxy provider named SocksEscort; the latest of such a crackdown against proxy providers over the past years.
The service had been running since 2021 and rented access to more than 369,000 different IP addresses across its lifetime.
According to the FBI, Europol, and Dutch Police, SocksEscort was a front for a malware operation that infected modems and home routers. Lumen's Black Lotus Labs linked it to a botnet it discovered in 2023, named AVRecon.
The botnet never grew to an extremely large size, but managed to maintain a healthy pool of IP addresses it could rent out to its customers, most of which were other cybercrime operations needing ways to hide their attacks inside the infrastructure of residential internet providers.
Europol linked the service to ransomware deployments, DDoS attacks, and the distribution of child sexual abuse material (CSAM).
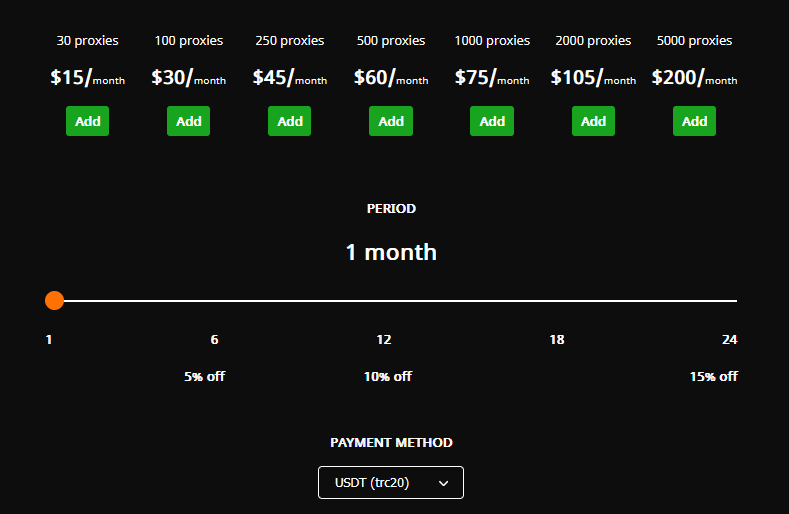
It also estimated that SocksEscort operators made more than €5 million from renting out their infected IPs, which is quite the sum for such a service. Prices on its site [archived] ranged from $15/month for 30 proxies to $200/month for 500.
On the day of the takedown, the FBI has also published an advisory with tips on how telcos and consumers can protect their devices and prevent them from ending up nodes in proxy networks. It also published an advisory [PDF] on how to spot and get AVRecon off your devices.
Over the past few years, the US has mounted a war against residential proxy networks after several reports concluded that foreign adversaries were using infected American routers to hide their tracks.
Law enforcement takedowns have targeted both private proxy networks—called ORBs, or Operational Relay Box networks—but also residential proxy providers. The difference between the two is that ORBs are typically built and managed by the threat actors for their sole use, while a residential proxy provider is a service built for an operator's financial gain, typically rented out to whoever has the money.
Past botnets that were taken down include the likes of 911 S5, Anyproxy, 5socks, RSOCKS, Flax Typhoon's Raptor Train, Volt Typhoon's KV Botnet, APT28's Moobot and VPNFilter, and many more.

Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
We also launched a new podcast series called Risky Business Features. In this episode James Wilson takes a (ridiculously) deep dive into the Coruna exploit kit.
Breaches, hacks, and security incidents
DOGE dude stole SSA data: A former DOGE employee is being investigated for allegedly stealing two internal databases from the US Social Security Administration. The former DOGE software engineer now works for a private company. He allegedly bragged about taking the data out of the SSA on a thumb drive. The databases contain extremely sensitive data on more than 500 million living and dead Americans. [WaPo]
Hacker stole Epstein files from FBI: A hacker breached the FBI in 2023 and stole documents related to the Epstein sex trafficking investigation. The breach impacted a server at the Child Exploitation Forensic Lab in New York. The hacker didn't realize he breached the FBI and later contacted the Bureau to report child abuse images he found on the very same server. According to Reuters, FBI agents had a video chat with the intruder to convince them it was their server.
The hacker expressed disgust at the presence of child abuse images on the device and left a message threatening to turn its owner over to the FBI… FBI officials… convinced… the hacker that they actually were the FBI, by having the hacker join a video chat where they flashed their credentials
— Matthew Shirts (@matthewshirts.bsky.social) 2026-03-11T16:35:46.883Z
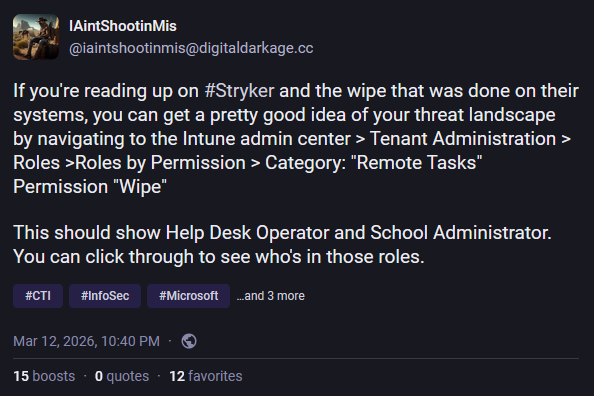
Stryker data wiping incident: Iranian hackers have wiped the IT systems of American medical device maker Stryker. The company has shut down all production systems globally. Hacktivist group Handala took credit for the hack and claimed it was in retaliation for the US bombing of an all-girls school in Iran. Reports claim the group hacked the company's Microsoft Intune server and issued a remote wipe command. The group claims to have wiped more than 200,000 phones, servers, and workstations. [KrebsOnSecurity // Zero Day // SEC 8K filing]
Cyberattack on Poland's nuclear center: Poland says it blocked a cyberattack on one of its nuclear facilities that appears to have been carried out by Iranian-linked hackers. [Politico Europe]
Israel Railways signage hacked: Suspected Iranian hackers have defaced the signage of Israel's national railway company. Israel Railways shut down the panels after they started showing fake missile alerts and other threats. [Ynet]
Iranian hackers hit Albania's Parliament: The Albanian government is investigating a breach of its internal email server. The hack took place on Tuesday. Lawmakers couldn't access their PCs and email accounts for hours as IT staff investigated. Iranian hacking group Homeland Justice took credit for the attack. The group has a long history of hacking Albanian government agencies in response to the country hosting exiled Iranian opposition leaders. [The Record]
Quittr leak: Data has leaked from Quittr, an app to help men escape porn and masturbation addictions. [404 Media]
Loblaw data breach: Canadian retailer Loblaw has suffered a security breach. The company notified customers of the incident this week. It also logged out all users and asked them to sign back into their accounts. Loblaw said the incident didn't impact its financial services branch. [CTV News]
Telus breach: Canadian business processing and outsourcing company Telus Digital has confirmed a security breach related to a ShinyHunters intrusion last year. [BleepingComputer]
County sues to get BEC funds back: The Laurens county in South Carolina has sued to recover $1.5 million stolen in a BEC incident at the end of last year. [The Post and Courier]
South Korea fines Lotte Card over breach: South Korea's privacy watchdog has fined fintech company Lotte Card 9.6 billion won ($6.5 million) for leaking the personal data of 450,000 users last September. According to the agency, the company failed to encrypt data and stored customer details in plaintext. [h/t J.P.]
Michelin impacted by EBS hacking spree: Tire maker Michelin has confirmed that it was one of the 100+ companies that had its data stolen as part of a hacking spree that targeted Oracle E-Business Suite servers last year. [SecurityWeek]
General tech and privacy
Odido stops AI telemetry: Dutch ISP Odido has removed a feature that sent router telemetry data to American AI company Lifemote. The secret behavior was discovered by Dutch security researcher Sipke Mellema last week. The secret behavior was removed after Dutch lawmakers started asking questions about the legality of the practice. Odido had not disclosed the telemetry collection to its customers. The Dutch telco is in everyone's crosshairs after it disclosed a major security breach last month. [NLTimes] [h/t RVD]
New Node.js release schedule: The Node.js project is slowing down its release schedule from two major releases per year to just one. This is a result of the project maturing over the past decade.
Atlassian layoffs: Australian software company Atlassian has fired 1,600 employees, or 10% of its staff, to make room for more AI products its CEO says can't replace people. YOLO leadership! [Heise Online]
Automattic launches local WordPress: Automattic has launched a new service that lets users run WordPress instances in their local browser only, without putting the site online. The WordPress team hopes users will use their sites for personal apps, such as CRMs or RSS readers.
Chrome 146: Google has released version 146 of its Chrome browser. See here for security patches and webdev-related changes. The biggest change in this release is the formal launch of the new Sanitizer API, a new system for working with HTML without exposing users to XSS attacks. This is also in Firefox since v148, last month. Chrome is also testing WebNN, a new API that "lets web applications and frameworks take advantage of native operating system services for machine learning and the underlying hardware capabilities available on your computer to implement consistent, efficient, and reliable ML experiences on the web."
YouTube expands likeness detection tool: Google has expanded YouTube's celebrity protection and likeness detection tool to current government officials, political candidates, and even some journalists.
Meta acquires MoltBook: Meta has acquired MoltBook, the silly project that acted as a social network where AI agents could plot world domination and the end of humankind. [Axios]
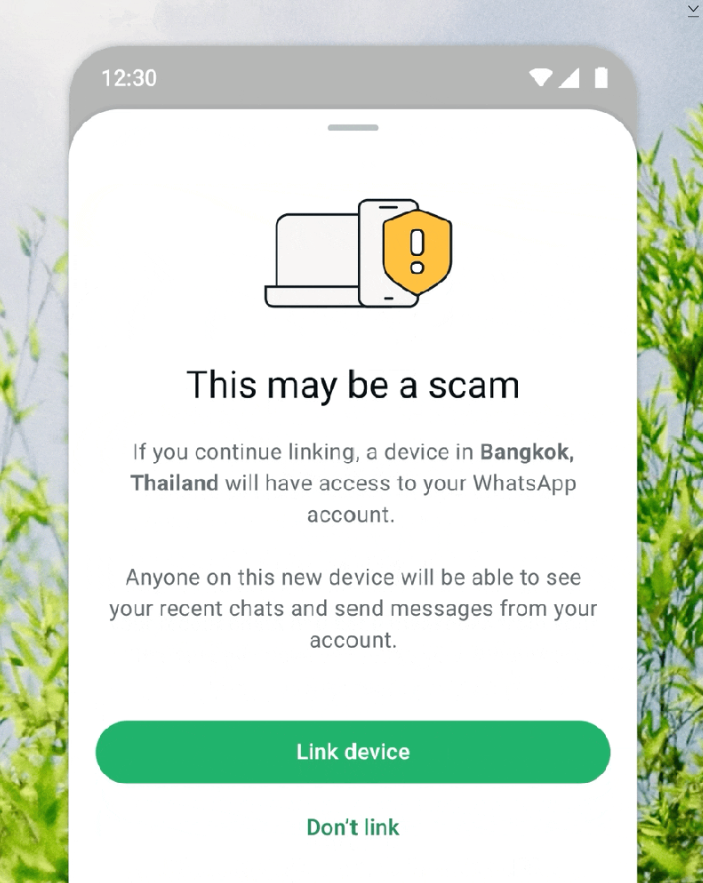
WhatsApp gets device linking alert: WhatsApp will warn users when they receive suspicious requests to link their account to a new device. The new security feature is part of a crackdown on scammers targeting its platform. Meta is also adding alerts for suspicious friend requests on Facebook and expanding its advanced scam detection feature on Messenger to more countries. The company said it removed almost 160 million scam ads last year.
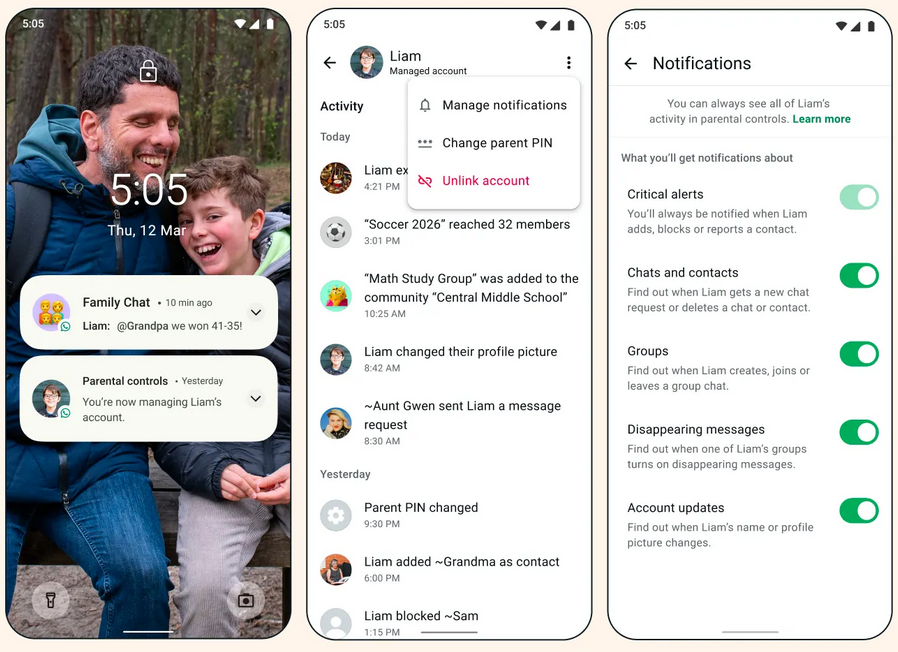
WhatsApp adds parent-managed accounts: Meta is also adding parent-managed accounts on WhatsApp. The accounts are designed for pre-teen children and access to their settings will be blocked by a PIN set up by the parent. Messages on the pre-teen accounts will remain private but parents will be able to approve who the child speaks to, what groups they can join, and review message requests from unknown contacts.
Government, politics, and policy
China warns against OpenClaw use: China has warned against the use of the OpenClaw AI agent on government and private networks. The country's CERT says the agent is easy to misconfigure during installation and expose companies to severe security risks. It is the second Chinese cybersecurity agency to warn against OpenClaw after the National Vulnerability DataBase (NVDB). [SCMP]
A small cottage industry offering OpenClaw installation services and preconfigured hardware emerges in China as the tool becomes the country's latest tech craze (Caiwei Chen/MIT Technology Review) Main Link | Techmeme Permalink
— Techmeme (@techmeme.com) 2026-03-12T06:36:09Z
Iran threatens US tech giants: Iran's military has threatened to launch missile and drone strikes against the Middle East offices of US tech platforms. Google, Microsoft, Palantir, IBM, Nvidia and Oracle were listed in a Telegram message this week by an IRGC-affiliated group. Iranian officials threatened to attack US companies after recent US-Israeli strikes have hit Iranian banks and other private companies. [Al Jazeera]
France publishes cyber threat report: France's cybersecurity agency has published its annual cyber threat report. Currently, only in French, but an English version usually also comes out after a few days. One of the main findings is that while ransomware attacks are down, data theft incidents are way up now. ANSSI also found growing interest for AI tools from threat actors. [ZDNet France]
New CNMF lead: Brig. Gen. Matthew Lennox will become the leader of US Cyber Command's Cyber National Mission Force this Friday. [The Record]
EU extends voluntary DM scanning: The European Parliament failed to secure enough votes to pass Chat Control so it extended a provision that grants tech platforms an exemption from EU data privacy rules if they run voluntary scans of users' DMs for CSAM and other illegal material. [Heise Online]
UPDATE: The European Parliament voted today to *end* untargeted mass scanning of private communications, firmly rejecting the error-prone and unconstitutional surveillance practices of recent years! Next: trilogue negotiations w/ Commission and Council.
— Fight Chat Control (@fightchatcontrol.bsky.social) 2026-03-12T00:09:05.766Z
Sponsor section
In this Risky Business sponsor interview, Marco Slaviero, CTO of Thinkst, talks to Tom Uren about how the company ensures that it is a learning organization.
Arrests, cybercrime, and threat intel
Meta's scam account crackdown: Thai authorities have arrested 21 individuals in Bangkok for running cyber scam compounds. Meta participated in the investigation and took down more than 150,000 scam accounts operated by the group. In all, Meta removed almost 11 million accounts linked to cyber scam compounds last year.
Nigerian hackers detained in India: Indian authorities have arrested two Nigerian nationals believed to be members of the Solar Spider hacking group. Police said the two were planning to exploit vulnerabilities in Indian cooperative banks and transfer funds to mule accounts. The two had already stolen more than $750,000 from a bank in Gujarat before they were caught last week. [The 420 // Amarujala]
US indicts another DigitalMint employee: US authorities have charged the former employee of a US security firm with conducting at least 10 ransomware attacks. Angelo Martino allegedly asked in excess of $75 million in ransoms from his victims. At the time of the attacks, he was working as a ransomware negotiator for security firm DigitalMint. He was part of a trio of cybersecurity professionals who hacked their customers, deployed ransomware, and then asked for ransoms. Two others were charged in November and later pleaded guilty. [CyberScoop]
Dutch police warn hosting companies: Dutch Police have warned local web hosting providers about hostile resellers that may drag their infrastructure into bulletproof cybercrime hosting services.
Joint Iran security advisory: Ten Information Sharing and Analysis Centers (ISACs) have published a joint advisory on Iranian threat actors and the dangers companies might face. [Gate15] [h/t Andy Jabbour]
CISA asks for Cisco device logs: CISA has ordered federal agencies to upload logs from Cisco SD-WAN devices to its cloud platform by March 23. The devices have been under attack using a zero-day since 2023. Aggregating the logs on CISA's platform will allow the agencies to investigate which agency was compromised. Agencies will also have to configure their Cisco SD-WAN to send future logs to the same Cloud Logging Aggregation Warehouse, also known as CISA CLAW.
Malicious themes on Packagist: Six themes for OPhim, a Vietnamese language Laravel CMS, contain malicious payloads. The six are available through the official Packagist portal. The payloads are JS redirectors that hijack traffic from compromised sites.
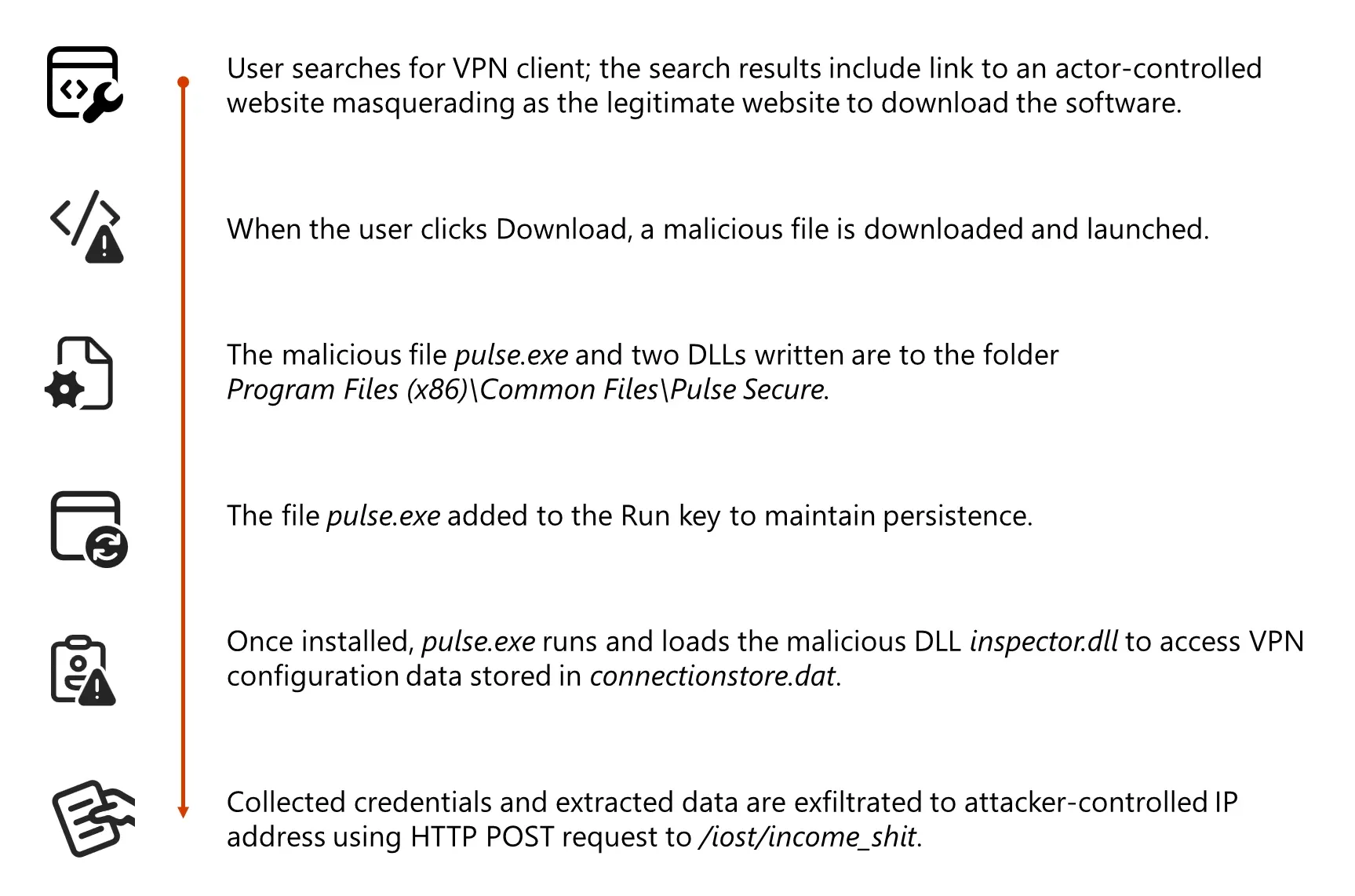
Storm-2561 ops: Microsoft's security team says the Storm-2561 has been running SEO-poisoning campaigns to distribute malware-laced VPN clients. The campaign has been live since May of last year.
Security researcher behind PhantomRaven campaign: An alleged security researcher is behind a massive wave of malicious npm packages. More than 210 packages have been linked to this campaign since October of last year. According to Endor Labs and Koi Security, the packages clearly cross the line between security research into malware territory. They collect extensive data about the infected environments, such as configuration files, credentials, and CI/CD tokens. They also don't disclose that they are part of a security research project in any way and the researcher routinely rotates accounts and email addresses.
More InstallFix campaigns: Bitdefender, Kaspersky, and ThreatBook look at the influx of new InstallFix campaigns out in the wild. These are malicious web pages that contain instructions for installing AI agents like Claude and OpenClaw but secretly deploy malware on the user's devices.
DPRK remote IT worker schemes: If you wanna deal with the browser auto-translate errors, South Korean security firm Logpresso has a pretty good report on North Korea's remote IT worker schemes.
More sanctions on DPRK IT workers: And speaking of the devil, the US imposed more sanctions on North Korean individuals and companies involved in these schemes.
New daisy-chaining RMMs technique: Threat actors have abused remote monitoring and management (RMM) tools for a while, but Huntress is seeing new campaigns where attackers are daisy-chaining different RMM tools, jumping from one to another to "fragment telemetry, distribute persistence, and complicate attribution and containment efforts."
Abuse of Telegram bots: A new Cofense report looks at how various infostealers and RATs are abusing Telegram bots for C2s and data collection.
"Due to its flexibility and ease of use, the Telegram Bot API can be used on virtually any webpage or malicious program capable of making web requests. Some common ways threat actors use the Telegram API include directly making HTTPS requests from executing a malicious script, sending credential phishing form data upon submitting the form, or alerting the threat actor that a victim visited a malicious embedded link payload upon loading the site."
Malware technical reports
RCtea botnet: China's CERT team has detected a new DDoS botnet named RCtea targeting IoT gear. The botnet emerged in December of last year.
RondoDox botnet reaches 174 exploits: A botnet that burst on the scene last year has now reached an arsenal of 174 exploits it uses to breach into systems. That's quite an impressive number. Bitsight suspects the botnet might be used as the backbone of a residential proxy provider.
BlackSanta EDR killer: Aryaka's Aditya K Sood has uncovered BlackSanta, a new EDR killer that's being used in live malware campaigns.
Falcon: Russian security firm F6 has spotted new versions of the Android banking trojan Falcon. The trojan was first spotted in 2021 and is one of the many versions that spun out of the Anubis trojan code.
PixRevolution attacks: Zimperium looks at attacks against Pix users in Brazil where crooks are using the Revolution RAT to intercept Pix payments and hijack money to their own accounts, similar to crypto-clipboard hijackers work.
Venon: Speaking of Brazil and its unique financial system, ZenoX has spotted a new Windows banking trojan targeting the country, coded in Rust, and named Venon.
Remcos RAT: Trellix looks at a recent campaign spreading fileless versions of the Remcos RAT.
HellsUchecker backdoor: Malware analyst Kirk, from Derp.ca, looks at HellUchecker, a new backdoor delivered via ClickFix campaigns.
"HellsUchecker is a 28 KB native x64 backdoor that sits at the end of a 10-stage attack chain. It starts with a ClickFix lure – a fake Cloudflare CAPTCHA – and ends with a memory-resident PE that checks in to its C2 server over HTTPS. Between those two points: a Windows LOLBin delivers the first payload over the finger protocol on port 79, a smart contract on BNB Smart Chain stores the encrypted C2 configuration, and a custom block cipher with aPLib compression unpacks the final binary entirely in memory."
Tranium wiper: Kirk also looks at Tranium, a new Go-based wiper that was misidentified in some places as ransomware.
MicroStealer: Also a new malware strain found this week is MicroStealer, an infostealer documented by ANY.RUN.
VIP Keylogger: K7 has a report on a phishing campaign delivering the VIP Keylogger.
Tengu ransomware: Threat intel analyst Rakesh Krishnan has published a report on the Tengu ransomware, a group that recently rebranded as Shisa. When I visited the Shisa leak site today after I read Rakesh' report, there was a suspicious "Tengu panel source code leak" post but the leak was dead.
Clicking this gave me a 404 and then the post disappeared altogether There's something weird going on on the Shisa/Tengu ransomware leak site right now
— Catalin Cimpanu (@campuscodi.risky.biz) 2026-03-12T14:06:18.985Z
Sponsor section
In this Soap Box edition of the podcast, Patrick Gray chats with Thinkst Canary founder Haroon Meer about his "decade of deception."
APTs, cyber-espionage, and info-ops
War APTing: Proofpoint looks at the influx of APT campaigns targeting Middle East countries since the US and Israel attack on Iran. This doesn't include Iranian groups, but also APTs from China and Belarus alike, showing how foreign governments rush to acquire intelligence the moment a military conflict starts.
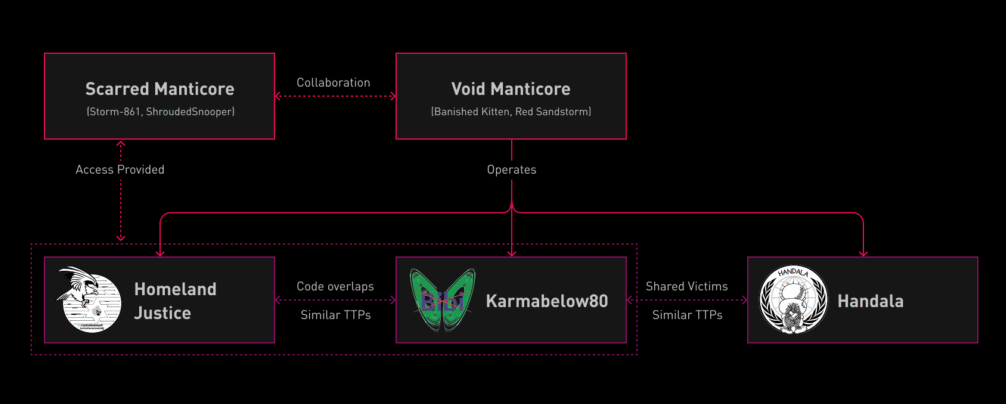
Handala Hack profile: Check Point has published a profile and common TTPs for Handala Hack, a hacktivist group linked to the Iranian MOIS. Handala is allegedly one of the many hacktivist personas managed by Void Manticore (aka Red Sandstorm, Banished Kitten).
Pro-Ukraine cyber activity goes down in Russia: Rostelecom's security team reported in its yearly report that cybersecurity incidents linked to pro-Ukrainian activity have gone down from 70% in 2024 to barely 25% last year.
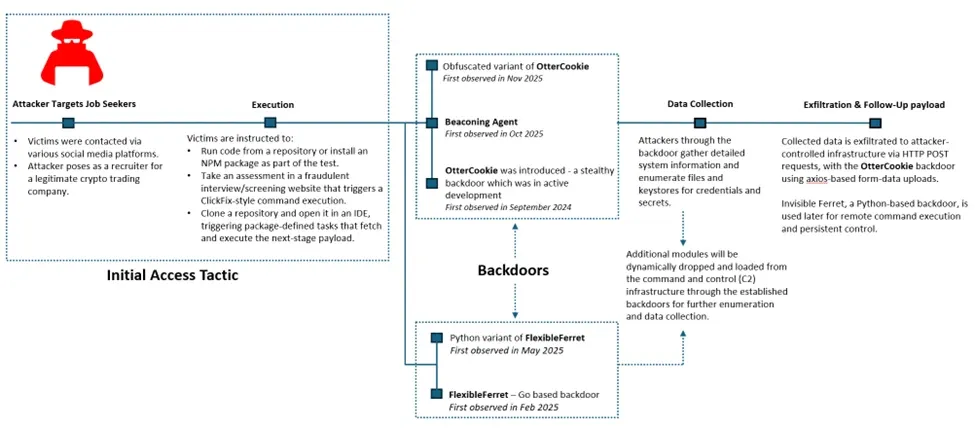
Contagious Interview: Another Contagious Interview report, this time from Microsoft. There are so many of these reports that you'll think North Korea just runs fake job ads all day. Actually, nevermind! They probably do.
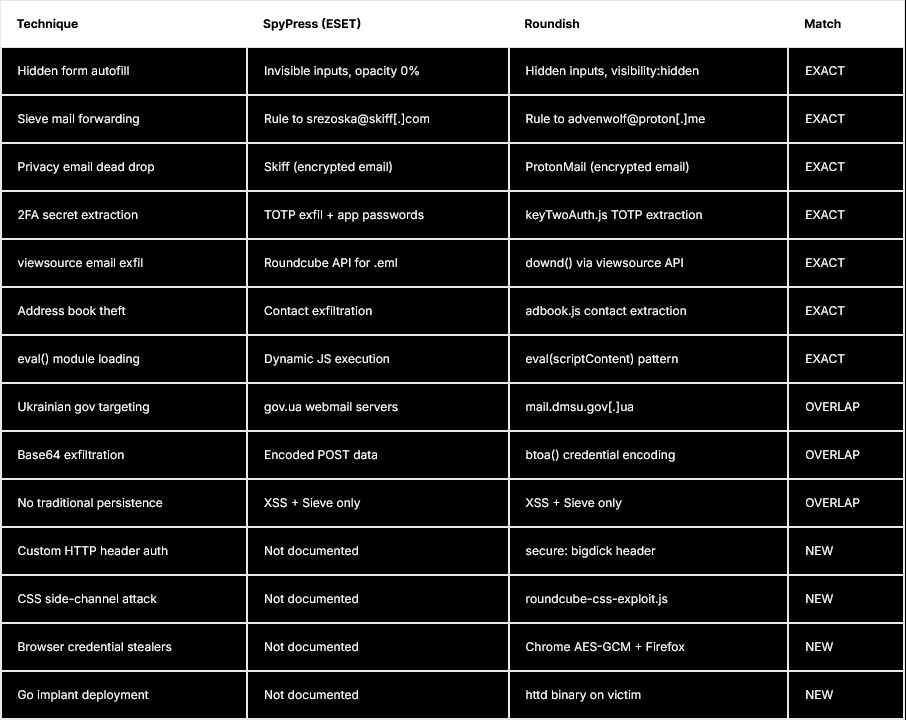
APT28 leaks Roundcube exploit kit: Russian cyber-espionage group APT28 has leaked its exploit kit for hacking Roundcube email servers. The kit was found in an open directory by security firm Hunt Intelligence. It contained payloads, C2 components, and operator artifacts. The payloads enabled credential harvesting, persistent mail forwarding, bulk email exfiltration, address book theft, and 2FA secret extraction. They also found a previously undocumented module that enabled browser credential theft. Hunt found links tying the exact exploit kit to past APT28 campaigns discovered by security firm ESET.
Vulnerabilities, security research, and bug bounty
Apple security updates: Apple has released security updates for older iOS versions to patch exploits used by the Coruna iOS hacking framework. Updates are available for iOS 15 and 16. Patches for iOS 17 were released in December. Coruna is an exploit kit for hacking iOS devices developed by American defense contractor L3Harris. It is thought to have leaked after a former employee sold it to a private Russian exploit broker.
Cisco security updates: Cisco has released four security advisories for various products.
n8n exploitation: CISA says that a December 2025 bug (CVE-2025-68613) in n8n is now being exploited in the wild. Expect more of these to come under attacks since n8n has been patching some spectacularly bad bugs in recent weeks.
Simple-Git RCE: CodeAnt has found a bypass of two previous patches in the Simple-Git npm package that re-enables an old RCE vector.
Azure Arc LPE: Cymulate has published a technical write-up (CVE-2026-26117) on an LPE its researchers found in the Windows client of Azure Arc. This was patched this month.
"A chain of vulnerabilities in Azure Arc agent services for Windows lets a low-privileged user hijack service communications, impersonate the machine’s cloud identity, escalate to NT AUTHORITY\SYSTEM and even trick it to connect to an attacker-controlled tenant instead."
Zombie ZIP vulnerability: Security researcher Christopher Aziz of Bombadil Systems has discovered a new technique to create malicious ZIP files that can bypass EDR and security tools.
AgenticBlabbering: Guardio has described AgenticBlabbering, a term it uses to describe all the internal traffic that takes place inside an AI browser before a web page is delivered to a user. The company argues that this entire process could be abused by threat actors to bypass the browser's internal defenses and route users to online scams and other dangerous pages.
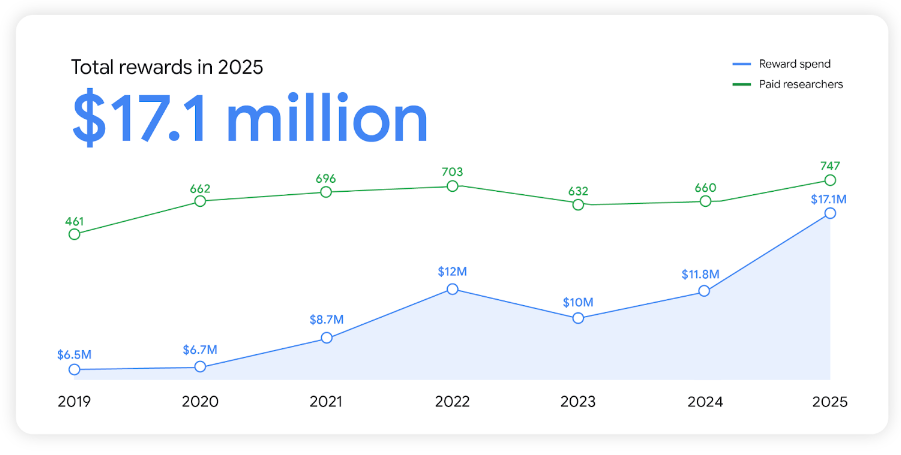
Google bug bounty: Google paid more than $17 million to security researchers last year for vulnerability reports. The payouts reached an all-time high, a 40% increase to the previous year. More than half of the payouts went to Google's Android, Chrome, and Cloud bug bounty programs. Since its inception in 2010, Google has paid over $81.6 million for vulnerability reports.
Infosec industry
Threat/trend reports: Cato Networks, DryRun Security, Flashpoint, Netscout, Positive Technologies, and Rostelecom have recently published reports and summaries covering various threats and infosec industry trends.
Logpoint rebrands: Danish security firm Logpoint has rebranded as Guardsix.
Google closes Wiz deal: Google has formally closed its Wiz acquisition. Now, for the fun part. Let's see what Google does with it.
Kaspersky cuts staff in France: Russian security firm Kaspersky has cut staff at its French subsidiary after losing almost a third of revenue last year. [L'Informe] [h/t Gabriel Thierry]
New ENISA guide: The EU's cybersecurity agency has released guidance on the proper and safe use of package managers.
New tool—Dev Machine Guard: Step Security has open-sourced Dev Machine Guard, a tool to scan your dev machine for AI agents, MCP servers, IDE extensions, and other suspicious packages.
Black Alps 2025 videos: Talks from the Black Alps 2025 security conference, which took place last November, are available on YouTube.
Disobey 2026 videos: Talks from the Disobey 2026 security conference, which took place in Helsinki in mid-February, are now available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the newly released Trump Cyber Strategy for America. The ideas in it are fine and occasionally even game-changing, but many of its goals have been undercut by the administration's actions to date.
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about why an internet shutdown won't stop US cyber operations in Iran.
