Risky Bulletin Newsletter
February 23, 2026
Risky Bulletin: AI-driven hacking campaign breaches 600+ Fortinet devices
Written by

News Editor
This newsletter is brought to you by Socket, a developer-first security platform that prevents vulnerable and malicious open-source dependencies from infiltrating software supply chains. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
A Russian-speaking financially motivated threat actor has used commercial AI toolkits to hack more than 600 Fortinet firewalls.
The campaign began at the start of the year, around January 11, according to the AWS security team.
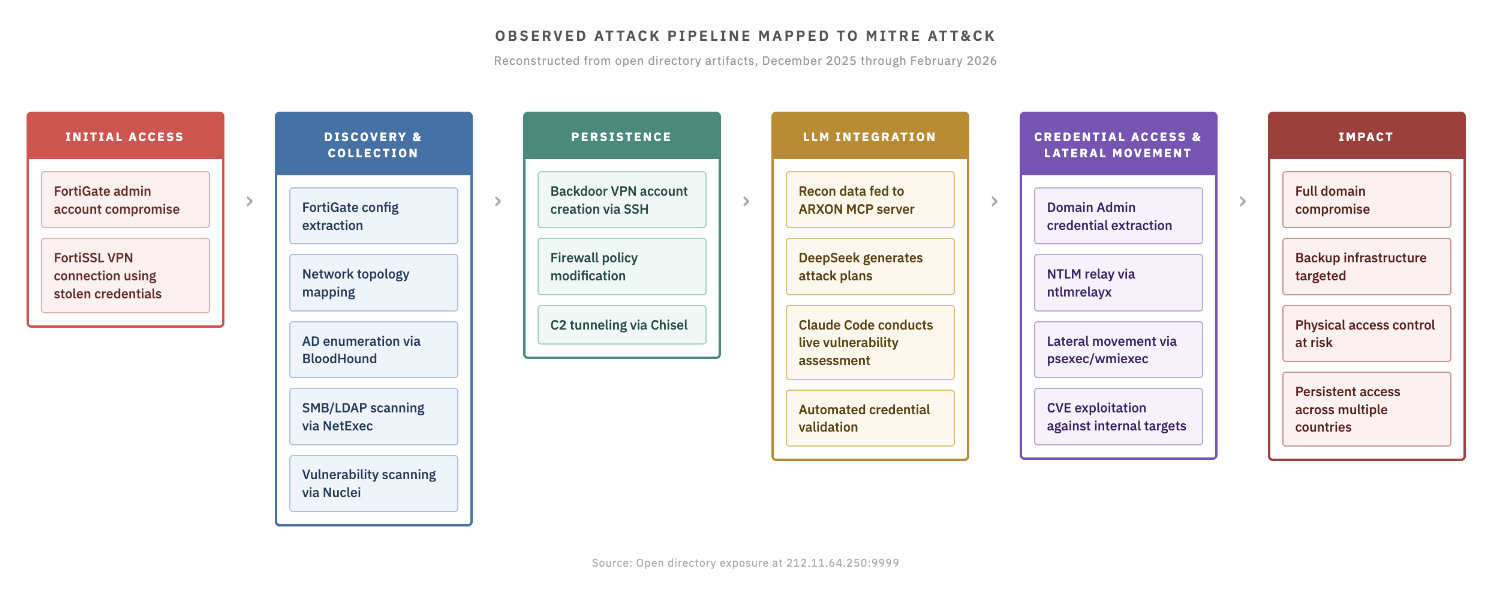
The attacker didn't exploit zero-days or older vulnerabilities. Instead, they targeted FortiGate devices that had their management ports exposed online, used weak passwords, and didn't have MFA enabled.
Once inside, he used a collection of scripts that AWS says were written by AI tools. While AWS didn't name any products, researchers from Cyber and Ramen and Ctrl-Alt-Int3l tracked them down to Claude and Deepseek.
DeepSeek was used to create scripts to perform reconnaissance and extract configurations from the hacked devices while Claude was used to generate scripts for vulnerability assessments and to run offensive tools against the networks.
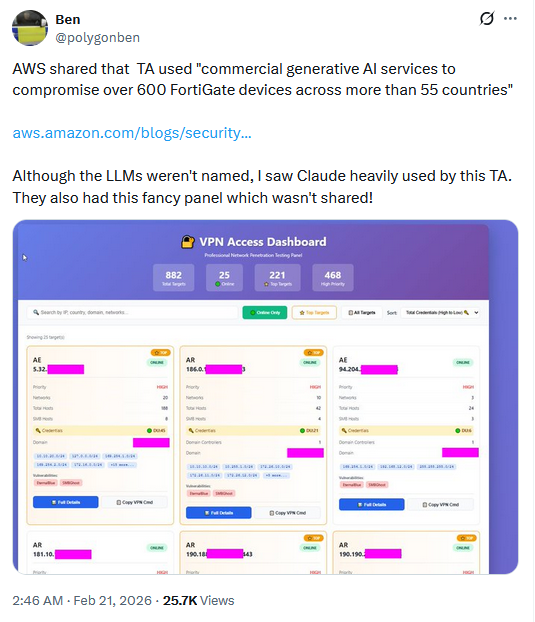
Since we're talking about AI and infosec, the report generated a tornado of feedback and opinions on social media. The general consensus was that the threat actor wasn't particularly sophisticated, which AWS also believes.
AWS CISO CJ Moses said the attacker was more interested in scale rather than value. Every time they encountered errors caused by hardened or non-standard internal networks, the attacker moved on to softer targets.
Once they did move laterally from the Fortinet device, the attacker compromised the victim's Active Directory environment, extracted database credentials, and tried to gain access to backup infrastructure.
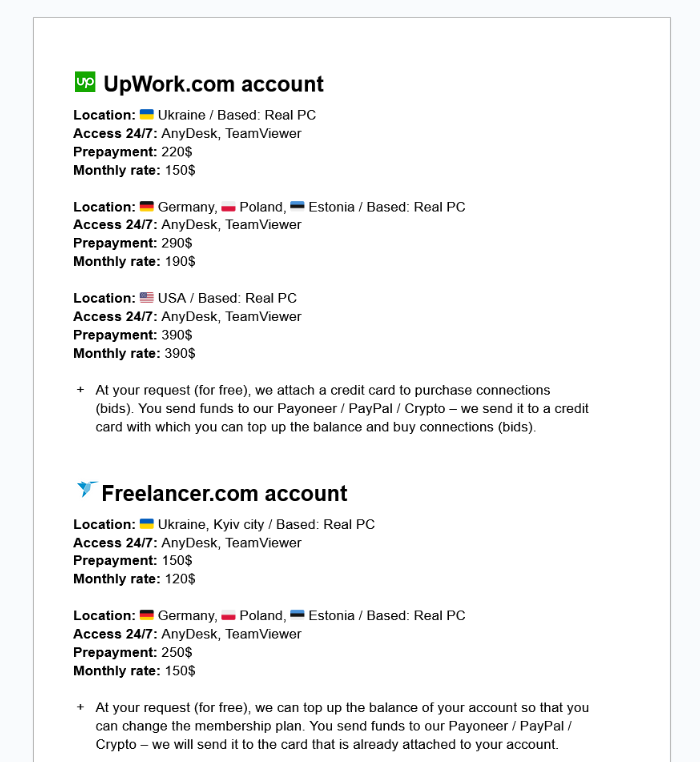
All of this made everyone believe the threat actor was one of those low-skilled initial access brokers (IABs) that gain initial footholds on corporate environments and sell access to the hacked network on underground portals, which is a fair opinion to have based on the available evidence.
From the Cyber and Ramen blog post, which claims this campaign actually started in December when the attacker was still in early phases of experimentation.
"The significance of this operation is not reliant on any single technique. Every tool observed, from BloodHound to Nuclei, and Impacket is well documented. What sets this activity apart is the integration of LLMs: a (likely) single operator managing simultaneous intrusions across multiple countries with analytical support at every stage."
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Ivanti hacked in 2021 via its own product: Chinese hackers have breached Ivanti's internal network in a previously unreported data breach in 2021. According to Bloomberg, the attackers exploited a vulnerability in Ivanti's own Secure Connect VPN product and gained access to the company's California data center. Ivanti said the hackers didn't reach its internal network. The hacks were part of a campaign that also targeted US and European military contractors.
China hacks DIGOS: Chinese state-sponsored hackers have breached the Italian police's special investigations and operations division (DIGOS). The intruders allegedly stole a list with the names of more than 5,000 DIGOS police officers. Officials said data on active investigations was not accessed. They believe the hackers were after data on Chinese dissidents living in Italy. [La Repubblica // AFP]
PayPal had a data leak: A bug in a PayPal loan application exposed customer data for almost six months. The leak began at the start of July last year and was closed in December. It exposed data such as customer names, emails, phone numbers, addresses, and Social Security numbers. PayPal claims that despite the bug the bug exposed the details of only 100 customers. [BleepingComputer]
Advantest ransomware attack: Japanese company Advantest, a maker of test equipment for the semiconductor industry, has fallen victim to a ransomware attack. [The Record]
Skimmer incident: SanSec says it found an active web skimmer on the site of a global supermarket chain. The security firm didn't publish the victim's name since the skimmer was still active but described it as having €100 billion in annual revenue and over 10,000 stores across 25 countries.
Wikipedia bans ArchiveToday for DDoS attacks: Wikipedia has blacklisted the ArchiveToday domain. The site had allegedly altered page snapshots to add the link of a blog they had a dispute with. This caused an indirect DDoS attack against the blog. Wikipedia will be replacing almost 700,000 links going to ArchiveToday, also known as Archive[.]is.
In light of recent revelations that Archive(dot)today is involving its users in a DDOS attack, and altering archives to further a personal grudge, I am ceasing use of the site. I also did three quick tests of alternatives for on-demand archiving, summarized below... arstechnica.com/tech-policy/...
— Conspirador Norteño (@conspirator0.bsky.social) 2026-02-21T17:13:28.089Z
General tech and privacy
Microsoft recommends against OpenClaw: Microsoft has warned against running OpenClaw AI agents on both personal and enterprise workstations. The company security team says OpenClaw should be deployed only via dedicated virtual machines. Alternatively, via systems physically separated from normal workstations.
Samsung Weather App fingerprinting: The Samsung pre-installed weather app is fingerprinting its users. A test of 42 Samsung devices found that the fingerprints were unique per device and survived IP changes across providers and VPN use. Some fingerprints repeated but only for users who saved a single location in the app. Users with two or more saved locations had a globally unique fingerprint.
Political censorship of Chinese LLMs: A new academic paper looks at the high levels of political censorship in Chinese-made LLMs.
Government, politics, and policy
Arizona wants age verification on every app: Arizona lawmakers have proposed a bill that would require all mobile apps to verify the age of their users. The proposed law would apply to both apps downloaded on the device through an app store but and apps that are bundled with the device. In the most extreme case, a phone's pre-installed clock or weather app would not work until the device owner verifies their age. Under the bill, all minor accounts would be required to have an associated parent device and obtain their consent before using apps. [Reclaim The Net]
Predatorgate trial decision: A Greek court is expected to issue a ruling in a trial over the government's use of the Predator spyware. The decision is expected this week, on Thursday, February 26. [in.gr] [h/t Vas Panagiotopoulos]
French national strategy document: France has published its national strategy to combat information manipulation for the next half-decade. The document's pillars are:
- Mobilize the nation to build resilience
- Regulating online platforms and generative artificial intelligence service
- Strengthen the national operational capacity to combat foreign digital interference
- Ensure, with our allies, the existence of a free, open and secure informational space
Sponsor section
In this Risky Business sponsor interview, Casey Ellis and Feross Aboukhadijeh discuss how AI is affecting open source, chat about a few attacks the company has seen in the wild and introduce Socket’s answer to the smouldering trashfire: Socket Firewall.
Arrests, cybercrime, and threat intel
Another DPRK laptop farmer sentenced: The US has sentenced a Ukrainian national to five years in prison for running laptop farms for North Korean IT workers. Oleksandr Didenko paid Americans to receive and host laptops at their homes. He then sold access to the laptops and their identities via the Upworksell.com portal. According to the Justice Department, he operated three US-based laptop farms that hosted as many as 871 proxy identities.

Scam center dismantled in Nigeria: Nigerian authorities have arrested seven suspects who ran a cyber scam center in the city of Agbor. The group used social media ads to lure victims on their fake crypto investment portals. The suspects were detained with the help of UK police and Facebook.
ATM jackpotters indicted: The US has indicted six more suspects for ATM jackpotting crimes. The DOJ claims they are connected to the Tren de Aragua gang. So far, the US has indicted 93 TdA members on ATM jackpotting crimes over the past half year.
Romanian IAB pleads guilty: A Romanian national pleaded guilty to hacking and selling access to the computer networks of American companies. One of his victims was an Oregon state government office in 2021. Catalin Dragomir made at least $250,000 as initial access broker until he was arrested in November 2024. He faces up to seven years in prison.
Engineers arrested for IP theft: US authorities have arrested three engineers from Silicon Valley for stealing trade secrets from Google and other US tech companies. Two sisters, Samaneh and Soroor Ghandali, as well as a 40-year-old man named Mohammadjavad Khosravi were detained on Friday. The three stole sensitive information about processor security and cryptography and accessed the data while they were in Iran.
IMSI catcher case in France: ZDNet France journalist Gabriel Thierry has live-posted from the trial of eight individuals accused of using an IMSI catcher to send waves of spam.
Bonjour, Reprise de ce live-skeet avec le deuxième jour d'audience de l'affaire dite de l'IMSI Catcher qui va bientôt débuter.
— Gabriel Thierry (@gabrielthierry.bsky.social) 2026-02-19T13:11:33.417Z
Russian crypto-exchanges: Elliptic looks at five Russian cryptocurrency platforms involved in helping Russia evade international sanctions.
LonTalk changes: Claroty warns of new cybersecurity risks as the LonTalk building management system protocol is moving to IP-based communications.
BeyondTrust attacks: Palo Alto Networks has published IOCs from recent attacks on BeyondTrust devices, attacks that deployed malware such as VShell and SparkRAT. According to CISA, the bug is now also used in ransomware attacks as well.
Facebook malvertising: Malwarebytes has spotted a Facebook malvertising campaign spreading fake Windows 11 downloads that deploy infostealers.
Malicious npm package: Veracode researchers have spotted a malicious npm package that employed steganography to download and deploy the Pulsar RAT. jFrog also found one of these things, but this one targeting macOS users with a RAT.
New hacker forum: Security researchers have found a new hacking forum named LegionNull. The forum is for Turkish-speaking users and centered around data leaks and data trades.
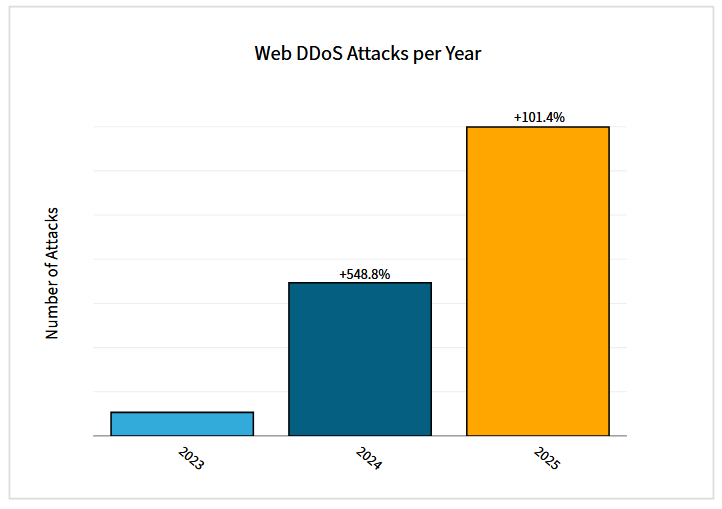
DDoS attacks doubled last year: The number of web DDoS attacks (101%) and bad bot (91%) activity doubled in 2025 compared to the previous year and way way above 2023's numbers, according to Radware's early threat report.
Malware technical reports
SANDWORM_MODE: A new worm is spreading on the npm package repository. The worm was spotted in 19 libraries across two developer accounts. Once installed, these packages exfiltrate a victim's credentials and then spread to other other npm packages if the victim maintains any. Socket Security named it SANDWORM_MODE, due to its similarities to the Sha1 Hulud npm worm from last year.
Winos 4.0 campaign targets Taiwan: Fortinet has spotted a campaign spreading the Winos 4.0 RAT, aka ValleyRAT, to individuals in Taiwan. The phishing emails pose as local tax authorities. Fortinet described the campaign as massive.
CharlieKirk Grabber: A new infostealer named CharlieKirk Grabber, or KirkG, has been open-sourced on GitHub.
MIMICRAT: Elastic has spotted a new C++-based RAT named MIMICRAT being delivered via ClickFix campaigns.
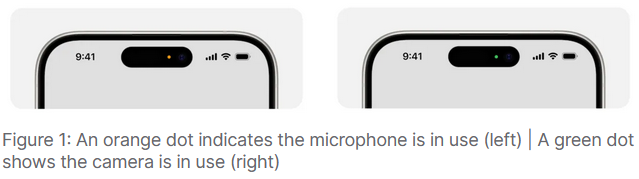
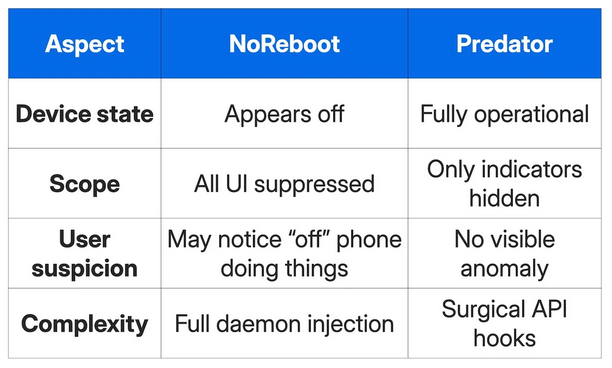
Predator can hide camera and mic indicators: The Predator spyware can hide camera and microphone indicators on an iPhone's screen to enable silent recording. Unlike previous open-source exploits that achieved the same result, Predator can disable the indicators while leaving the rest of the screen UI active. The spyware was developed by a company known as Intellexa, previously Cytrox.
Sponsor section
In this Soap Box edition of the Risky Business podcast Patrick Gray chats with Socket founder Feross Aboukhadijeh about how to measure the reachability of vulnerabilities in applications. It's great to know there's a CVE in a library you're using, but it's even better if you can say whether or not that vulnerability actually impacts your application.
APTs, cyber-espionage, and info-ops
MuddyWater's Operation Olalampo: Group-IB has documented a new MuddyWater APT campaign that employs new malware. This includes a Rust backdoor dubbed CHAR, an advanced backdoor called GhostBackDoor, and two downloaders named GhostFetch and HTTP_VIP.
Cloud Atlas: Rostelecom's security team looks at a Cloud Atlas spear-phishing campaign targeting Russian organizations.
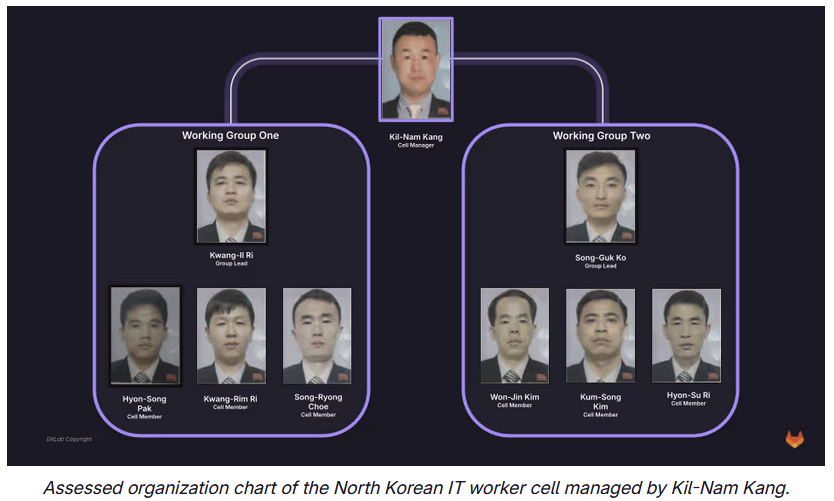
Contagious Interview: GitLab's security team has published a "year in review" report on how North Korean hackers abused its services for Contagious Interview campaigns. The report also takes a deep dive into one of the clusters, which GitLab linked to a North Korean manager named Kil-Nam Kang.
Vulnerabilities, security research, and bug bounty
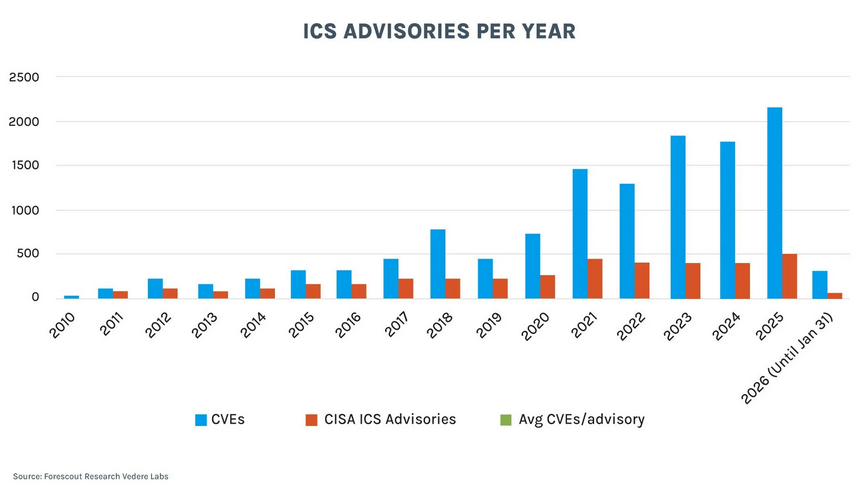
ICS vulnerabilities on the rise: Vendors published 508 security advisories for ICS equipment last year, the most of any year since CVEs started being published. Over 82% of the advisories were for high or critical severity bugs. CISA tracked and notified federal agencies of only a fifth of last year's ICS vulnerabilities, according to Forescout.
Security updates: ABB, AMD, Apache Camel, Atlassian, Cisco Splunk, Moodle.
RoundCube exploitation: Hackers are exploiting two new vulnerabilities to gain access to RoundCube webmail servers. The vulnerabilities include an unsecure deserialization issue and a cross-site scripting bug. Both were patched last year. Although no details about the attacks are available, Russian state-sponsored hackers have been behind several hacking campaigns targeting RoundCube servers over the past four years.
Firefox RCE: A simple one character typo in the Firefox source code exposed the browser to remote code execution attacks. The issue was discovered by security researcher Alessio Ghidini and fixed in Firefox Nightly 149, before it made it into the main browser branch. The typo was an ampersand character (&) being used instead of a pipe (|), causing incorrect data to be stored into memory.
MS-EVEN RCE: SafeBreach researchers have published a write-up on CVE-2025-29969, a remote code execution vulnerability in Microsoft Windows MS-EVEN, a protocol for reading events in both live event logs and backup event logs on remote computers.
Bounty offered to de-Amazon Ring cameras: The Fulu Foundation is offering a $10,000 bug bounty to security researchers to hack Ring cameras and disable their Amazon data sharing feature. The security camera vendor has been under heavy criticism after airing a Super Bowl ad of a new feature that can track lost dogs across all Ring cameras. In a leaked email, the company's management hinted the feature will be soon used for something else, most likely to track individuals as they move through US neighborhoods.
Infosec industry
Threat/trend reports: Barracuda, Cisco, Forescout, Radware, and Red Canary have recently published reports and summaries covering various threats and infosec industry trends.
RIP Parmaster: Jason Snitker, known under his hacker pseudonym Parmaster, has passed away.
Axonius layoffs: Security firm Axonius has laid off 40 employees this month. [CTech]
New ENISA guide: ENISA, the EU's cybersecurity agency has published a guide for how to plan, run and evaluate a cybersecurity exercise.
New tool—RedAmon: Software researcher Samuele Giampieri has released RedAmon, an AI-powered agentic red team framework.
New tool—Bagel: Boost Security published Bagel, a cross‑platform CLI that inspects developer workstations and laptops for risky configurations and settings.
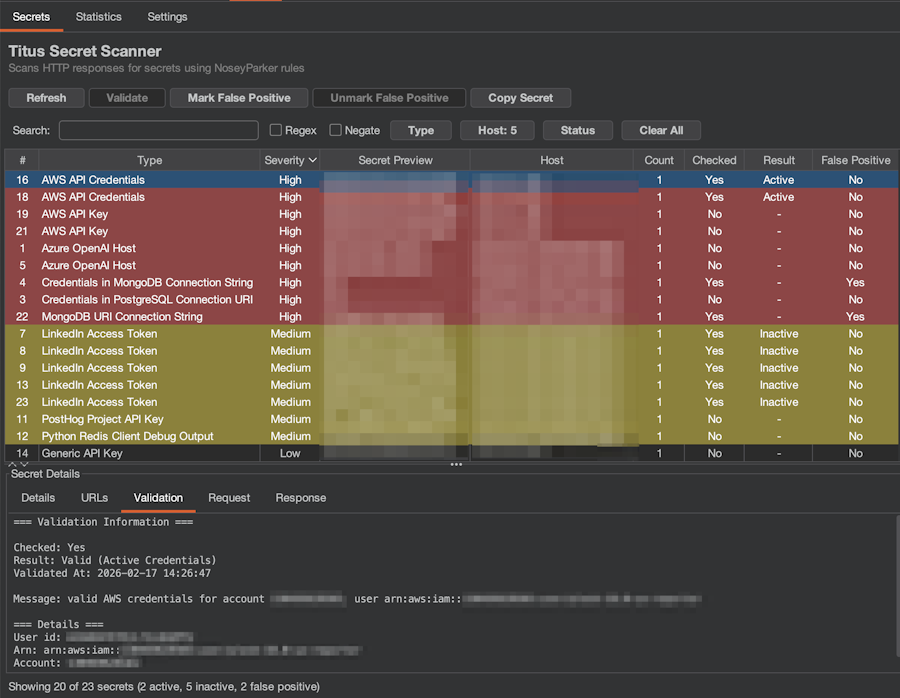
New tool—Titus: Security firm Praetorian has open-sourced Titus, a security scanner available as a CLI tool, Go library, Burp Suite extension, and Chrome extension.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about a groundswell of calls from officials that European countries need to build cyber capabilities to strike back against adversaries. They also talk about 'distillation attacks' the way that AI developers can steal the secret sauce of advanced models just by asking questions.
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss whether middle powers should be investing in military cyber capabilities.
